- Introduction
- Understanding Java Keystore
- Why Manual Keystore Management Falls Short
- Breakdown of Manual Java Keystore Operations
- Why Manual Management of JKS Is Unsustainable at Scale
- The Need for Automation
- Automating Java Keystore Management with CertSecure Manager
- Key Capabilities of the CertSecure CLI Agent
- A Real Workflow, Simplified
- Conclusion
Introduction
The Java KeyStore (JKS) is a foundational component in Java applications when it comes to managing digital certificates, cryptographic keys, and trust anchors. Whether you’re securing HTTPS endpoints, enabling mutual TLS, or deploying signed JARs, the keystore plays a critical role in securing application communication.
As Java applications scale across hybrid cloud environments and microservices architectures, Manual keystore management is not only slow and error-prone but also lacks proper audit trails, making it challenging to verify who accessed, modified, or deployed cryptographic keys, a critical requirement for security audits and regulatory compliance. This is where certificate automation with Certificate Lifecycle Automation tools like CertSecure Manager becomes essential. Within a CLM (Certificate Lifecycle Management) ecosystem, JKS is one of the primary certificate endpoints that needs to be managed as part of the full lifecycle, from issuance to renewal to revocation.
Most Java applications, including Spring Boot apps, Tomcat, JBoss, Kafka, Hadoop, and microservices, expect certificates and keys to be stored in a Java KeyStore (.jks) format. CLM tools need to interface with JKS to:
- Push issued certificates into the keystore
- Automate renewals to avoid expiration-related downtime
- Distribute updated keys/certs securely
- Support compliance with modern standards (e.g., 90-day or 47-day certificates)
Understanding Java Keystore
A Java Keystore is a secure, file-based repository used by Java applications to store:
- Private keys and their corresponding certificate chains
- Trusted public certificates from CAs
It is typically managed using the keytool utility that comes with the JDK.
There are two commonly used keystore formats:
- JKS : Java’s original keystore format. Though still supported, it’s now considered legacy due to limitations in cryptographic agility and security.
- PKCS12: A more modern, standardized format that supports stronger encryption and interoperability with other security systems. It is now the default format for keystores in newer Java versions.
For official documentation on JKS management, refer to Oracle’s keytool guide.
Why Manual Keystore Management Falls Short
In the past, TLS certificates typically had lifespans of 1–2 years, allowing IT and security teams to set renewal reminders and update keystores at a relatively relaxed cycle. However, industry standards are rapidly changing. Major CAs, browser vendors, and platforms like Apple and Google have pushed the move toward short-lived certificates, first to 90 days, and now 47 days is emerging as the new norm.
This shift is rooted in the principle of cryptographic agility and security hygiene. Shorter lifespans reduce the window of exposure if a private key is compromised and force organizations to automate certificate renewal and deployment.
Breakdown of Manual Java Keystore Operations
Updating a JKS manually isn’t a single-click operation. Uploading a certificate to JKS includes a series of tightly coupled, high-risk tasks that often span across teams:
-
Generating the CSR (Certificate Signing Request)
- Use keytool or openssl to create a private key and CSR.
- Save store private keys in an HSM device.
-
Submitting the CSR and Await Issuance
- Submit the CSR to your private or public CA (like DigiCert, Let’s Encrypt, etc.).
- Wait for CA to validate the CSR and issue the digital certificate.
-
Receiving and Verifying the Certificate Chain
- Download and install the issued certificate, the intermediate certificates, and the root certificate.
- Ensure the full certificate chain is correct and in proper order, starting from the leaf, followed by intermediate(s), and ending with the root, by verifying it under the Certification Path tab in the certificate properties.
-
Importing into the Keystore
- Use keytool -importcert or similar command.
- Import the signed certificate along with the chain to the keystore in the correct order along with the chain.
- Maintain correct alias mapping to the existing private key.
- Ensure compatibility with the application’s keystore format (.jks or .p12).
-
Service Restart or Certificate Reload
- If the certificate is bound to an HTTPS connector (e.g., Tomcat, Apache), the service often needs to be restarted to bind the new certificate to the designated service of the web server/load balancer.
- For clustered environments, this updated record of the certificate must be coordinated across all nodes.
-
Audit and Logging
- Maintain a detailed log capturing when the certificate was last updated, who performed the update, and which environments or systems were affected.
- Keeping a track of the certificates and maintaining a record of each in an Excel sheet is not a scalable solution.
