We often come across an abstract concept called “Security on the internet” and then the Unavoidable query comes “why do we need security on the internet?”
We spend loads of time on the internet be it social media, personal communication and business transactions. The Internet security is important to communicate securely over the Internet. Thus, with the use of internet security the computers, files/data from the computer, IT systems etc. are protected from any kind of intrusion by any malicious user/system over the Internet
What does security provide?
- Confidentiality: The information within the message or transaction is kept confidential. It may only be read and understood by the intended sender and receiver.
- Integrity: The information within the message or transaction is not tampered accidentally or deliberately.
- Authentication/Identification: The persons/entities with whom we are communicating are really who they say they are.
- Non-Repudiation: The sender cannot deny sending the message or transaction, and the receiver cannot deny receiving it.
- Access Control: Access to the protected information is only realized by the intended person or entity.
All the above security properties can be achieved and implemented with the help of Digital Certificate through the use of Public Key Infrastructure (PKI) mechanism.
About Digital Certificate
The digital certificate is basically a digital form of identification by which consumers, businesses and organizations can exchange the data securely over the internet using the public key infrastructure (PKI). Digital Certificate is also known as a public key certificate or identity certificate.
Public Key Cryptography or Asymmetric Cryptography uses two different cryptographic key pairs: A.) Private key and B.) Public key. One key from the key pair is used to Encrypt and the other key is used to decrypt the data and vice-versa.
To understand what certificates are, it is important to note that a digital certificate establishes the owner’s identity, and it makes the owner’s public key available. Digital certificates are issued by trusted Certificate Authorities (CAs), which are recognized as reliable digital certificate providers. These certificates are issued only for a limited time; after the expiration of the certificate a new certificate is issued.
A digital certificate alone can only verify the identity of the digital certificate’s owner by providing the public key that is required to verify the owner’s digital signature. Therefore, the owner of the digital certificate must protect the private key that belongs to the public key of the digital certificate.
How digital certificates are verified?
- The issuer of a digital certificate is called a Certificate/Certification Authority. Verifying the certificates is the process of validating the entity’s identity. Validation process is a way to be sure about the person’s identity.
- The certificate contains information about the CA name and digital signature, these two fields will be used to authenticate the certificate. The CA name of the certificate has to be from a trusted CA and the digital signature must be valid.
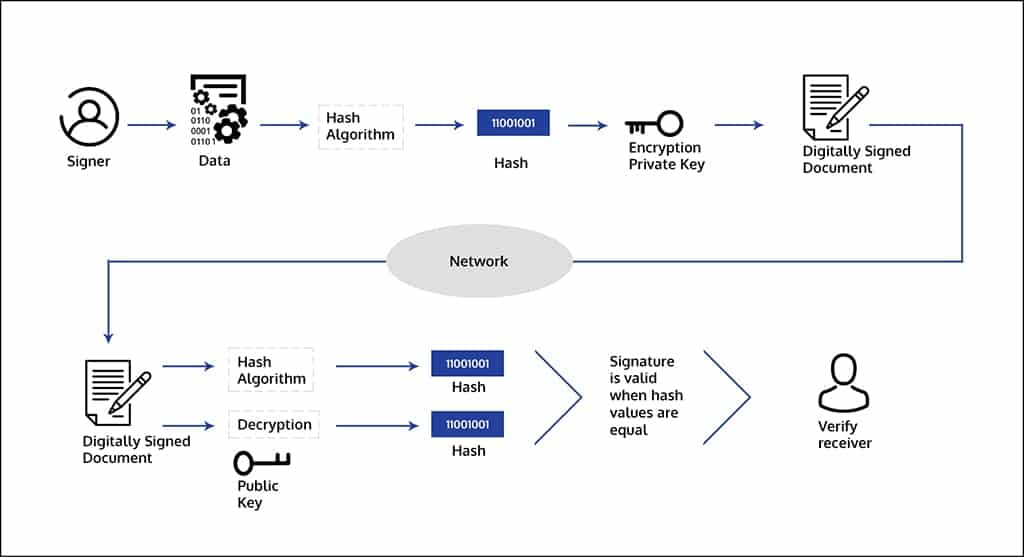
- Now, the process is to validate the digital signature of the certificate, the verification of a digital signature is performed as per the below steps:
- Calculate the hash-value: The first step is to calculate the hash-value of the message (often called a message digest) by applying a cryptographic
hashing algorithm (For example: MD5, SHA1, SHA2). The hash value of the message is a unique value. - Calculate the digital signature: In this step the hash value of the message or the message digest is encrypted with the private key of the signer, the encrypted hash value is also called as digital signature.
- Calculate the current message digest: In this step the hashed value of the signed message is calculated by the same algorithm which was used during the signing process.
- Calculate the original Hash-value: Now, the digital signature is decrypted by the public key that corresponds to the private key of the signer. As a result, we will obtain the original hash value that was calculated from the original message during the first step of the signing process.
- Compare the current and original hash value: In this step we will compare the hash values of the current message digest and the original hash value. If two values are identical then the verification is successful. This proves that the message has been signed with the private key that corresponds to the public key used in the verification process. If the two values differ, this means that the digital signature is invalid and the verification is unsuccessful.
