Why is Ransomware a threat?
Within the framework of society’s structure, the desire for monetary rewards drives cybercriminals to target and obtain valuable data. Generally, this includes personal details, organization information, login credentials, customer information like credit card details, contact info, and other crucial information.
Knowing the absolute worth of data, cybercriminals target it. In an instance of a ransomware attack, the operational capabilities of a company are crippled as cybercriminals encrypt data and potentially restrict device access, demanding payment of a ransom as the condition for unlocking the compromised resources. These attacks not only put user data on display to the world but also breach the principle “Right to Privacy.” Ransomware’s aftermath also devastates organizations, sometimes leading them to close completely, damaging company reputation and user trust.
Not only does it take time and money to rebuild the business functionality back to speed, but only 4% of businesses that pay a ransom retrieve all of their data.
Ransomware behaves differently according to the malware code. Some general types of ransomware behaviours are: –
-
Ransomware-as-a-service (RaaS)
-
Scareware
Deceives user with fake messages of malware infecting the system and prompts the user to remove this malware by downloading the solution mentioned, generally an Antivirus.
-
DDoS extortion
Prompts users to pay the ransom, or the attacker will launch a DDoS attack.
-
Cryptoware
Encrypts important data and demands a ransom to decrypt it.
-
ScreenLocker
Locks the device and demands a ransom to unlock it within a limited time.
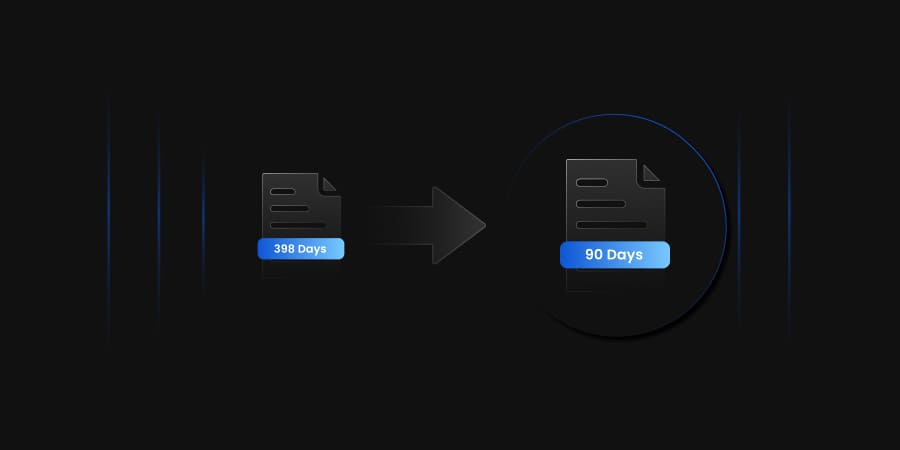
All these attacks put a time restriction on the user and demand ransom payment within a time limit or else destroy the data.
Ransomware-as-a-Service (RaaS)
RaaS is a business model where malware developers lend ransomware to other malicious groups or cybercriminals.
RaaS is a variation of MaaS, Malware-as-a-service, a malicious variant of SaaS, Software-as-a-service. Like SaaS in RaaS, you use malware instead of software.
RaaS is generally used to spread Cryptoware, malware that encrypts data and decrypts it only if the ransom is paid to the organization.
According to a report by Forbes titled “The rise of RaaS,” The average total cost of recovery from a ransomware attack ($1.8 million in 2021) is now 10 times the size of the ransom payment itself ($170,404).
RaaS and its variations
RaaS is generally divided into two main variations:
-
Affiliate programs
This is where the attacker is doing this on behalf of a larger group. They do the encryption and earn a percentage of each successful ransom payment.
-
Outright payment
Ransomware executables are purchased outright and left to their own devices for distribution, infection, and facilitation of ransom payment.
The main catch in RaaS is that even a starter cybercriminal can successfully pull off a ransomware attack on an esteemed organization with the help of RaaS.
Responding to Ransomware attacks
After your organization is hit by ransomware, it does its work of encrypting the files or locking the system, according to the type of ransomware used. The screen displays a message and the instructions for payment. At the same time, ransomware pivots to other systems and tries to do the same.
The following few steps can help you while being under a ransomware attack.
- The first and foremost task at hand would be identifying the system affected.
- Isolating affected systems from the organizational network.
- Identifying and shutting down any backdoors present in the systems.
- If necessary, cut the power supply of the affected systems.
- Call for experts to look into the environment and eradicate the threat present.
Steps to prevent ransomware attacks
Various measures can be taken to prevent ransomware attacks and the following disaster.
- Monitor your server and network and back up key systems. Make multiple backups and store them.
- Emails are the primary source of distributing ransomware attacks. Spearhead phishing, broken into simple terms, targets a particular person who holds substantial influence over the organization.
- Invest in user training and build a culture of security.
- Network segmentation helps to stop the further proliferation of the attack over the organizational network.
- Secure web gateways can scan users’ web surfing traffic to identify malicious web ads that might lead them to ransomware
- Using security tools like Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS).
- Depending on timely Vulnerability assessments and Penetration Testing.
If organizations have followed best practices and made regular backups of the data, the restoration will be quite easy, and no need for a ransom payment. This will also ensure that your organization gets to working conditions as soon as possible.
Conclusion
Ransomware-as-a-service (RaaS) is a growing threat to businesses of all sizes. RaaS makes it easy for even the most unskilled criminals to launch ransomware attacks, which can result in significant financial losses and downtime.
The best way to prevent ransomware attacks is by never letting it happen. Using advanced security tools and proper training, the employees will save millions.
Timely Vulnerability assessments, along with penetration testing, will help organizations follow up on any disadvantages posed to them.
If you are struck with ransomware attacks, your movements should be swift, and the incident should be reported immediately.