Users and organizations are valuing security and privacy more and more every day. Technologies such as HTTPS, a combination of HTTP and SSL/TLS protocols, are created to provide confidentiality and integrity of web browsing. Many organizations have taken measures to prompt the deployment of HTTPS. Since 2014, Google has improved the rankings of websites that deploy HTTPS. Furthermore, in Chrome, the websites that do not deploy HTTPS cannot use geographic locations and the application cache. Also, users may not even be able to visit websites that do not have HTTPS enabled. Eventually, they will result in an unsafe symbol in the address bar of the Chrome browser. In the past, obtaining and maintaining digital certificates would have cost a lot. Therefore, small companies or big companies with many domain names might not deploy HTTPS due to the expense. Recently, Let’s Encrypt, with its ACME protocol, has made it easier and cheaper to obtain SSL/TLS certificates, and they provide Domain Validation (DV) certificates for free through a fully automated process. Apart from Let’s Encrypt, several content distribution networks and cloud service providers, including Cloudflare and Amazon, provide free TLS certificates to their customers.
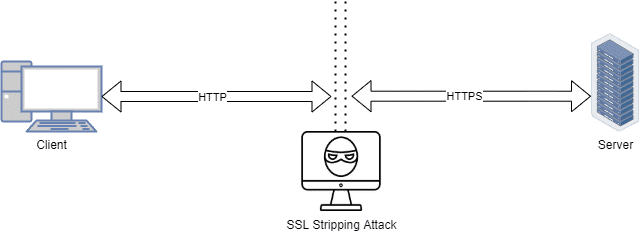
However, there are still many HTTP connections that exist on the Internet. To handle the mix of HTTP and HTTPS connections seamlessly is difficult for browsers due to the stripping attack. HTTPS stripping attacks have raised widespread concerns since Marlinspike put forward sslstrip at the blackhat conference in 2009. Attackers can intercept the communication between the target website and the client and change all HTTPS to HTTP in the response packets from the website. Even though this attack violates the rule that states TLS/SSL should ensure end-to-end security, neither the client nor the server can be aware of the attack because the packets sent from the server are still encrypted.
To defend against the stripping attack, the HTTP Strict Transport Security (HSTS) protocol was presented in 2012. It defines a mechanism enabling websites to declare themselves accessible only via secure connections.
Stripping Attack
A few years ago, HTTPS was deployed only in financial or e-commerce payment pages or login pages. However, more and more sites began to deploy HTTPS. One of the reasons is that many studies show that the site owners should provide HTTPS service on all site pages, including whole resource files, and thus encryption of part of the sites is proven unsafe. Another reason is the emergence of free certificates and the TLS accelerator. Maintaining an HTTPS service was very expensive, which included the cost of applying certificates, the cost of updating certificates, and the performance overhead caused by extra encryption or decryption. Fortunately, these problems have been solved in recent years. Many organizations began to provide free TLS/SSL certificates, and websites greatly benefited from HTTPS.
Nonetheless, an HTTPS stripping attack poses a risk to HTTPS. When users type a domain name without a protocol type (HTTP or HTTPS), the default request type is HTTP rather than HTTPS. Usually, if the server provides HTTPS service, the server will give a 302 redirection after receiving an HTTP request. However, the attacker can intercept the traffic through ARP spoofing and replace all HTTPS with HTTP in the response packet. Thus, the browser will still request an HTTP website regardless of the 302 redirections. Again, the attacker can replace all HTTP with HTTPS in the request packet. The communication between the attacker and the server is encrypted, but the communication between the attacker and the browser is in plaintext. This attack is called an HTTPS stripping attack, which browsers or servers cannot detect, as it follows the HTTP communication protocol.
HSTS Protocol
To avoid the HTTPS stripping attack, the HSTS policy was created in 2012. Websites declare the policy via the Strict-Transport-Security HTTP response header field or other means, such as user-agent configuration. If the server wants to provide HTTPS service all the time, it will send an HSTS header to the browser. According to the information in headers, the browser will remember the domains which want to forced to be visited by HTTPS. And when users send an HTTP request next time, the browser automatically converts HTTP to HTTPS in the background. The HSTS policy defines the standard of HSTS headers, and the headers mainly consist of three fields. The first is the max-age field, which implies the expiration time, and it is mandatory. The second is the optional includeSubdomains field, which indicates whether the HSTS policy applies to the domain’s subdomains. The last one is the preload field, and it is also optional. This field indicates whether the domain has been permanently added to the preload list maintained by browser providers. It is essential that HTTPS requests can only send these headers; hence, the attacker cannot arbitrarily tamper with the HSTS policy to disable it.
Conclusion
HSTS protocol provides a way to avoid SSL stripping attacks, but many site owners or developers do not understand the HSTS policy well. An SSL stripping attack provides attackers a way to read a user visiting a website in plaintext. The data between the browser and the attacker is not encrypted, giving plaintext access to the whole data, including passwords, credit card information, and more. Using the HSTS protocol avoids these issues and forces a browser to use encryption between the server and the browser.




