What is Certificate Manager?
Certificate Manager is a service that helps to manage and deploy secured public and private digital certificates such as Secure Socket Layer/Transport Layer Security (SSL/TLS) for cloud based services and connected resources. Certificate Manager provides a security repository of private keys, certificates and prevents outages during certificate expiry by providing push notifications. Certificate Authority acts as a trusted third party for requestor and receiver of certificates.
Why to encrypt data in Cloud?
As per Thales Data Threat Report 2020, out of all the organizations surveyed, half of the overall organizational data (50%) is now stored on Cloud environment. 47% of all participating organizations confirmed that they experienced data breach or failed a compliance audit during a past one year.

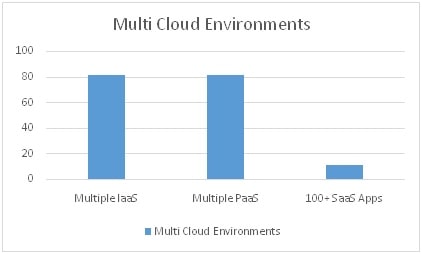
Companies are using multi-cloud environments in each category of Software as a Service (SaaS), Infrastructure as a Service (IaaS), and Platform as a Service (PaaS). Below are the statistics from the survey:
- More than one IaaS vendor – 81% of the participants
- More than one PaaS vendor – 81% of the participants
- Managing more than 100 SaaS apps – 11% of the participants
As per the above respondents who are using multiple cloud environments, 100% of them have some data in cloud which is unencrypted. This raises a serious concern regarding data security and also creates a definite threat for data privacy compliance violation as per latest General Data Protection Regulation (GDPR), California Consumer Privacy Act (CCPA), and PCI DSS etc. To avoid the outages and vulnerable situations many organizations are now opting for encryption in cloud.
What are the benefits of using Certificate Manager in Cloud?
Using Certificate Manager in cloud environment helps in tackling multiple problems related to data security. Providing data security helps organizations to be in compliance with laws and regulations such as GDPR, CCPA etc. Other benefits of using Certificate Manager in cloud include:
- Secure certificate and key management: Private keys used in certificates are protected and managed using Certificate Manager. Keys are encrypted and best practices are ensured for key management
- Protect and secure cloud apps with SSL/TLS: Data in transit of cloud apps can be protected by configuring SSL/TLS. This process ensures data is communicated/transferred between trusted entities only.
- Avoid certificate outages: Certificate expiry causes business outages. Certificate Manager issues notification on expiry due date for public facing or internal certificates
- Compliance with laws and regulations: Violating compliance regulations can cause severe damage to brand reputation and creates financial loss. Using dedicated certificate manager and enabling encryption can help in avoiding such circumstances.
If your organization is looking for implementation of encryption technologies in cloud environment, please consult info@encryptionconsulting.com for further information.




