- SSL Encryption Fundamentals
- Digital Signatures
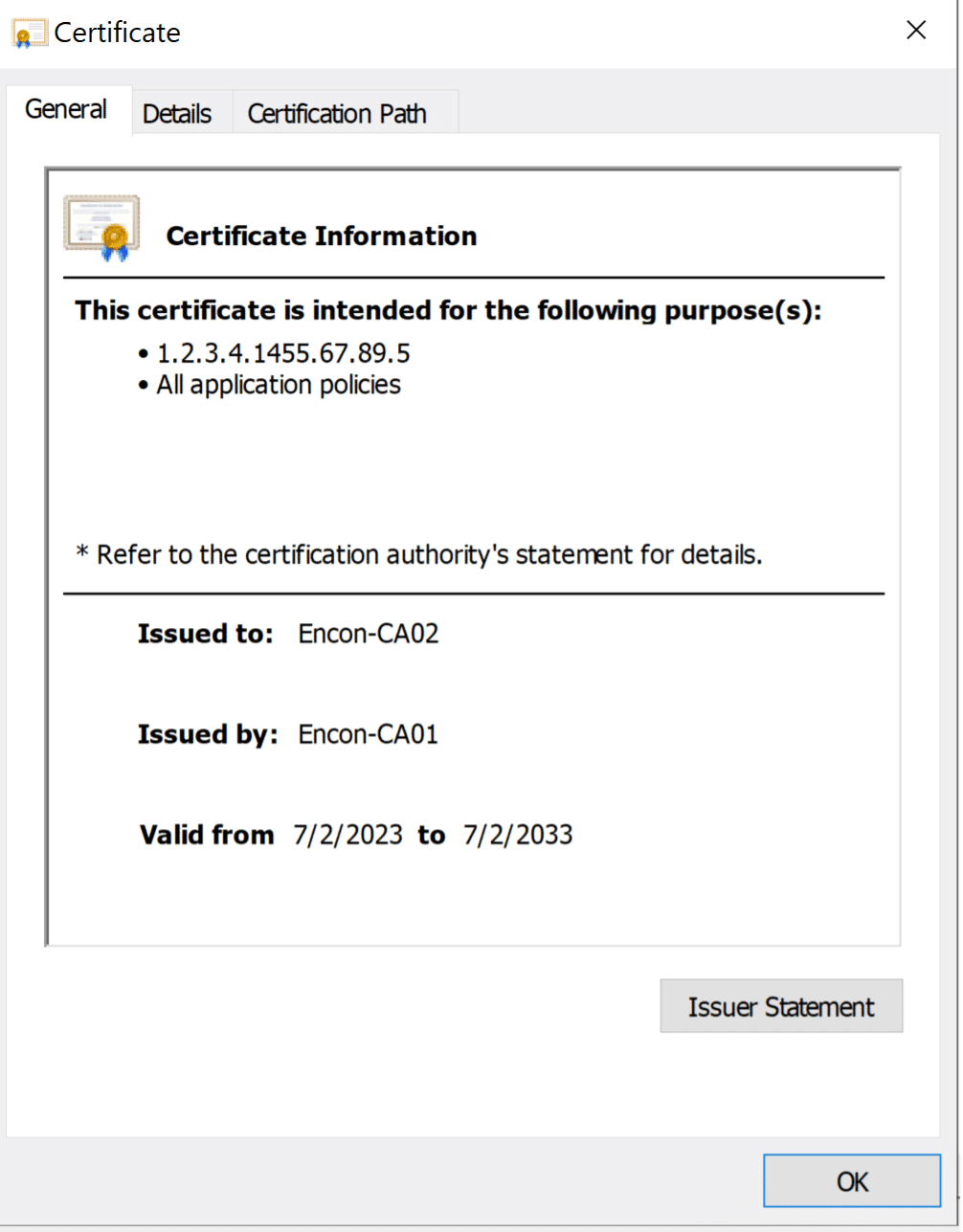
- Navigating Certificate Chains
- The Significance of Certificate Hierarchy
- Managing Trust: The Role of Root Programs in SSL Security
- The Purpose of Intermediate Certificates
- Significance of Intermediate Certificates
- Difference Between the Root Certificate Authority and Intermediate Certificate Authority
- How can Encryption Consulting help?
- Conclusion
SSL Encryption Fundamentals
SSL, or Secure Sockets Layer, operates on the foundation of a private-public key pair arrangement, enhancing digital security. Site data undergoes encryption using a private key, permitting only those with the corresponding public key to access the information. This public key is shared with visitors through a certificate file, which they use whenever they attempt to access the site.
