- Why Automate Intune Connector Monitoring?
- How Intune Connector for NDES Log Monitoring Assists Security Professionals and Organizations?
- Step-by-Step Guide to Setting Up Intune Connector Log Monitoring
- Advanced Monitoring and Analysis
- Best Practices and Considerations for NDES Log Monitoring with Intune Connector
- How can Encryption Consulting help?
- Conclusion
Are you an administrator struggling to keep up with the manual monitoring of every log and event within your Intune infrastructure? You’re not alone. As organizations rely increasingly on mobile device management (MDM) solutions, the burden of ensuring a healthy and secure environment can feel overwhelming. This blog is your helping hand.
Imagine this: A streamlined system that automatically monitors your Intune Connector logs, proactively alerting you to potential issues and freeing up your valuable time. It sounds too good to be true. It’s not! In this guide, we’ll delve into the importance of automated monitoring for Intune, specifically focusing on the Intune Certificate Connector on your NDES server within a Windows Server 2019 environment.
Why Automate Intune Connector Monitoring?
Consider the scenario where critical updates are delayed, devices fail to enroll, or compliance policies are overlooked due to a minor Intune issue flying under the radar. In such situations, the repercussions can be significant, impacting both the security and efficiency of your device management infrastructure.
-
Proactively identify and address issues
By automating log monitoring, you can proactively detect issues before they escalate. Early identification allows administrators to address problems swiftly, preventing any adverse effects on users or productivity.
-
Reduce troubleshooting time
Manually sifting through logs can be time-consuming and may delay issue resolution. Automated monitoring streamlines this process, reducing the time spent on troubleshooting and ensuring a quicker response to potential problems.
-
Enhance Security and Compliance
Automated monitoring ensures that critical updates are promptly implemented, preventing security vulnerabilities. Devices failing to enroll can be quickly addressed, maintaining the integrity of your device management system, and ensuring compliance with organizational policies.
-
Optimize Resource Utilization
By gaining insights into usage patterns through log analysis, administrators can optimize the configuration of Intune. This leads to more efficient resource utilization, enhancing the overall performance of the device management infrastructure.
-
Minimize User Disruptions
Delays in critical updates or enrollment issues can disrupt user experiences. Automated monitoring helps minimize such disruptions by tackling issues in their early stages, ensuring a smoother and more reliable device management environment.
-
Ensure Data Integrity
Compliance policies going unenforced may lead to data integrity issues. Automated monitoring acts as a safeguard, ensuring that compliance policies are consistently applied, and data remains secure and intact.
-
Facilitate Continuous Improvement
By continuously analyzing log data, administrators gain valuable insights into the functioning of the Intune infrastructure. This information can be used to implement improvements, refine configurations, and adapt strategies for even better device management over time.
How Intune Connector for NDES Log Monitoring Assists Security Professionals and Organizations?
Intune Connector for NDES log monitoring goes beyond the general benefits of security log analysis and offers targeted advantages for both security professionals and organizations. Here’s how:
For Security Professionals
-
NDES-Specific Threat Detection
Monitor for suspicious activities related to NDES certificate issuance, enrollment, and revocation attempts. This includes detecting unauthorized enrollment requests, failed attempts with brute-force patterns, or unusual certificate requests outside established policies.
-
Faster Troubleshooting of NDES Issues
Quickly identify and diagnose issues like misconfigurations, connectivity problems, or errors in the certificate issuance process, minimizing downtime and ensuring smooth device enrollment.
-
Compliance with Certificate Policies
Monitor adherence to internal certificate policies and industry standards like PKCS#7 and SCEP, ensuring a secure certificate lifecycle and reducing compliance risks.
-
Insider Threat Detection
Watch for anomalies in user behavior related to NDES certificate management, potentially indicating unauthorized access or malicious intent.
For Organizations
-
Strengthened Device Security
Proactive monitoring of NDES activities minimizes the risk of compromised certificates being issued or unauthorized devices gaining access, enhancing overall device security posture.
-
Reduced Certificate-Related Breaches
Early detection of suspicious activities or misconfigurations prevents attackers from exploiting vulnerabilities in the certificate issuance process, reducing the risk of data breaches.
-
Improved Device Enrollment Efficiency
By identifying and addressing NDES issues promptly, organizations can ensure smooth and seamless device enrollment, minimizing disruptions and delays.
-
Optimized Operational Costs
Timely troubleshooting and proactive risk mitigation minimize the need for reactive incident response, reducing operational costs associated with security breaches and disruptions.
