FIPS 140 (“Federal Information Processing Standard”) is a series of security standards published by the U.S. government that specify security requirements for the evaluation of cryptographic modules. FIPS 140-3 is the newest version; this iteration of FIPS has necessary changes related to the design, implementation, and operation of a cryptographic module.
What is FIPS 140-3?
FIPS 140-3 is a standard developed by the National Institute of Standards and Technology (NIST) and Communications Security Establishment Canada (CSEC) to define the requirements to be satisfied by a cryptographic module to protect sensitive information.
FIPS 140-3 supersedes FIPS 140-2 and outlines updated federal security requirements for cryptographic modules. The new standards align with ISO/IEC 19790:2012(E) and include modifications of the Annexes that are allowed by the Cryptographic Module Validation Program (CMVP), as a validation authority.
FIPS 140-3 became effective September 22, 2019, permitting CMVP to begin accepting validation submissions under the new scheme beginning September 2020. The CMVP continues to validate cryptographic modules to Federal Information Processing Standard (FIPS) 140-2 Security Requirements for Cryptographic Modules until September 22, 2021.
Status of FIPS 140-2
FIPS 140-2 modules can remain active for 5 years after validation or until September 21, 2026, when the FIPS 140-2 validations will be moved to the historical list. Even on the historical list, CMVP supports the purchase and use of these modules for existing systems. CMVP recommends purchasers consider all modules that appear on the Validated Modules Search Page and meet their requirements for the best selection of cryptographic modules, regardless of whether the modules are validated against FIPS 140-2 or FIPS 140-3.
Transition schedule from FIPS 140-2 to FIPS 140-3
The time of the transition is shown below:
| Date | Activity |
|---|---|
| March 22, 2019 | FIPS 140-3 Approved |
| September 22, 2019 | FIPS 140-3 Effective Date Drafts of SP 800-140x (Public comment closed 12-9-2019) |
| March 20, 2020 | Publication of SP 800-140x documents |
| May 20, 2020 | Updated CMVP Program Management Manual for FIPS 140-2 |
| July 1, 2020 | Tester competency exam updated to include FIPS 140-3 |
| September 21, 2020 | FIPS 140-3 Implementation Guidance CMVP Management Manual for FIPS 140-3 |
| September 22, 2020 | CMVP accepts FIPS 140-3 submissions |
| September 21, 2021 | CMVP stops accepting FIPS 140-2 submissions for new validation certificates |
| September 21, 2026 | Remaining FIPS 140-2 certificates are moved to the Historical List |
Table: Transition schedule
FIPS 140-3 approved Cryptographic Algorithms:
When we say FIPS Approved algorithm, it generally refers to an algorithm or technique that is either specified in a FIPS or NIST recommendation or adopted in a FIPS or NIST recommendation (specified in an appendix or in a document referenced by the FIPS or NIST recommendation).
Block Cipher Algorithms:
Several block cipher algorithms have been specified for use by the Federal Government. The approval status of the block cipher encryption/decryption modes of operation are provided in the below table:
| Algorithm | Status |
|---|---|
| Two-key TDEA Encryption | Disallowed |
| Two-key TDEA Decryption | Legacy use |
| Three-key TDEA Encryption | Deprecated through 2023 Disallowed after 2023 |
| Three-key TDEA Decryption | Legacy use |
| SKIPJACK Encryption | Disallowed |
| SKIPJACK Decryption | Legacy use |
| AES-128 Encryption and Decryption | Acceptable |
| AES-192 Encryption and Decryption | Acceptable |
| AES-256 Encryption and Decryption | Acceptable |
Table: Approval Status of Symmetric Algorithms Used for Encryption and Decryption
Digital Signatures:
Digital signatures are used to provide assurance of origin authentication and data integrity. DSA, ECDSA and RSA are allowed, but only with certain parameters. The transition guidance gives a handy summary, shown below:
| Digital Signature Process | Status |
|---|---|
| Digital Signature Generation | |
| <112 bits of security strength: DSA: (L, N) ≠ (2048, 224), (2048,256) or (3072, 256) ECDSA: len(n) < 224 RSA: len(n) < 2048 | Disallowed |
| ≥ 112 bits of security strength: DSA: (L, N) = (2048, 224), (2048,256) or (3072, 256) ECDSA or EdDSA: len(n) ≥ 224 RSA: len(n) ≥ 2048 | Acceptable |
| Digital Signature Verification | |
| < 112 bits of security strength: DSA32: ((512 ≤ L < 2048) or (160 ≤ N < 224)) ECDSA: 160 ≤ len(n) < 224 RSA: 1024 ≤ len(n) < 2048 | Legacy use |
| ≥ 112 bits of security strength: DSA: (L, N) = (2048, 224), (2048,256) or (3072, 256) ECDSA and EdDSA: len(n) ≥ 224 RSA: len(n) ≥ 2048 | Acceptable |
Hash Functions:
A hash function takes a group of characters (called a key) and maps it to a value of a certain length (called a hash value or hash). The hash value is representative of the original string of characters but is normally smaller than the original.
