CertSecure Manager
Prevent Outages Before They Happen!
Your One-Stop Solution for All Your Digital Certificate Management Requirements.
Webinar: Register For Our Upcoming Webinar
Register NowCertSecure Manager
Your One-Stop Solution for All Your Digital Certificate Management Requirements.
Purpose-built for modern PKI challenges, CertSecure Manager goes beyond certificate management. It gives your organization the visibility, automation, and control needed to stay secure in an increasingly complex cryptographic landscape.
CertSecure Manager is built by PKI and encryption practitioners, with Encryption Consulting's deep advisory expertise embedded into every decision.
CertSecure Manager is built with crypto-agility at its core, helping organizations assess their current cryptographic posture and transition confidently to quantum-safe certificates as standards evolve.
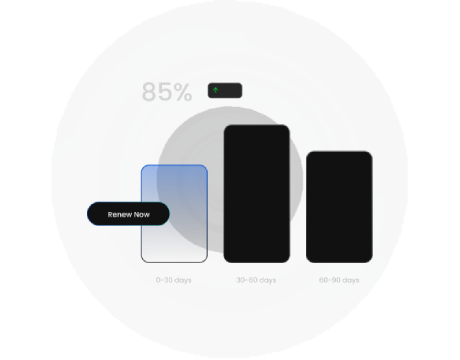
CertSecure Manager automates renewals at scale, keeping pace with the industry's shift to shorter certificate lifespans.
CertSecure Manager generates comprehensive audit trails and high-risk certificate reports on demand, simplifying internal and external audits.
CertSecure Manager continuously scans your environment to detect unknown and rogue certificates, closing gaps attackers exploit.
Digital trust is everything, and certificate management should never be an afterthought.
Automated renewals eliminate expirations and downtime, ensuring continuous security.
Instantly issue, revoke, and renew certificates with automation, adapting quickly to security needs.
Reduce manual effort with centralized management, policy enforcement, and automated certificate workflows.
Seamlessly connect with existing PKI, ITSM, and security tools without disrupting workflows or operations.
Gain complete certificate visibility, track expirations, and automate renewals in one unified dashboard.
Simplify certificate management with automation, security, and seamless integration across your IT ecosystem.
Learn More
Automate
Enforce

Streamline
Effortlessly integrate CertSecure Manager into your existing infrastructure with powerful automation and flexible APIs. Streamline certificate issuance, renewal, and compliance across diverse environments while ensuring security, scalability, and minimal manual intervention.

Enable seamless certificate automation, lifecycle management, and security across diverse infrastructures to mitigate outages, streamline operations, and ensure compliance.


Deploy CertSecure Manager in the environment that best fits your security, scalability, and operational needs. Choose on-premises for full control, cloud for flexibility, SaaS for simplicity, or hybrid for a balanced approach.
Maintain full control and security with an in-house deployment tailored to your infrastructure.
Leverage flexible, scalable deployment with seamless integration into your preferred cloud provider.
Experience hassle-free deployment with a fully managed, cloud-hosted solution for streamlined certificate management.
Combine on-premises control with cloud scalability for a balanced, flexible deployment strategy.
Post Quantum Cryptography
Stop treating your cryptographic inventory as a one-time project. Learn how a living CBOM turns discovery data into compliance evidence, risk prioritization, and a realistic PQC migration plan.
Read more
White Paper
Which NIST post-quantum signature fits your code-signing workflow? Compare ML-DSA, SLH-DSA, and draft FN-DSA variants in one practical reference.
Read more
Video
Explore expert insights on cybersecurity, PKI, and post-quantum readiness, with practical guidance to strengthen security and future-proof cryptography.
Watch Now
Everything you need to know about CertSecure Manager. Can't find the answer you're looking for? Send us an email and we'll get back to you as soon as possible!
CertSecure Manager supports a wide range of certificate types including TLS/SSL certificates, S/MIME email certificates, code signing certificates (OV & EV), and private PKI certificates for devices, servers, and users. It works across Microsoft CAs, Public CAs, and Private CAs, all from a single unified dashboard.
CertSecure Manager automates the entire certificate lifecycle, from issuance to renewal, so certificates never expire unexpectedly. It continuously monitors expiration dates, sends automated alerts, and triggers zero-touch renewals, eliminating the risk of downtime caused by lapsed certificates.
Yes. CertSecure Manager integrates seamlessly with existing PKI, ITSM tools including ServiceNow, and security platforms through industry-standard protocols like REST APIs, SCEP, ACME, and EST. It connects with F5 BIG-IP, Apache, Nginx, IIS, Tomcat and others, and supports DevOps automation through Ansible and other leading tools. For security operations teams, it integrates with Splunk and other observability platforms for centralized alerting and certificate event visibility, and supports Azure Key Vault, Java KeyStore, and other key vault solutions for secure certificate and key storage.
CertSecure Manager offers flexible deployment to match your organization’s needs: On-Premises for full infrastructure control, Cloud for scalability, SaaS for a fully managed hassle-free experience, or a Hybrid model combining both on-premises and cloud. You choose what fits your security and operational requirements.
CertSecure Manager allows you to enforce organization-wide enrollment and security policies, restrict encryption algorithms, and ensure FIPS compliance. You can also define multi-level approval workflows for critical certificate requests and restrict access to Certificate Authorities (CAs) using M of N approval policies.
Absolutely. CertSecure Manager supports DevOps workflows through ACME and REST APIs, enabling automated issuance of both public and private container certificates. It extends discovery and lifecycle management to containers, cloud environments, and HashiCorp Vault, ensuring certificates across modern infrastructure are never out of scope. Ansible playbooks further streamline automation for teams managing certificates across distributed systems.
CertSecure Manager reduces manual IT effort, minimizes costly certificate-related outages, and consolidates certificate management into one platform, cutting operational overhead significantly. You can use the built-in ROI calculator on the product page to get a data-driven estimate based on your organization’s specific environment and certificate volume.
CertSecure Manager delivers a unified Single Pane of Glass experience, giving you complete visibility and control across all certificate types, CAs, and environments in one dashboard. It combines automated lifecycle management, robust policy enforcement, flexible deployment options, and seamless integration with tools like ServiceNow, F5, and DevOps pipelines, eliminating manual effort, preventing outages, and scaling with your organization’s needs.
CertSecure Manager integrates with leading SIEM and observability platforms, including Splunk, Datadog, and OpenTelemetry to stream certificate lifecycle events, expiration alerts, and compliance status directly into your existing security monitoring workflows. This ensures certificate health is visible alongside the rest of your infrastructure telemetry, without requiring security teams to switch between tools.