-
Data-Driven NDES Management
Insights gained from log analysis inform decisions about NDES configuration, security policies, and resource allocation, leading to more efficient and secure NDES management.
Step-by-Step Guide to Setting Up Intune Connector Log Monitoring
Consider the scenario where critical updates are delayed, devices fail to enroll, or compliance policies are overlooked—all due to a minor Intune issue flying under the radar. In such situations, the repercussions can be significant, impacting both the security and efficiency of your device management infrastructure.
Prerequisites
-
Intune Connector: Installed and configured on your NDES server.
-
Log collection script: Prepared with your desired filtering and analysis functionalities.
-
Monitoring action: Defined, such as saving logs to a specific location or triggering alerts.
-
Administrative privileges: On the NDES server for configuration.
Task 1: Create a New Task in Task Scheduler
- Open Run (or press CTRL + R), type taskschd.msc and press OK.
- Navigate to Task Scheduler Library > Events Monitor (create a new folder if not available)
- Right-click on Events Monitor and select “Create Task…”
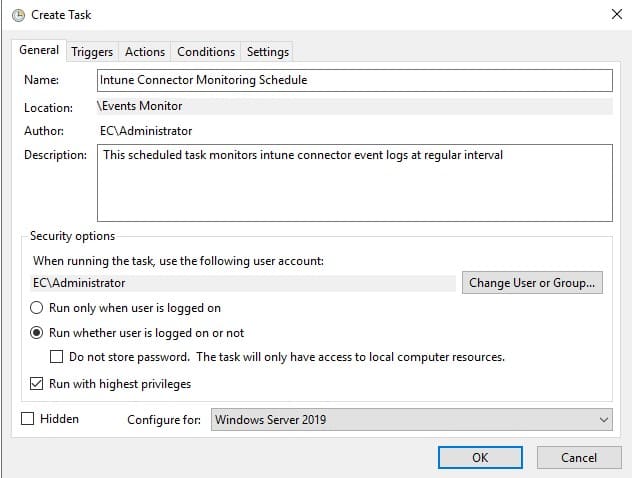
Task 2: Configure General Task Settings
- In the “General” tab, enter Name and Description for the task.
- Select the Domain Administrator account for the user account.
- Select “Run whether the user is logged on or not.”
- Opt for “Run with highest privileges.”
- Configure for “Windows Server 2019.”
- Close all necessary boxes and exit.
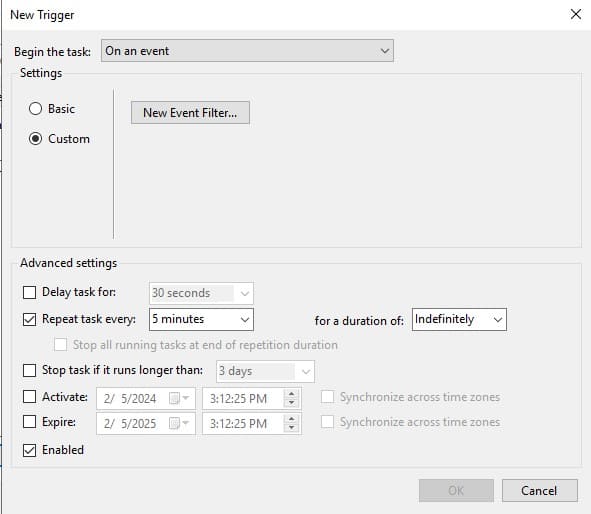
Task 3: Configure Triggers Settings
- Go to the Triggers tab and click on “New…” button.
- Select On an event from the drop-down menu to begin the task field.
- Select Repeat task every and assign a value of 5 minutes for a duration of Indefinitely.
- Deselect all other options.
