- What is SCEP?
- What is NDES?
- Why NDES Still Matters in Modern PKI?
- How NDES Works: Architecture Overview
- Common NDES Misconfigurations Found in Security Assessments
- Security Best Practices for NDES Deployments
- Where SCEP and NDES Start to Show Limitations
- The Modern Certificate Automation Framework: ACME
- Comparing SCEP, NDES, and ACME in Enterprise PKI
- Real-World Example: Hybrid Enterprise Deployment
- How to Choose the Right Enrollment Method
- The Future of Enterprise Certificate Enrollment
- How can Encryption Consulting help?
- Conclusion
As organizations accelerate adoption of Zero Trust, device authentication, and cloud-managed infrastructure, traditional manual certificate enrollment is no longer scalable. Whether onboarding thousands of laptops via Intune, issuing certificates for VPN access, or enabling Wi-Fi authentication across global offices, automated certificate enrollment is essential.
This is where SCEP (Simple Certificate Enrollment Protocol) and NDES (Network Device Enrollment Service) play a critical role in Microsoft PKI ecosystems.
Despite their importance, many administrators deploy them without fully understanding how they work, how they differ, or how to secure them properly. Misconfigured NDES servers remain one of the most common PKI weaknesses discovered during security audits.
In this article, we will break down:
- What SCEP is and why it still matters
- How NDES works in Microsoft PKI
- Real-world deployment scenarios
- Common mistakes and security risks
- Best practices for modern enterprise environments
What is SCEP?
SCEP, or Simple Certificate Enrollment Protocol, is a protocol originally developed by Cisco to automate certificate enrollment for network devices that cannot easily join Active Directory.
Unlike traditional AD-based enrollment methods, SCEP allows devices to:
- Request certificates using HTTP/HTTPS
- Authenticate using a shared secret or challenge
- Automatically retrieve signed certificates
SCEP was designed for devices such as:
- Routers and switches
- VPN gateways
- Network appliances
- IoT devices
- Mobile devices
Over time, it has evolved into the de facto standard for certificate enrollment in device management platforms, including Microsoft Intune and many MDM solutions.
What is NDES?
NDES (Network Device Enrollment Service) is Microsoft’s implementation of SCEP.
It acts as a bridge between devices and the Microsoft Certification Authority, allowing devices that cannot authenticate via Active Directory to still obtain certificates securely.
In simple terms, this is how it works:
- Devices talk to NDES using SCEP
- NDES validates the request
- NDES submits the request to Microsoft CA
- The CA issued the certificate
- NDES delivers it back to the device
Without NDES, SCEP cannot be used with Microsoft ADCS.
Why NDES Still Matters in Modern PKI?
Some administrators assume SCEP is outdated because it was created decades ago. However, the opposite is true; SCEP usage has grown dramatically due to modern device management trends.
Let’s have a look at a couple of use cases where NDES is widely used:
1. Microsoft Intune Device Certificate Enrollment
Organizations deploying Intune often rely on NDES to issue, Device authentication certificates, Wi-Fi certificates, VPN certificates, Email authentication certificates, etc.
Without NDES, Intune cannot issue certificates from on-premises ADCS.
2. Client Authentication Certificates
NDES is commonly used to issue client authentication certificates for Windows Always-On VPN, Third-party VPN clients, Hybrid remote access architectures, etc.
This enables Passwordless VPN authentication tied to device identity.
3. IoT and Network Device Enrollment
NDES allows certificates to be issued to Printers, Cameras, Manufacturing systems, and Network devices
These devices often cannot join AD, making SCEP the only scalable option.
How NDES Works: Architecture Overview
A typical NDES deployment involves four components:
- The requesting device (MDM-managed or network device)
- The NDES server
- The Microsoft Certification Authority (CA)
- The certificate template is configured for SCEP
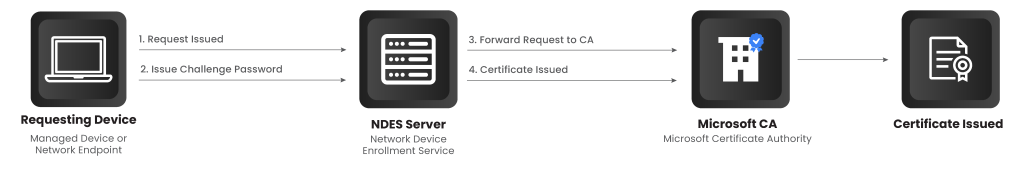
The process works as follows:
Step 1: Device Requests Enrollment: The device contacts the NDES endpoint using SCEP.
Step 2: NDES Issues a Challenge Password: NDES generates a one-time password used to validate the request.
Step 3: Device Submits Certificate Request: The device submits its certificate request along with the challenge.
Step 4: NDES Submits to the CA: NDES forwards the request to the Microsoft CA using a designated template.
Step 5: Certificate is Issued: The CA signs the certificate and returns it to NDES.