Why Manual Management of JKS Is Unsustainable at Scale
Managing JKS keystores manually at scale presents several challenges, especially in complex enterprise scenarios. For example, consider an enterprise environment where dozens of Java applications are deployed across multiple environments, development, testing, staging, and production. Each application might have its own TLS certificate, keystore file, and alias mapping.
Some may use the older .jks format, while others have migrated to .p12 for compliance or compatibility reasons. In many cases, individual microservices or APIs are assigned their own certificates to maintain isolation and security boundaries. Managing all of this manually becomes a continuous, error-prone cycle, especially as the industry moves toward short-lived certificates that expire every 90 days, or even 47 days in certain compliance-focused infrastructures.
Every few weeks, teams must repeat a sequence of all the above complex steps. This needs to happen across multiple environments without introducing mismatches, misconfigurations, or versioning issues. Even with the most well-documented SOPs, the margin for human error is high. One missed renewal could bring down a production service.
A mismatched chain could break mutual TLS. A misplaced keystore file might trigger an audit failure. And without a proper change management or logging system, tracking who did what, when, and where becomes nearly impossible, especially in large or regulated enterprises.
The Need for Automation
To address the above mentioned challenges, organizations are increasingly adopting certificate lifecycle automation. Rather than relying on scattered manual processes and ad hoc scripts, automation allows for a centralized, policy-driven, and fully auditable system to manage certificates at scale.
An automation solution should be able to discover all keystore assets across environments and maintain visibility into their expiration timelines. It should automatically generate CSRs, submit them to the appropriate CA, and retrieve signed certificates without requiring human intervention. Once certificates are issued, the system must validate the entire chain, ensuring that the leaf, intermediate, and root certificates are correctly ordered and trusted before integrating them into .jks or .p12 keystores.
CertSecure Manager was built precisely with these goals in mind. In the next section, we’ll walk through how its CLI-driven integration with JKS enables end-to-end automation, from certificate request to secure deployment, within seconds, not hours.
Automating Java Keystore Management with CertSecure Manager
Manual keystore management doesn’t scale, especially when you’re juggling dozens of Java applications in multiple environments. To address this challenge head-on, we built a lightweight but powerful CLI integration for CertSecure Manager that brings automation, accuracy, and auditability to JKS operations. Whether you’re working with .jks or .p12, need to rotate certificates, or push CA chains into trust stores, the CLI handles it all.
Key Capabilities of the CertSecure CLI Agent
-
Request and Download Certificates
The CLI enables you to initiate certificate requests directly from your terminal, no browser, no portal logins required. You simply provide essential certificate details such as the Common Name (CN), Subject Alternative Names (SANs), key type, and algorithm, and CertSecure Manager handles the rest. Once the request is approved, the signed certificate, along with its complete chain, is securely downloaded and stored locally. You can then install the certificate in any of the five supported formats: .txt, .zip, .p7b, .pfx, or .cer based on your application’s specific requirements.
-
JKS Integration
This is the core strength of the integration. The CLI allows you to specify:
- The exact file path of the .jks or .p12 keystore
- The password protects it.
- The alias under which the new certificate and key should be stored
Once provided, the tool automatically inserts the downloaded certificate and private key into the specified keystore. It takes care of:
- Mapping the certificate to the correct alias
- Preserving existing entries
- Maintaining password protection and encrypting the secrets securely.
Thus, with this integration, there is absolutely no need to touch keytool, no need to worry about command syntax or file mismatches.
-
Push CA Certificates into the Truststore
For secure communication, especially in mutual TLS or client authentication scenarios, Java applications must trust the issuing CA. The CLI includes a built-in feature that allows you to push the necessary CA certificates directly into your keystore, ensuring that trust is properly established. Depending on your requirements, you can push a CA certificate, a domain certificate, or a PFX bundle into the keystore. This functionality is particularly valuable in environments where you manage a private CA hierarchy or need to dynamically add intermediate root certificates.
-
Manage Certificate Rotation
One of the most frustrating parts of managing TLS certificates is dealing with renewals. With the CLI agent, certificate rotation is integrated into the JKS automation workflow. Once a certificate approaches its expiration window, the tool can trigger a reissuance notification, fetch the updated certificate, and re-import it into the keystore with only a few clicks.
This keeps your Java applications running smoothly, even in a world of short-lived certificates.
-
Persistent Configuration and Seamless Reuse
You don’t have to re-enter your settings every time. The CLI integration is stateful in the sense that it securely stores your configuration (such as CertSecure Manager backend URL, default keystore paths, preferred aliases, etc.) on the local system in an encrypted database. If you ever need to update them, just re-run the executable and walk through the updated setup prompts.