- Mark as Enabled
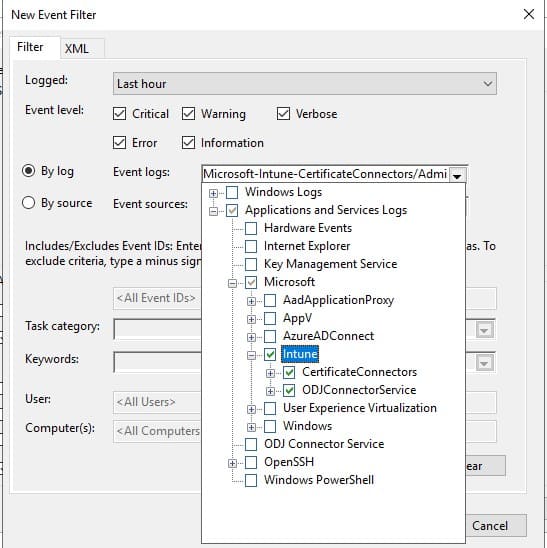
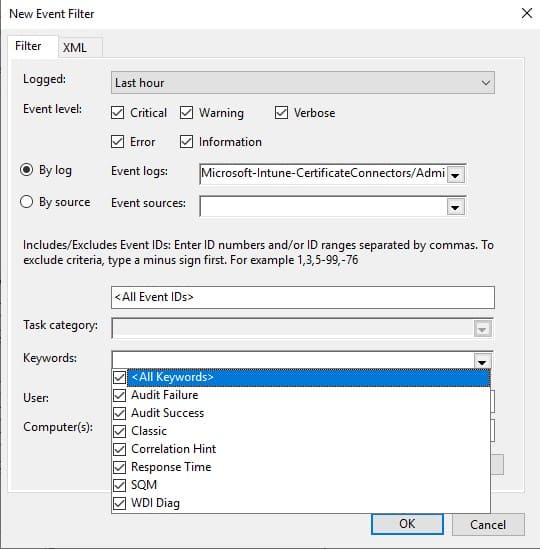
Task 4: Configure Event Filtering
- Under New Trigger settings, select the Custom event filter option.
- Click on “New Event Filter…” button.
- In the Filter Tab, select Last Hour for logged.
- Select the necessary event levels to monitor.
- Select By Logs option, expand the drop-down menu and navigate to:
Application and Services Logs > Microsoft > Intune. - Mark checked for Intune.
- In Keywords field, select the required Keywords to log.
- Press OK button.
- Press OK button on the New Trigger window.
Task 5: Define Actions for Monitoring and Diagnostics
- Go to the Actions tab and click “New…” button.
- In Action, select the type of action required to be triggered. (In this example, a custom program is executed with PowerShell)
- In Settings, fill in the required action details that are to be performed.
- For the program/script with PowerShell, fill in “powershell.exe”. (Replace with your customized program)
- For arguments, browse and select the required PowerShell script that needs to be executed. Write “-File <filename>.ps1”. (Replace <filename> with the original path of the program file if you are using PowerShell script)
Note: In this example, we are using a script that saves the logs into a ‘.json‘ file on the server’s desktop.
try {
# Specify the user’s desktop directory
$desktopPath = [System.IO.Path]::Combine([System.Environment]::GetFolderPath(‘Desktop’))
# Define the local file path to save and update the logs
$filePath = [System.IO.Path]::Combine($desktopPath, ‘intune_monitor_logs.json’)
# Check if the file already exists
if (Test-Path $filePath) {
# Read existing logs from the file
$existingLogs = Get-Content -Path $filePath | ConvertFrom-Json
} else {
# Initialize with an empty array if the file doesn’t exist
$existingLogs = @()
}
# Define the command to retrieve new logs from Event Viewer for Microsoft Intune Certificate Connector Service
$command = ‘Get-WinEvent -LogName “Microsoft-Intune-CertificateConnectors/Operational” | ConvertTo-Json’
# Run the PowerShell command and capture the output
$output = Invoke-Expression -Command $command
# Parse the JSON output for new logs
$newLogs = $output | ConvertFrom-Json
# Check for duplicates and append new logs
foreach ($logEntry in $newLogs) {
if ($logEntry -notin $existingLogs) {
$existingLogs += $logEntry
}
}
# Save the updated logs to the local file
$existingLogs | ConvertTo-Json | Set-Content -Path $filePath -Force
# Display a message indicating that logs have been updated
Write-Host “Logs successfully updated with new records.”
Write-Host “An error occurred: $_”
}
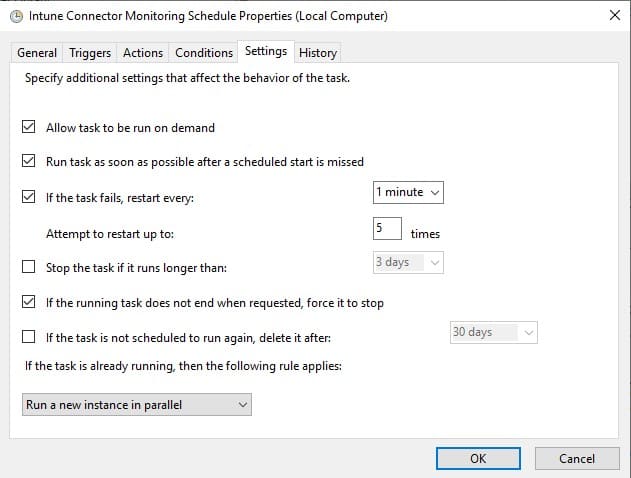
Task 6: Set Additional Task Settings
- Go to the Conditions tab and deselect all options.