Step 6: Device Retrieves Certificate: The certificate is delivered back to the requesting device.
Common NDES Misconfigurations Found in Security Assessments
In my experience during PKI Assessment, several recurring issues appear. Let’s talk about some of them today.
- NDES Exposed Directly to the Internet: NDES endpoints often run on IIS and may be published externally without protection. This allows attackers to attempt certificate enrollment, enumerate templates, and exploit IIS vulnerabilities. NDES should always be protected by Application gateways and role-based access rules.
- Over-privileged Service Accounts: NDES uses a service account to request certificates from the CA. If this account has excessive permissions, attackers could issue certificates themselves. This risk is particularly severe because certificates can be used for authentication.
- Weak Template Configuration: Templates used for SCEP are sometimes configured to allow exportable private keys, allow overly broad usage rights, and issue certificates without approval controls. These misconfigurations can lead to identity compromise.
- Lack of monitoring and logging: Many organizations deploy NDES but never monitor it. Without proper monitoring and logging, Rogue certificate issuance goes unnoticed, Enrollment abuse cannot be detected, and incident response becomes difficult.
Security Best Practices for NDES Deployments
To secure NDES in modern environments, organizations should follow several best practices.
1. Isolate NDES Servers
NDES should never be installed directly on the CA.
Instead, deploy it:
- In a dedicated DMZ segment
- Behind a reverse proxy or application gateway
- With limited network access to the CA
2. Restrict Template Permissions
SCEP templates should:
- Allow only required EKUs
- Restrict subject name formats
- Disable private key export when possible
3. Monitor Certificate Issuance
Organizations should:
- Log SCEP requests
- Monitor template usage
- Alert on abnormal enrollment volumes
This is especially important for high-privilege templates.
4. Hardening IIS Configuration
Since NDES runs on IIS, it’s important to note the following:
- Disable unused modules
- Enforce TLS 1.2 or higher
- Apply security headers
- Regularly patch the server
For more details on security best practices for NDES deployment, refer blog: NDES Security Best Practices
Where SCEP and NDES Start to Show Limitations
Despite their widespread adoption, SCEP and NDES were not originally designed for today’s cloud-native environments.
Several challenges commonly arise in modern deployments:
Limited Security Context
SCEP was designed for simplicity, which means it provides limited identity validation capabilities. Additional controls must often be layered on top to ensure strong device authentication.
Operational Complexity
NDES deployments require:
- Dedicated servers
- IIS hardening
- Network exposure considerations
- Template configuration management
- This introduces operational overhead, especially in hybrid or multi-cloud environments.
- Scaling Challenges
While SCEP works well for endpoint devices, it is less suited for dynamic workloads such as containers, microservices, or ephemeral cloud instances. These modern workloads require faster certificate issuance cycles and stronger identity verification mechanisms.
The Modern Certificate Automation Framework: ACME
ACME, or Automated Certificate Management Environment, was developed to enable fully automated certificate lifecycle management with minimal human involvement.
Unlike SCEP, ACME was built for modern environments and supports:
- Automated certificate issuance
- Automated renewal
- API-driven workflows
- Identity verification mechanisms
ACME is widely used for public TLS certificates, but enterprises are increasingly adopting it internally for workload identities.
This makes it particularly valuable for:
- DevOps pipelines
- Kubernetes clusters
- Cloud-native services
- Service-to-service authentication
ACME’s support for short-lived certificates aligns well with Zero Trust principles.
Comparing SCEP, NDES, and ACME in Enterprise PKI
Each technology serves a different purpose. SCEP provides a simple enrollment protocol suited for endpoint devices. NDES enables Microsoft PKI environments to support SCEP-based enrollment. ACME introduces modern automation capabilities tailored to dynamic infrastructure. Organizations often use them together rather than choosing only one. For example:
- SCEP/NDES for device certificates
- ACME for server and workload certificates
- Traditional AD enrollment for domain-joined systems
This layered approach allows enterprises to modernize gradually without disrupting existing infrastructure.
Real-World Example: Hybrid Enterprise Deployment
Consider an enterprise adopting Zero Trust and migrating to the cloud simultaneously.
They might plan to deploy:
- NDES integrated with Intune to manage device certificates
- ACME-based issuance for container workloads
- ADCS auto-enrollment for internal servers
This hybrid model enables them to maintain compatibility with legacy systems while modernizing certificate lifecycle management.
It also reduces reliance on passwords and strengthens identity-based access controls across the environment.
How to Choose the Right Enrollment Method
The right approach depends on the type of identities you are managing.
If your focus is on end-user devices or network appliances, SCEP with NDES remains practical and widely supported.
If your focus is on modern workloads or automation-heavy environments, ACME offers stronger integration and scalability.
Most enterprises will need both during their transition toward cloud-native security models.
