Building your Encryption Strategy
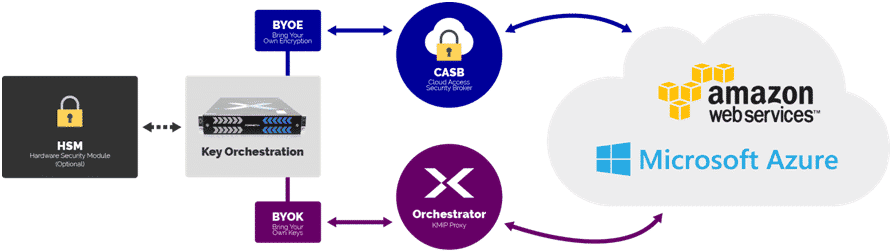
Once overlooked, key management in the cloud is becoming a high priority for CISOs as multi-cloud environments become the next step in the continual goal of reducing downtime. Each major cloud provider has its own internal key manager. Amazon Web Services (AWS) has the AWS Key Management Service tucked away inside the Identity and Access Management (IAM). Azure has the Key Vault to store keys used within its environment. Google has the Cloud Key Management Service. All of them have very different interfaces and offer little control over key sovereignty.
Leverage REST for BYOK
External Key Management services have been slow to address the problem with their focus on the internal data center. Cloud key managers have not been keen to adopt standards such as the Key Management Interoperability Protocol (KMIP). The latest generation of Key Managers, however, is starting to close the gap. By leveraging the REST interfaces provided by cloud providers, Key Managers can enable Bring Your Own-Key (BYOK) functionality at multi-cloud and enterprise scales. Functionally, most Key Managers can support these new use cases through APIs and clients. Migrating to a secure cloud infrastructure requires some research, as BYOK integrations are still emerging.
How to Decide on a Key Management Partner?
There are several questions you should consider before deciding on your key management partner:
- What is your current usage of encryption?
- Where should your organization be using encryption, but not due to complexity?
- How many cryptographic objects will the Key Manager support? Will it be able to scale with the continued growth of your company?
- Does the Key Manager support automation of workloads? With the heavy automation already in your DevOps environment, why introduce a manual bottleneck?
- Does the Key Manager have the integrations for the tools you use?
- Is the Key Manager from a company that can be a trusted partner? Managing your keys is only part of the equation. Encryption keys and certificates manage all of your stored data. You need to ensure your organizational data integrity.
By working with experts, you greatly increase your chances of having a platform that performs and provides the security your organization needs to thrive while still protecting vital data. With the right strategy, encryption of your multi-cloud infrastructure can be integrated into your existing DevOps platforms with ease.
Jon Mentzell is a cybersecurity expert with two decades of systems administration and DevOps experience, including security for a cabinet-level government agency. He is currently the Product Security Manager at Fornetix.
Challenges of Key Management in Multi-Cloud Environments
-
Interoperability Between Cloud Providers
Ability of different cloud platforms like GCP, AWS, etc, to seamlessly work together and manage encryption across multiple providers.
-
Complexity of Key Rotation Across Multiple Cloud Platforms
Security can be enhanced by regularly changing the encryption keys. In a multi-cloud environment, managing key rotation across different platforms can be complex due to varying key management mechanisms and policies.
-
Ensuring Consistency and Synchronization of Keys
Maintaining consistency and synchronization of encryption keys across multiple cloud environments is crucial to ensure data integrity.
-
Compliance with Different Security Standards and Regulations
Different cloud providers may adhere to varying security standards and regulations. Managing keys in compliance with these standards across multiple clouds requires careful planning and implementation to avoid compliance breaches.
How Can Encryption Consulting Help?
With a strong focus on Encryption Advisory services and decades of consulting expertise, Encryption Consulting offers a range of cryptographic solutions. Among these, PKI as a Service (PKIaaS) stands out, providing round-the-clock support to clients for any issues related to their PKI environment. This comprehensive approach enhances security, ensuring organizations remain resilient against potential misconfigurations in their encryption setups.