A hash function is used to produce a condensed representation of its input, taking an input of arbitrary length and outputting a value with a predetermined length. Hash functions are used in the generation and verification of digital signatures, for key derivation, for random number generation, in the computation of message authentication codes, and for hash-only applications.
The Transition guidelines document summarizes when SHA-1, SHA-2 etc. can be used.
| Hash Function | Status |
|---|---|
| SHA-1 | |
| Digital signature generation | Disallowed, except where specifically allowed by NIST protocol-specific guidance |
| Digital signature verification | Legacy use |
| Non-digital signature applications | Acceptable |
| SHA-2 family (SHA224, SHA-256, SHA-384, SHA-512, SHA-512/224 and SHA-512/256) | Acceptable for all hash function applications |
| SHA-3 family(SHA3-224, SHA3- 256, SHA3-384, and SHA3-512) | Acceptable for all hash function applications |
| TupleHash and ParallelHash | Acceptable for the purposes specified in SP 800-185 |
Table: Approval Status of Hash Functions
FIPS 140-2 Vs. FIPS 140-3
| Specifications | FIPS 140-2 | FIPS 140-3 |
|---|---|---|
| Cryptographic Module | The FIPS 140-2 standard (issued 2001) was written with the idea that all modules were hardware modules. Later different types of modules (hybrid, software and firmware) were added and defined in the IG (IGs 1.9, 1.16 and 1.17). | FIPS 140-3 will include the hardware module, firmware module, software module, hybrid-software module, and hybrid-firmware module |
| Cryptographic Boundary | FIPS 140-2 IG 1.9 restricted hybrid modules to a FIPS 140-2 Level 1 validation | There is also no restriction as to the level at which a hybrid module may be validated in the new standard. |
| Roles | The FIPS 140-2 standard (section 4.3.1), requires that a module support both a crypto officer role, and a user role, and the support of a maintenance role was optional. | FIPS 140-3 still has these same three roles, but only the crypto officer role is required (section 7.4.2). The user role and the maintenance role are now optional. |
| Authentication | ISO 19790: Level 1 -no authentication requirements Level 2 – minimum role-based authentication Level 3 – identity-based authentication | ISO 19790: FIPS 140-3 is similar to FIPS 140-2 for authentication at security levels 1-3. Level 4 is also added in FIPS 140-3, For level 4 authentication, it must be multi-factor identity based. |
Table: Approval Status of Symmetric Algorithms Used for Encryption and Decryption
Summary:
FIPS 140-3 has been finally approved and launched as the latest standard for the security evaluation of cryptographic modules. It covers a large spectrum of threats and vulnerabilities as it defines the security requirements starting from the initial design phase leading towards the final operational deployment of a cryptographic module. FIPS 140-3 requirements are primarily based on the two previously existing international standards ISO/IEC 19790:2012 “Security Requirements for Cryptographic Modules” and ISO 24759:2017 “Test Requirements for Cryptographic Modules”.
FIPS 140-3 Timelines:
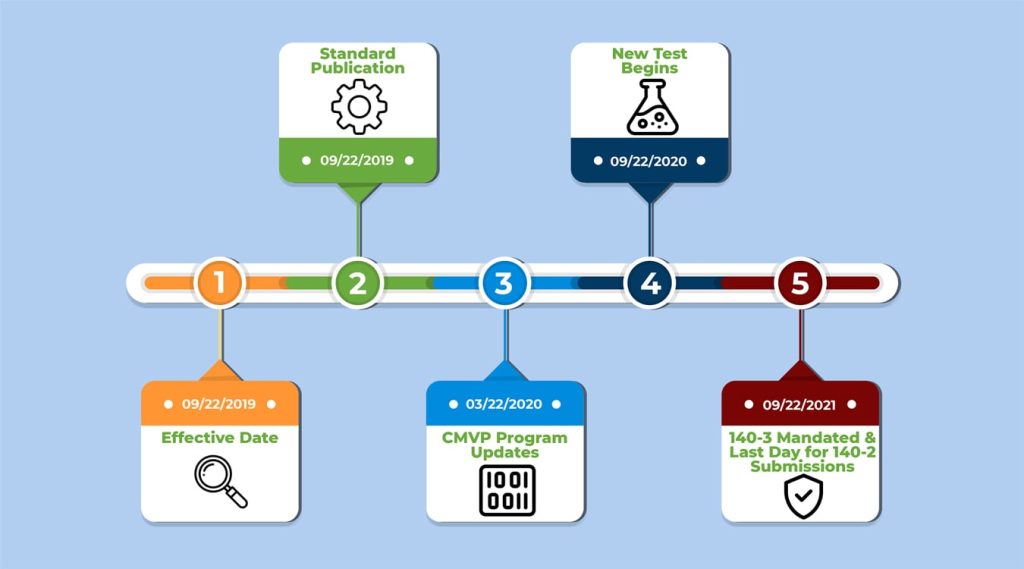
The Timeline: FIPS 140-3 Timelines:
Sources
www.nvlpubs.nist.gov/nistpubs/SpecialPublications/NIST.SP.800-131Ar2.pdf
www.csrc.nist.gov/projects/cryptographic-module-validation-program