A Real Workflow, Simplified
Let’s walk through how this process actually unfolds when using the CertSecure CLI integration:
-
Start with Configuration
Begin by launching the configuration executable:
./configure_certsecure.exe
Ensure that the user account running this has read and write permissions to the JKS and is authorized to perform JKS operations. During this setup, the CLI will prompt you to authenticate with your CertSecure portal. You’ll be asked to paste a token that you can retrieve from your CertSecure UI.
-
Connect to CertSecure Manager
Once the token is saved and verified, your CLI agent is officially connected to CertSecure Manager. This means all actions performed via the CLI will now honor your assigned role-based access control (RBAC) policies, audit logging, and certificate issuance workflows as defined in the central portal.
-
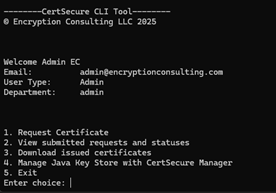
Launch the CLI Tool
With configuration complete, you can now begin managing certificates and keystores using:
./certsecure_cli.exe
-
Choose from Multiple Certificate Operations
You’ll be presented with a menu to:
- Request new certificates
- View the status of submitted requests.
- Download issued certificates.
- Manage JKS.
- Manage JKS with Ease
Selecting the “Manage Java Key Store” option gives you further choices such as:
- Check JKS configuration
- Integrate the keystore with CertSecure Manager
- Push certificates (in .pfx format) into the JKS
- Push CA certificates (from .p7b) into the JKS
- Print the current contents of the keystore for verification
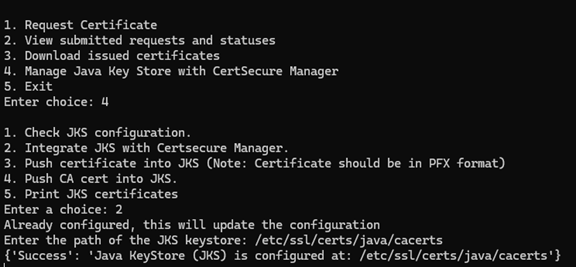
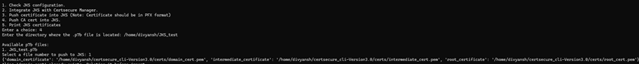
- Push CA Certificates into the JKS
For example, when you choose to push a CA certificate (option 4), you’ll be prompted to enter the directory containing your .p7b file. The CLI will list all available files in that directory. After selecting one, the CLI automatically extracts and maps:
- The domain certificate
- The intermediate certificate
- The root certificate
If any of the aliases (e.g., domain_cert, intermediate_cert, root_cert) already exist in the keystore, the CLI will prompt for deletion before re-importing—ensuring clean overwrites and avoiding duplication errors.
- Warnings & Best Practices
If you’re working with the legacy .jks format (e.g., cacerts), the CLI will display a helpful warning suggesting migration to PKCS12, the modern, standardized keystore format. This is particularly important for compatibility and long-term support.
- Result: Full Trust Chain Imported
Once confirmed, each certificate is securely imported, and a success message is displayed:
- Success: domain_certificate imported into JKS.
- Success: intermediate_certificate imported into JKS.
- Success: root_certificate imported into JKS.
Your keystore is now fully trusted and ready to support secure TLS communications.
This automated, interactive CLI experience ensures that even complex certificate deployments, such as pushing CA chains into secured Java environments, can be completed in just a few minutes, without ever touching keytool manually.
Note: For advanced users or CI/CD environments, this process can also be scripted using flags, allowing full automation of certificate renewals and keystore updates.
Conclusion
Managing certificates within Java environments has long been a time-consuming and high-stakes responsibility. From generating CSRs and importing signed certs to maintaining keystore integrity and trust chains, each step introduces operational overhead and the potential for error. With the growing industry shift toward short-lived certificates and tighter compliance requirements, manual keystore management is no longer sustainable.
That’s where CertSecure Manager’s CLI integration steps in. It doesn’t just simplify certificate operations; it standardizes and automates them. Whether you’re a platform engineer integrating certificates into your CI/CD workflow, a security administrator ensuring trust enforcement across hundreds of services, or a developer just trying to keep your local environment running securely, the CertSecure CLI provides the tooling you need.
- Introduction
- Understanding Java Keystore
- Why Manual Keystore Management Falls Short
- Breakdown of Manual Java Keystore Operations
- Why Manual Management of JKS Is Unsustainable at Scale
- The Need for Automation
- Automating Java Keystore Management with CertSecure Manager
- Key Capabilities of the CertSecure CLI Agent
- A Real Workflow, Simplified
- Conclusion