- In the Settings tab, select “Allow the task to be run on demand”.
- Check “Run the task as soon as possible after a scheduled start is missed”.
- If the task fails, restart every 1 minute, attempt to restart up to 5 times.
- Select “If the running task does not end when requested, force it to stop”.
- If the task is already running, select Run a new instance in parallel.
- Press OK button.
Task 7: Credentials and Confirmation
On activating the task, a dialog asks for credentials. Fill in credentials for Domain Administrator.
Task 8: Run the New Task
- On saving the task, it will show “Ready” status.
- In the Actions pane at the right, Click on Run.
- The scheduled task will now operate and monitor Intune Connector logs.
Task 9: Verify and Monitor
- Check the History tab of the task to view execution events and ensure successful log collection.
- Access the location where your script saves the logs (e.g., server desktop) to confirm data is being written.
- Continuously monitor and analyze the collected logs to identify potential security threats, compliance issues, or operational insights.
These steps will enable you to set up an automated system to keep an eye on your Intune Connector logs for your organization. This system, powered by Task Scheduler, acts like a watchful guard, catching problems early, saving you time on troubleshooting, and giving you insights to fine-tune your Intune setup. It’s a straightforward way to make sure your device management runs smoothly.
Advanced Monitoring and Analysis
While the basic steps of setting up Intune Connector log monitoring lay the foundation, the true value lies in advanced analysis to uncover security threats, compliance issues, and valuable insights. This section explores techniques that elevate your NDES monitoring practices.
Mastering the Filter
Filtering is your superpower for navigating the vast ocean of NDES logs. Here’s how to wield it effectively:
-
Predefined Filters: Utilize built-in filters based on event severity, log source, or keyword categories to narrow down specific areas of interest.
-
Custom Filters: Craft filters targeting specific events like certificate requests from unauthorized devices, failed attempts exceeding a threshold, or revoked certificates not appearing in logs.
-
Combine Filters: Leverage the power of combining filters, for example, finding failed requests from a particular IP range during a specific timeframe.
Search Like a Pro
While filters provide focus, search expands your reach. Master these search techniques:
-
Keyword Search: Find mentions of specific devices, users, certificates, or error codes.
-
Regular Expressions: Unleash the power of regular expressions for complex pattern matching in event details.
-
Time-Based Search: Isolate events within a specific timeframe to pinpoint incidents or track changes.
Scripting for Efficiency
For repetitive tasks or complex analysis, unleash the power of custom scripts:
-
PowerShell Scripts: Use PowerShell to automate tasks like exporting specific logs, summarizing events, or triggering alerts based on custom criteria.
-
Python Scripts: Leverage Python’s advanced data analysis capabilities for in-depth log exploration and threat detection.
-
Integrate with SIEM: Connect your log data to a Security Information and Event Management (SIEM) platform for broader threat correlation and incident response.
Examples: Putting Theory into Practice:
Let’s see how these techniques can identify:
-
Potential Breach: Filter for failed certificate requests exceeding a threshold from unusual IP addresses, followed by successful requests for the same user – a possible brute-force attack.
-
Compliance Issue: Search for events indicating certificates issued outside approved hours or exceeding validity periods, highlighting policy violations.
-
Insider Threat: Combine filters and analyze user activity logs alongside NDES events to identify anomalous certificate requests or unauthorized access attempts.
Tools and Integrations for Enhanced Analysis:
Several tools and integrations can further empower your NDES log analysis:
-
Log Analysis Tools: Dedicated log analysis platforms like Splunk or Sumo Logic offer advanced filtering, visualization, and threat detection capabilities.
-
Security Automation Tools: Integrate with security automation tools like Azure Sentinel or Palo Alto Networks Cortex XSOAR for automated incident response and threat hunting.
-
Machine Learning Integration: Leverage machine learning models trained on historical data to identify anomalous behavior and potential security threats proactively.