- Calculate the hash-value: The first step is to calculate the hash-value of the message (often called a message digest) by applying a cryptographic
To manage user certificates, individuals and organizations can use certificate lifecycle management tools, which facilitates the issuance, renewal and revocation of digital certificates. The tool can be essential for maintaining the integrity and security of digital communications.
Now, worried about false impersonation of your identity? – If you send your digital certificate containing your public key to someone else, the person cannot misuse the digital certificate without having access to your private key. If the private key is compromised, then malicious users may act as the legitimate owner of the digital certificate.
Use of digital certificate in the internet applications
There are numerous internet applications using public key cryptography standards for key exchange, digital signature and digital certificates need to be used to obtain the desired public key.
Following are brief descriptions of a few of the commonly used Internet applications that use public-key cryptography:
- SSL (Secure Socket Layer) – This is an encryption-based internet security protocol. This protocol is used to provide security between the client and a server. SSL uses digital certificates, called SSL Digital, for key exchange, encryption, server authentication, and client authentication for secure communication over the internet. Overall, it provides a private communication path for a user and a trusted authority.
- Client Authentication –Client authentication is an option which requires a server to authenticate a client’s digital certificate before allowing the client to access certain resources. The server requests and authenticates the client’s digital certificate during the SSL handshake and the server can also determine whether it trusts the CA that issued the digital certificate to the client.
- Secure Electronic Mail – To secure email messages, it uses standards such as Privacy Enhanced Mail (PEM) or Secure/Multipurpose Internet Mail Extensions (S/MIME). digital certificates are used for digital signatures and for the exchange of keys to encrypt and decrypt messages.
- Virtual Private networks (VPNs) – Virtual private networks, also called secure tunnels, can be set up between firewalls/secure gateways to enable protected connections between secure networks over insecure communication links. All traffic destined to these networks is encrypted between the firewalls/secure gateways.
Windows Certificate stores
Certificate stores are a combination of logical grouping and physical storage locations. Certificate store contains certificates issued from a number of different certification authorities (CAs). Windows Certification List is a collection of certificates which are part of Windows Certificate Store, these include Root Certificates, Intermediate Certificates, End Entity Certificates, SSL/TLS certificates, Client Authentication certificates etc.
System certificate stores has the following types:
- Local machine certificate store: This certificate store is local to computer and global to all users on the computer. The certificate store is located in the registry under HKEY_LOCAL_MACHINE root.
- Current user certificate store: This certificate store is local to a user account on the computer. This certificate store is located in the registry under the HKEY_CURRENT_USER root.
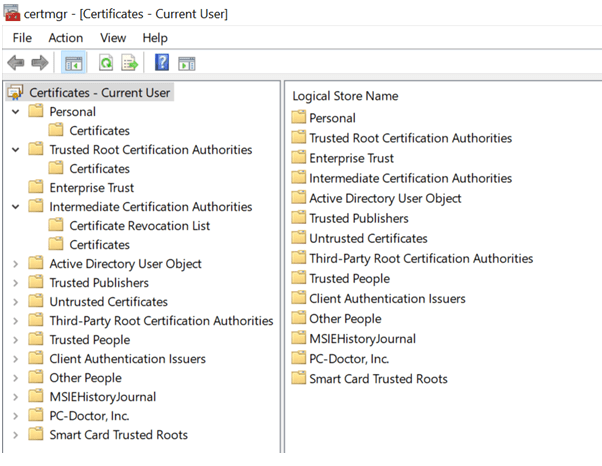
Let’s start with the certificate MMC console, easily launched by certmgr.msc.
This gives us the hint of physical certificate stores, as shown in fig 1.
As shown in figure1 below, there are several stores: smart card store, Enterprise store, the Third-Party store etc.
If we go to MMC and add the certificate snap-in, we have some more choices for the accounts: user account, service account and the computer account, all the stores listed in the fig1 have their corresponding location for each account.
Microsoft certificate stores storage locations include:
- HKEY_LOCAL_MACHINESOFTWAREMicrosoftSystemCertificates – contain the info for the computer account
- HKEY_LOCAL_MACHINESOFTWAREMicrosoftEnterpriseCertificates – contains info about the AD published certificates
- HKEY_Local_MachineSoftwarePoliciesMicrosoftSystemCertificates- contains info for the computer account, but for Group policy distributed certificates for the computer account
- User: HKEY_CURRENT_USERSoftwareMicrosoftSystemCertificates – contains registry settings for the current user. Those can include the BLOB (Binary Large object) and various settings for the certificate, as well as settings related to the CA certificates that support the user certificates.
- HKEY_Current_UserSoftwarePoliciesMicrosoftSystemCertificates – contains registry settings for the current user, but for certificates distributed via Group Policy.
- HKEY_UsersUser SIDSoftwareMicrosoftSystemCertificates – contains this info for the corresponding user
If your organization is looking for implementation of encryption technologies in cloud environment, please consult info@encryptionconsulting.com for further information.