The Future of Enterprise Certificate Enrollment
Certificate-based authentication is rapidly becoming the default mechanism for securing enterprise environments. As organizations move toward:
- Passwordless authentication
- Device identity enforcement
- Zero Trust access models
- Cloud-native architecture
Certificate automation becomes a core security capability rather than a niche PKI function.
SCEP and NDES will likely remain in use for device enrollment, while ACME adoption continues to grow for workload identities and infrastructure automation.
The key challenge for security teams is not choosing one protocol over another, but designing a PKI strategy that integrates them cohesively.
How can Encryption Consulting help?
Encryption Consulting has extensive experience delivering end-to-end PKI solutions for enterprise and government clients. We provide both professional services and our automation platform (CertSecure Manager) to ensure your PKI is secure, resilient, and future-ready.
PKI Services
End-to-end advisory, design, and implementation services to help organizations build, modernize, and govern secure Public Key Infrastructure environments.
Project Planning
We assess your cryptographic environment, review PKI configurations, dependencies, and requirements, and consolidate findings into a structured, customer-approved project plan.
CP/CPS Development
In the next phase, we develop Certificate Policy (CP) and Certification Practice Statement (CPS) aligned with RFC#3647. These documents are customized to your organization’s regulatory, security, and operational requirements.
PKI Design and Implementation
We design and deploy resilient PKI infrastructures, including offline Root CAs, issuing CAs, NDES servers, HSM integration, etc., depending on the customer’s needs. Deliverables include PKI design document, build guides, ceremony scripts, and system configurations. Once deployed, we conduct thorough testing, validation, fine-tuning, and knowledge transfer sessions to empower your team.
Business Continuity and Disaster Recovery
Following the deployment, we develop and implement business continuity and disaster recovery strategies, conduct failover testing, and document operational workflows for the entire PKI and HSM infrastructure, supported by a comprehensive PKI operations guide.
Ongoing Support and Maintenance (Optional)
After implementation, we offer a subscription-based yearly support package that provides comprehensive coverage for PKI, CLM, and HSM components. This includes incident response, troubleshooting, system optimization, certificate lifecycle management, CP/CPS updates, key archival, HSM firmware upgrades, audit logging, and patch management.
This approach ensures your PKI infrastructure is not only secure and compliant but also scalable, resilient, and fully aligned with your long-term operational and regulatory goals.
CertSecure Manager
CertSecure Manager by Encryption Consulting is a certificate lifecycle management solution that simplifies and automates the entire lifecycle, allowing you to focus on security rather than renewals.
Automation for Short-Lived Certificates: With ACME and 90-day/47-day TLS certificates becoming the standard, manual renewal is no longer a practical option. CertSecure Manager automates enrolment, renewal, and deployment to ensure certificates never expire unnoticed.
Seamless DevOps & Cloud Integration: Certificates can be provisioned directly into Web Servers and cloud instances, and they integrate with modern logging tools like Datadog, Splunk, ITSM tools like ServiceNow, and DevOps tools such as Terraform and Ansible.
Multi-CA Support: Many organizations utilize multiple CAs (internal Microsoft CA, public CAs such as DigiCert and GlobalSign, etc.). CertSecure Manager integrates across these sources, providing a single pane of glass for issuance and lifecycle management.
Unified Issuance & Renewal Policies: CertSecure Manager enforces your organization’s key sizes, algorithms, and renewal rules consistently across all certificates, not just automating renewals with multiple CAs, but ensuring every certificate meets your security standards every time.
Proactive Monitoring & Renewal Testing: Continuous monitoring, combined with simulated renewal/expiry testing, ensures you identify risks before certificates impact production systems.
Centralized Visibility & Compliance: One consolidated dashboard displays all certificates, key lengths, strong and weak algorithms, and their expiry dates. Audit trails and policy enforcement simplify compliance with PCI DSS, HIPAA, and other frameworks.
If you’re still wondering where and how to get started with securing your PKI, Encryption Consulting is here to support you with its PKI Support Services. You can count on us as your trusted partner, and we will guide you through every step with clarity, confidence, and real-world expertise.
Conclusion
Enterprise PKI is evolving from a backend security tool into a central identity infrastructure.
Understanding how SCEP, NDES, and ACME interact allows organizations to build scalable certificate management pipelines that support both legacy environments and modern cloud workloads.
By combining traditional PKI foundations with modern automation frameworks, enterprises can move toward stronger identity-driven security without sacrificing operational efficiency.
- What is SCEP?
- What is NDES?
- Why NDES Still Matters in Modern PKI?
- How NDES Works: Architecture Overview
- Common NDES Misconfigurations Found in Security Assessments
- Security Best Practices for NDES Deployments
- Where SCEP and NDES Start to Show Limitations
- The Modern Certificate Automation Framework: ACME
- Comparing SCEP, NDES, and ACME in Enterprise PKI
- Real-World Example: Hybrid Enterprise Deployment
- How to Choose the Right Enrollment Method
- The Future of Enterprise Certificate Enrollment
- How can Encryption Consulting help?
- Conclusion




