With cloud adoption soaring to whopping 96% in 2018 according to CIO, it’s no wonder that cloud security is a hot industry topic. In today’s dynamic world, many companies are accelerating their digital transformation by moving data and applications to the cloud; benefiting from scalability and reduced costs at the same time. With cloud becoming an integral part of any enterprise, the questions that many ask include:
- How to ensure cloud data security?
- Where and how to manage encryption keys in the cloud?
- How to ensure your data is securely stored and protected in a multi-cloud environment?
- How to ensure vendor independence in a multi-cloud environment?
HSM
Hardware Security Modules (HSMs) have been around for a long time and have over the years become synonymous with “security”. Many organizations that host their data and applications on-premise will use HSMs – physical security units that authenticate, generate and store cryptographic material to protect their most valuable assets. The HSM acts as the centralized Root of Trust providing the ultimate level of security that no software can offer. While this is a great option for on-premise scenarios, it becomes complicated if you’re in a multi-cloud environment.
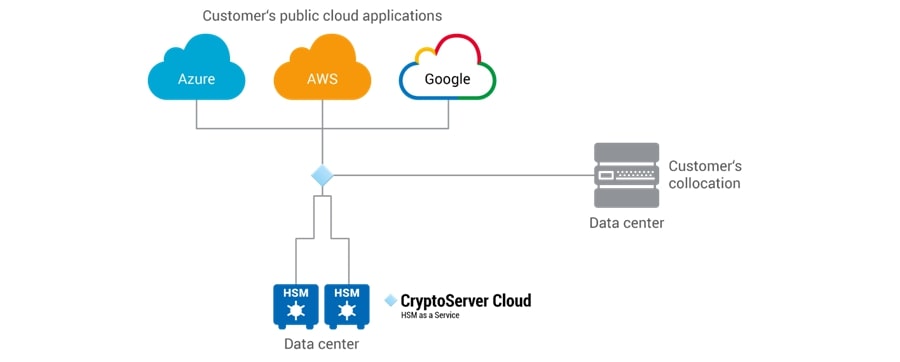
Say you do decide to go with the Key Management Service (KMS) offered by your Cloud Service Provider (CSP), what happens if your environment is a combination of private, public, hybrid or multi-cloud? The important question to ask would be if your CSP’s KMS supports data and applications hosted outside of their own data environment. Every enterprise has a unique cloud environment and getting locked-in with one vendor in the name of data security is probably not the best option. What you want to be looking for is a solution that is CSP-agnostic meaning supportive of various cloud environments so you can make the most of the benefits and services offered by key providers like Google, Azure, and AWS.
Another consideration regarding your CSP’s KMS is the proximity of your valuable data assets and your encryption keys. Is it safer to keep your house key under the doormat or in a locked vault in a secure storage facility? At the end of the day, KMS is nothing more than software which undoubtedly lacks the stringent security protections of a dedicated unit like an HSM. As a best practice, it’s important to separate your encryption keys from your encrypted data assets to minimize the risk of a catastrophic data breach.
HSM-as-a-Service: Simplified Security
We are back at where we started. If HSM is the ultimate security solution, then wouldn’t it be ideal to be able to have access to HSM-level security for your cloud applications and workloads without taking on the expense and responsibility of managing your multi-cloud environment HSM? Today, solutions like HSM-as-a-Service or HSM-in-the-Cloud offer the best of both worlds combining the security of an HSM with a flexibility of a KMS. This might be the solution for you if you’re looking for:
- Multi-cloud deployments
- Migration flexibility – no CSP and cloud lock-in
- Reducing your capex
- Innovate in the cloud – place your own firmware and custom code on the HSM
With the right strategy and solution, you can ensure your cloud security is treated like your on-premise security. Get in touch with Utimaco to learn more about CryptoServer Cloud and how you can secure your cloud data without limiting your agility and potential.