If the site’s certificate is invalid, it signifies inadequate verification and a potential security hazard. Diverse certification levels exist, each with distinct trust levels and validation processes, ensuring varying degrees of reliability.
Certificates are granted by credible certifying authorities. These authorities meticulously examine whether the SSL certificate applicant is authentic. Every certificate has an expiration date, after which it is deemed obsolete and necessitates renewal to sustain SSL protection features.
In essence, SSL assures users that a certifying authority has properly authenticated the site they’re connecting to. SSL’s absence entails compromised encryption and the susceptibility to data breaches.
Digital Signatures
Digital signatures act as digital equivalents of notarization for certificate verification. They bolster the trustworthiness of a specific certificate file, akin to how we authenticate physical documents with a qualified notary. Each element within the SSL certificate chain, whether a certificate or public key, bears a proper digital signature.
SSL websites receive certificates and the associated public keys upon loading in a browser. The browser then leverages these to authenticate the certificate’s validity, scrutinizing the digital signature and its link to the signing certificate. This process extends through the certificate chain until the ultimate certificate is reached.
Navigating Certificate Chains
Certificate chains, also known as chains of trust or certification paths, play a pivotal role in ensuring the secure use of public and private key pairs. Each chain includes various certificates, encompassing the end-user certificate, one or more CA certificates, and a self-signed certificate.
Certification chains boast distinct properties:
- The issuer’s certificate details usually match the next certificate’s subject.
- A secret key to sign the next certificate, excluding the final certificate.
- The last certificate, the trust anchor, usually a CA certificate, ensures the chain’s credibility.
A certificate chain without a valid root certificate link is deemed unreliable, causing the end-user application to distrust the corresponding site.
The Significance of Certificate Hierarchy
SSL certificate chains, or chains of trust, establish links between SSL certificates and trusted CAs. An SSL certificate should be traced back to a legitimate CA to be deemed valid.
Inspecting the certificate of a new website offers insight into the certificate hierarchy. The hierarchy ensures the certificates’ reliability, starting with the root certificate, followed by intermediate CAs, and culminating in a server certificate linked to a valid CA.
Root Certificate
- This is like the top authority in a certificate hierarchy.
- It’s the most trusted certificate and is issued by a highly trusted organization, like a well-known Certificate Authority (CA).
- Think of it as the ultimate boss who says, “I trust this company to issue certificates”.
Intermediate Certificate
- These are like middle managers in the certificate hierarchy.
- They are issued by the Root Certificate but are not as trusted as the Root Certificate itself.
- Intermediate Certificates are often used to help manage and organize the process of issuing lower-level certificates.,/li>
- Think of them as supervisors who help the boss delegate responsibilities.
Server Certificate
- This is the certificate that a website or a server uses.
- It’s issued by an Intermediate Certificate, which, in turn, is trusted by the Root Certificate.
- When your web browser connects to a secure website (with “https://” in the URL), it receives the Server Certificate from the website. Your browser trusts it because it can trace the trust back to the Root Certificate.
- Think of it as the employee ID badge that allows your browser to trust a website and securely communicate with it.
Managing Trust: The Role of Root Programs in SSL Security
Root certificates are paramount for trust chains, validating end-user certificates. Root programs manage root certificates and their public keys within a root store, a location subject to OS or third-party app variations. Major root programs, such as those by Microsoft, Apple, Google, and Mozilla, adhere to stringent CA/B forum baseline requirements and set guidelines for secure implementation.
The Critical Role of Root Certificates in SSL Security
A root certificate stands as the cornerstone of SSL security, holding the power to instill trust across all browsers. Certificates signed with its private key are universally trusted, underscoring the significance of genuine issuance. The root certificate shapes the foundation of trust, elevating a site’s credibility.
A CA undergoes meticulous verifications and compliance procedures to issue root certificates, solidifying its trustworthiness. The root certificate establishes the trust anchor, directly influencing sites relying on the CA’s security certificates.

Attributes of Root Certificates
Root certificates possess unique characteristics that set them apart:
- Extended lifespan of up to 25 years, compared to regular TLS/SSL certificates.
- Diverse root certificates with varying attributes and digital signatures.
- Root certificate validation serves as the basis for other certificates.
The Purpose of Intermediate Certificates
Although a root certificate alone can suffice for SSL security, most CAs employ intermediate certificates due to the practicalities of obtaining the necessary qualifications. Typically, CAs begin by issuing cross-certificates, linking to root certificates from established CAs. Novice CAs might lack the prerequisites to issue root certificates. They resort to established CA services, connecting their certificates to valid root certificates, creating a trust chain. This chain features a trusted root certificate linked to multiple intermediate certificates via cross-certificates, ensuring a valid SSL trust chain.
