CodeSign Secure
Secure Your Code with Confidence.
Protect your software with a powerful, policy-driven code-signing solution to streamline security effortlessly.
Trusted By
Benefits Of Our Product
Protect Signing Keys
Keep your private keys safe in FIPS certified HSMs, ensuring the highest level of security and control.
Enforce Strong Policies
Set strict security rules, monitor key usage, and prevent unauthorized access with centralized policy enforcement.
Seamless DevOps Integration
Automate code-signing within CI/CD pipelines to enhance efficiency without disrupting developer workflows.
Secure Workflows
Sign code effortlessly with built-in security measures, ensuring compliance and protection.
Trusted Time-Stamping
Ensure long-term signature validity, keeping your software trusted even after certificate expiration.
Discover The Functionality Of CodeSign Secure
Eliminate security risks, manual inefficiencies, and unauthorized code signing with policy-driven automation, seamless CI/CD integration, and advanced authentication.
Learn More
Enforce
Policy-Driven Code Signing
Secure your software pipeline with strict policy enforcement and controlled key access.- Restrict who can sign, when, and with which keys, for full control.
- Implement RBAC and M of N quorum approvals, to prevent unauthorized access.
Integrate
Seamless CI/CD Automation
Embed secure code signing into DevOps workflows without disrupting agility.- Automate signing within Jenkins, GitHub Actions, GitLab, Azure DevOps, and CircleCI.
- Enforce release security checks and integrity validation to Prevent unsigned from reaching production.

Monitor
Complete Auditability and Compliance
Gain real-time visibility into all code-signing activities for security and compliance.- Maintain detailed event logs and audit trails to track key usage, investigate incidents, and meet compliance.
- Enable centralized tracking and instant alerts for unauthorized signing attempts.
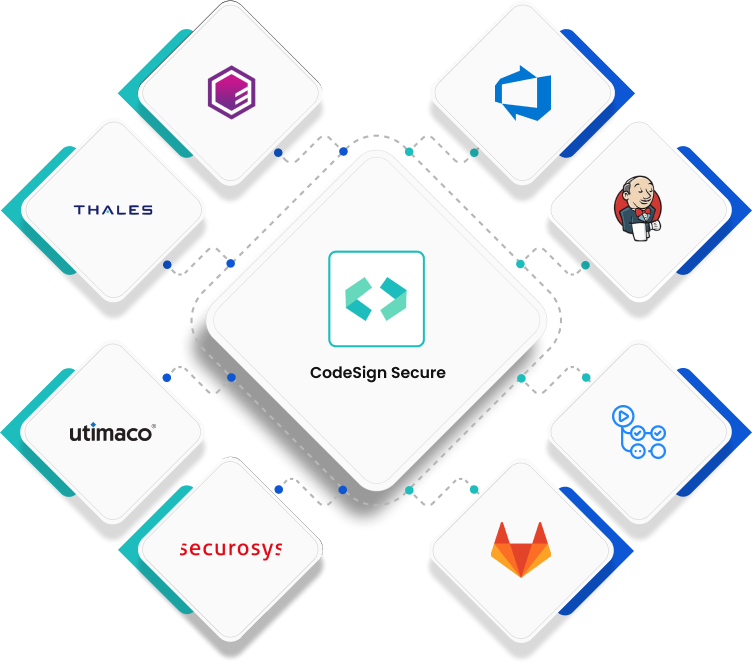
Seamless Advanced Integration
Explore the most connected code-signing ecosystem with CodeSign Secure, seamlessly integrating with your existing tools and platforms to simplify and secure the entire signing process. From DevOps pipelines to HSMs, cloud platforms to native signing tools, our solution ensures airtight security, compliance, and automation at every stage.
Use Cases
Enable seamless code-signing automation, security, and compliance across diverse platforms to protect software integrity, prevent unauthorized modifications, and streamline deployments.
Windows Signing
Sign Windows executables and drivers to ensure only trusted code runs, reducing malware risks. Seamlessly integrate with Microsoft’s infrastructure while ensuring compliance and user trust.
Docker Image Signing
Protect containerized applications with immutable digital signatures, preventing unauthorized modifications. Meet compliance while enabling secure deployments in production environments.
Firmware Code-Signing
Secure firmware signing keys with HSMs to prevent unauthorized access. Ensure only trusted firmware loads at startup, reducing supply chain risks and improving system security.
Apple Signing
Sign macOS, iOS, and watchOS apps to enable secure distribution. Prevent malware, enhance user trust, and ensure compliance with Apple’s security requirements.