Best Practices and Considerations for NDES Log Monitoring with Intune Connector
Having a robust monitoring system in place is just the first step. Here are some best practices and considerations to ensure your NDES log monitoring journey is smooth and successful:
-
Log Storage and Retention
-
Define a retention policy: Decide how long to store logs based on regulatory requirements, compliance needs, and security risk assessments. Avoid indefinite storage due to space and performance implications.
-
Archive older logs: Implement mechanisms to archive inactive logs to separate storage for longer-term compliance or forensic analysis needs.
-
Optimize storage: Utilize compression techniques or cloud storage solutions to optimize storage efficiency for active logs.
-
-
Access Control and Security
-
Grant least privilege access: Limit access to NDES logs based on job roles and responsibilities. Implement multi-factor authentication and strong password policies.
-
Monitor access attempts: Track and analyze user access to logs for potential anomalous activity or unauthorized access attempts.
-
Secure the script: Store your log collection script securely and restrict access to prevent unauthorized modifications or malicious usage.
-
-
Incident Response Procedures
-
Develop a clear plan: Define steps for identifying, investigating, and responding to security incidents detected through log analysis.
-
Train your team: Ensure your IT security team understands the NDES log monitoring system and their roles in incident response procedures.
-
Test and refine: Regularly test your incident response plan to identify and address any gaps or inefficiencies.
-
-
Potential Challenges and Solutions
-
Log volume overload: Monitor log volume and implement strategies like filtering, aggregation, and archiving to manage large data sets effectively.
-
False positives: Fine-tune your filters and analysis techniques to minimize false positives that trigger unnecessary alerts and consume resources.
-
Alert fatigue: Prioritize and categorize alerts based on severity and potential impact to avoid overwhelming your security team.
-
Keeping up with updates: Stay informed about updates to NDES, Intune Connector, and your log analysis tools to ensure compatibility and address potential vulnerabilities.
-
-
Continuous Improvement
-
Review and refine: Regularly review your monitoring configuration, filters, and analysis practices based on new threats, vulnerabilities, and evolving security needs.
-
Leverage automation: Explore automation tools for repetitive tasks like log analysis, reporting, and alert generation to improve efficiency.
-
Share insights: Foster communication and collaboration between IT security and device management teams to leverage log data for broader security posture improvements.
-
How can Encryption Consulting help?
Utilize Encryption Consulting’s expert guidance in automating Intune Connector Monitoring. We offer expertise relevant to automating Intune Connector monitoring in several ways:
-
Script development and customization
We can design or adapt scripts for tasks like log collection, analysis, and alert generation, ensuring security best practices.
-
SIEM integration
We can help you integrate Intune Connector logs with a SIEM platform for centralized management and advanced threat detection.
-
Incident response automation
We can assist in automating actions based on alerts, such as notifications, escalations, or remediation steps.
-
Security assessments and optimization
We can evaluate your current setup and recommend improvements for automation effectiveness and security adherence.
-
Ongoing support and training
We can provide ongoing support and training to your team on maintaining and optimizing your automated monitoring.
Conclusion
In simple terms, automated Intune Connector log monitoring is crucial for strengthening your device management system. This deliberate move empowers administrators with proactive capabilities to anticipate and promptly address potential issues, ensuring strict adherence to security protocols and optimizing overall efficiency in the organization’s device management.
By embracing automated monitoring, administrators streamline issue detection, expedite resolutions, and minimize impact on end-users, enhancing overall productivity. The ongoing scrutiny of log data acts as a guide for future enhancements, fostering a dynamic and responsive approach to device management.
This strategic investment in automation goes beyond a technological upgrade; it becomes a practical enabler, driving a seamlessly managed and future-proof device ecosystem for the organization, emphasizing a commitment to operational excellence and a proactive stance in ensuring a secure, efficient, and continually evolving device management landscape.
- Why Automate Intune Connector Monitoring?
- How Intune Connector for NDES Log Monitoring Assists Security Professionals and Organizations?
- Step-by-Step Guide to Setting Up Intune Connector Log Monitoring
- Prerequisites
- Task 1: Create a New Task in Task Scheduler
- Task 2: Configure General Task Settings
- Task 3: Configure Triggers Settings
- Task 4: Configure Event Filtering
- Task 5: Define Actions for Monitoring and Diagnostics
- Task 6: Set Additional Task Settings
- Task 7: Credentials and Confirmation
- Task 8: Run the New Task
- Task 9: Verify and Monitor
- Advanced Monitoring and Analysis
- Best Practices and Considerations for NDES Log Monitoring with Intune Connector
- How can Encryption Consulting help?
- Conclusion