Once a CA attains validation, it replaces the trust anchor with its root certificates, which enter the root store. Intermediate certificates facilitate a smooth transition from an intermediate CA to a trusted root certificate, assisting emerging CAs in building their user base.
Significance of Intermediate Certificates
Intermediate certificates offer several benefits:
- Control over root certificate proliferation to mitigate security risks.
- Scalable SSL network implementation.
- Enhanced security management during security incidents.
This minimizes the impact of security breaches.
Difference Between the Root Certificate Authority and Intermediate Certificate Authority
Root Certificate Authority (Root CA)
-
Position in Hierarchy
The Root CA stands at the top of the certificate hierarchy, symbolizing the ultimate trust anchor for all certificates within the chain.
-
Self-Signed
CA Root CA’s certificate is self-signed, meaning it signs its own certificate using its private key. This distinguishes it from intermediate CAs that are signed by higher-level CAs.
-
Issuance of Certificates
Apart from issuing and signing intermediate CA certificates, a Root CA is also responsible for issuing and signing end-entity (server or client) certificates. It acts as the root source of trust for the entire chain.
-
Validity and Lifespan
Root certificates typically have longer validity than intermediate certificates. They can remain valid for multiple years, sometimes spanning up to 25 years.
-
Trust Anchor
Root certificates establish the foundation of trust for the entire certificate chain. They are pre-installed in trust stores on various devices and browsers. All certificates in the hierarchy derive their trust from the root.
-
Validity and Lifespan
The security of a Root CA is paramount, as a compromise would undermine the trustworthiness of all certificates issued by it. Thus, rigorous security measures are in place to protect root keys and certificates.
-
Verification and Compliance
Root CAs undergo extensive verification and compliance procedures to ensure their authenticity and security. Due to their central role, the credibility of the entire certificate ecosystem depends on their trustworthiness.
Intermediate Certificate Authority (Intermediate CA)
-
Position in Hierarchy
Intermediate CAs are positioned between root CAs and end-entity certificates, forming a bridge in the trust chain.
-
Signed by Root CA
An Intermediate CA’s certificate is signed by a root CA’s private key. This signature creates the link between the intermediate and the root, establishing a path of trust.
-
Issuance of Certificates
Intermediate CAs are responsible for issuing and signing end-entity certificates. These certificates, commonly used for servers, rely on the trust established by the intermediate’s connection to the root.
-
Validity and Lifespan
Intermediate certificates have a shorter validity period than root certificates. They are renewed more frequently, usually within a few years.
-
Trust Reliance
The trustworthiness of an intermediate CA relies on the chain of intermediates leading back to the root. If any intermediate CA in the chain is compromised, it affects only the certificates issued by that intermediate, minimizing the impact on the entire hierarchy.
-
Enhanced Security
While a compromise of an intermediate CA is still serious, its impact is localized compared to a root CA compromise. This enhanced security allows for more flexibility in managing certificates.
-
Issuer Details
Each intermediate CA’s certificate includes an issuer field that points to the root CA that signed it. This provides a clear lineage of trust from the root to the intermediate to the end-entity certificates.
-
Versatility
Intermediate CAs allow root CAs to delegate the responsibility of certificate issuance. This delegation makes certificate management more scalable and helps new CAs establish themselves in the ecosystem.
-
Certificate Revocation
Individual intermediate certificates can be revoked if compromised without affecting the trust in other parts of the hierarchy. This targeted revocation minimizes disruptions caused by security incidents.
How can Encryption Consulting help?
Encryption Consulting provides a specialized Certificate Lifecycle management solution CertSecure Manager. From discovery and inventory to issuance, deployment, renewal, revocation, and reporting. CertSecure provides an all-encompassing solution. Intelligent report generation, alerting, automation, automatic deployment onto servers, and certificate enrollment add layers of sophistication, making it a versatile and intelligent asset.
Conclusion
Root and intermediate certificates and the web of trust they weave are integral components of secure online communication. Root certificates anchor trust, while intermediate certificates bridge the gap between budding CAs and established roots. Understanding these certificates and their nuances is vital for safeguarding digital interactions and maintaining a secure digital environment.
- SSL Encryption Fundamentals
- Digital Signatures
- Navigating Certificate Chains
- The Significance of Certificate Hierarchy
- Managing Trust: The Role of Root Programs in SSL Security
- The Purpose of Intermediate Certificates
- Significance of Intermediate Certificates
- Difference Between the Root Certificate Authority and Intermediate Certificate Authority
- How can Encryption Consulting help?
- Conclusion