Linux/RPM Signing
Sign Linux RPM packages to prevent unauthorized modifications. Ensure seamless verification by package managers, improving software trust, security, and compliance requirements.
OVA/OVF Code-Signing
Digitally sign OVA/OVF files to prevent tampering and ensure secure deployments. Simplify compliance while maintaining integrity across various virtualization platforms.Deployment Options
Choose the deployment model that best fits your security, compliance, and operational needs, ensuring seamless, high-trust code signing at scale.
On – Premises
Deploy CodeSign Secure on your infrastructure, using physical or virtualized servers, with private keys securely stored in an existing or newly configured HSM.
Cloud
Run CodeSign Secure on containers hosted in AWS, Azure, or private cloud environments, with seamless cloud HSM integration for secure key management.
SaaS
Leverage a fully managed, cloud-hosted solution with built-in HSM security, offering all on-premises features via API access without the complexity of infrastructure management.
Hybrid
Deploy CodeSign Secure on-premises using containers or physical servers while securely managing private keys in cloud HSMs, on-prem HSMs, or both for maximum flexibility.
Discover Our
Latest Resources
- Blogs
- White Papers
- Videos
Key Management
Everything About Secure Copy Protocol
Learn how Secure Copy Protocol (SCP) enables secure file transfers over SSH, its limitations, and when to use modern alternatives like SFTP and rsync.
Read more
White Paper
Introduction to Code Signing
Learn the fundamentals of code signing, from digital signatures and certificate validation to time-stamping and application reputation. Discover how to secure your software supply chain, protect against tampering, and build long-term trust across enterprise and consumer environments.
Read more
Video
PQC Migration Planning (Part 3) | How Organizations Deploy and Manage Post-Quantum Cryptography
Explore expert insights on cybersecurity, PKI, and post-quantum readiness, with practical guidance to strengthen security and future-proof cryptography.
Watch Now
Frequently Asked Questions
Everything you need to know about CodeSign Secure. Can't find the answer you're looking for? Send us an email and we'll get back to you as soon as possible!
What happens if one of our signing keys gets compromised?
A compromised signing key can invalidate the trust of every artifact ever signed with it. CodeSign Secure mitigates this risk by storing all private keys in FIPS-certified HSMs, enforcing strict access controls, and providing real-time alerts for unauthorized signing attempts, allowing your team to detect and respond before damage spreads.
How does CodeSign Secure fit into our existing development process?
CodeSign Secure is designed to integrate into your workflow without slowing it down. It embeds directly into CI/CD pipelines including Jenkins, GitHub Actions, GitLab, Azure DevOps, and Team City, meaning developers continue working as usual while signing happens automatically and securely in the background.
What happens to signatures after a certificate expires?
Normally, an expired certificate can invalidate previously signed code, creating trust issues for software already in the field. This is why CodeSign Secure recommends incorporating trusted time-stamping as a standard part of every signing operation. By anchoring the validity of a signature to the time it was made, time-stamping ensures your software remains trusted long after the signing certificate itself has expired, regardless of how the signing command is executed.
Can CodeSign Secure support multiple teams signing different products simultaneously?
Yes. CodeSign Secure supports Role-Based Access Control (RBAC) and M of N quorum approvals, allowing organizations to define precisely who can sign, what they can sign, and with which certificates. This makes it practical for large teams managing multiple products across different security requirements, without creating governance gaps.
How does CodeSign Secure help during a security incident or audit?
Every signing activity is logged with detailed event records and full audit trails. In the event of an incident, your team can quickly trace exactly what was signed, by whom, and when. For audits, these logs provide the documentation needed to demonstrate compliance with internal policies and external regulatory requirements, without scrambling to piece together records.
Is CodeSign Secure only for traditional software, or does it support modern infrastructure?
CodeSign Secure supports a broad range of signing needs beyond traditional executables, including Docker container images, firmware, Linux RPM packages, Apple platform apps, and OVA/OVF virtualization files. This makes it suitable for organizations running modern, containerized, or cloud-native infrastructure alongside traditional software environments.
What if we already have an HSM in place?
CodeSign Secure is designed to work with your existing security investments. Whether you have an on-premises HSM already configured or are leveraging cloud HSMs on AWS or Azure, CodeSign Secure integrates seamlessly, so you don’t need to replace infrastructure you’ve already invested in.
How does CodeSign Secure prevent unauthorized code from reaching production?
Beyond key protection, CodeSign Secure enforces release of security checks and integrity validation at the pipeline level, ensuring that unsigned or policy-violating code is blocked before it ever reaches a production environment. Combined with centralized policy enforcement and instant alerts, it creates a verifiable chain of trust from development to deployment.