Introduction
Modern internet security relies heavily on public-key cryptographic algorithms such as Rivest–Shamir–Adleman (RSA) and Elliptic-Curve Cryptography (ECC). These algorithms protect everything from websites and online banking to software updates and encrypted communication. However, the rapid progress in quantum computing has raised concerns about the long-term security of these traditional cryptographic systems. Cryptographically Relevant Quantum Computers (CRQCs) are quantum computers powerful enough to run algorithms such as Shor’s Algorithm, which can factor large integers and solve discrete logarithm problems exponentially faster than classical computers. Because many public-key cryptographic systems rely on the computational difficulty of these problems, a sufficiently powerful quantum computer could break these widely used encryption algorithms, posing a significant threat to current internet security.
To address this threat, the field of Post-Quantum Cryptography (PQC) emerged. PQC refers to cryptographic algorithms that are designed to remain secure even in the presence of these CRQCs. Unlike traditional cryptography, which relies on mathematical problems that can be broken down by quantum computers, PQC relies on mathematical problems that are believed to remain difficult for both classical and quantum computers to solve, while still being implementable on classical computing systems with certain computational and implementation requirements.
Research into quantum-resistant cryptography has been ongoing for decades, but the effort intensified when the National Institute of Standards and Technology (NIST) launched its PQC Standardization Project in 2016. After several evaluation rounds involving researchers from around the world, NIST selected a set of algorithms for standardization. One of the main algorithms chosen for key encapsulation is CRYSTALS‑Kyber, which was later standardized as Module-Lattice-based Key Encapsulation Mechanism (ML‑KEM). In addition to key encapsulation mechanisms, PQC also includes digital signature algorithms for authentication and integrity, such as ML-DSA (CRYSTALS-Dilithium), FN-DSA (FALCON), and SLH-DSA (SPHINCS+).
Why is PQC Necessary?
The adoption of PQC is becoming increasingly important for the overall security infrastructure of organizations, as many critical systems rely on public-key cryptography to protect sensitive data, communications, and digital identities. Public-key cryptographic mechanisms are widely used in applications such as secure communication protocols, software updates, authentication systems, and digital certificates that underpin trust on the internet. If these cryptographic systems become vulnerable, it could compromise the confidentiality, integrity, and authenticity of organizational data and services. As the threat of quantum computing advances, organizations must prepare to replace vulnerable cryptographic mechanisms with quantum-resistant alternatives.
The transition to PQC is particularly important for internet security protocols such as Transport Layer Security (TLS), which web browsers use to establish secure HTTPS connections with websites. Today, TLS relies on widely deployed public-key algorithms such as RSA and ECC for key exchange and authentication. While these algorithms are secure against classical computers, they are vulnerable to quantum attacks that could be performed by sufficiently powerful quantum computers in the future.
One of the major concerns associated with this threat is the harvest now, decrypt later (HNDL) scenario. In this scenario, adversaries may capture and store encrypted internet traffic today with the intention of decrypting it later once quantum computers become widely available. This creates long-term confidentiality risks for sensitive data such as financial transactions, personal communications, intellectual property, and government records.
To address this emerging risk, the industry is gradually integrating post-quantum cryptographic algorithms into existing protocols. Modern web browsers are experimenting with hybrid key exchange mechanisms that combine traditional cryptographic methods, such as elliptic-curve Diffie-Hellman, with quantum-resistant algorithms like ML-KEM. Hybrid approaches ensure backward compatibility while providing additional protection against potential quantum attacks.
Today, major web browsers such as Mozilla Firefox, Google Chrome, and Microsoft Edge provide support for post-quantum cryptographic mechanisms. Enabling PQC support in these browsers is an important step toward preparing web security for the challenges posed by quantum computing. As quantum computing continues to advance, it becomes increasingly important to adopt cryptographic algorithms that can resist quantum attacks. This helps ensure that sensitive data and online communications remain secure for the long term.
By enabling PQC support in modern browsers, users and organizations can start preparing their systems for the next generation of cryptography. In this blog, we will learn how to enable PQC support in popular web browsers and understand how it helps strengthen the security of web communication.
Enabling PQC Support in Web Browsers
This section explains how to enable or verify PQC support in Google Chrome, Microsoft Edge, and Mozilla Firefox.
Chrome and Edge
Both Chrome and Edge are built on the Chromium browser engine. Because of this shared architecture, the process for enabling or verifying PQC support is very similar in both browsers. Below are the steps to check or enable PQC support depending on the browser version.
For Newer Versions
In newer versions of Chromium-based browsers, post-quantum hybrid key exchange support is integrated directly into the browser. This means manual configuration through experimental flags may no longer be required. Modern versions of Chrome and Edge automatically attempt hybrid TLS key exchange (for example, X25519 combined with ML-KEM) when connecting to servers that support PQC.
To check the browser version, open the following pages in the address bar:
For Chrome:
chrome://version
For Edge:
edge://version
If you are using a recent version of these browsers, PQC functionality may already be included internally and enabled automatically during TLS handshakes.
For Older Versions
In older versions of Chromium-based browsers, PQC support was available as a feature that could be enabled through browser flags. Below are the steps to enable it.
- Open the Chrome or Edge browser.
-
Type the following in the address bar and press Enter:
-
For Chrome:
chrome://flags
-
For Edge:
edge://flags
-
For Chrome:
- In the search bar on the flags page, search for the keyword kyber.
- Locate the experimental option related to TLS 1.3 hybridized Kyber support or post-quantum key exchange.
- Change the setting from Default to Enabled.
- Click Relaunch to restart the browser and apply the changes.
After restarting, the browser will attempt hybrid TLS handshakes using Kyber with compatible servers.
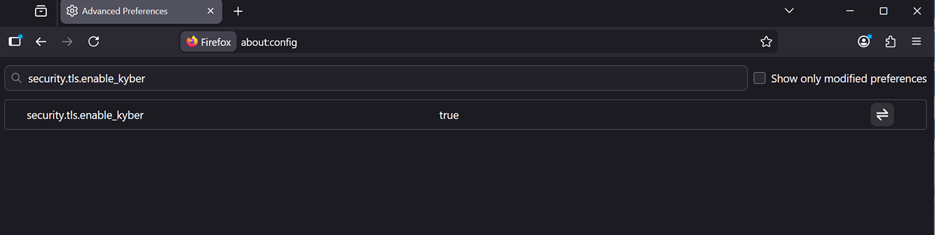
Mozilla Firefox
Unlike Chromium-based browsers, Mozilla Firefox exposes several experimental cryptographic features through advanced configuration settings. Below are the steps to enable PQC support in Firefox.
- Open the Firefox browser.
-
Type the following in the address bar:
about:config
-
In the search bar, search for the following preference:
security.tls.enable_kyber
- Change the value to true.
- Restart the Firefox browser.
- After restarting, Firefox will attempt hybrid TLS handshakes using Kyber or ML-KEM when connecting to servers that support PQC.
Verifying PQC Support in Web Browsers
After enabling PQC support in your browser, the next step is to verify whether the browser is negotiating a post-quantum key exchange during the TLS handshake.
Via Cloudflare
One of the easiest ways to test this is by using the PQC test page provided by Cloudflare. Below are the steps to verify PQC support.
- Open your browser.
- Navigate to the following website: https://pq.cloudflareresearch.com
- Once the page loads, it will display the key exchange mechanism used during the TLS handshake between your browser and the server.
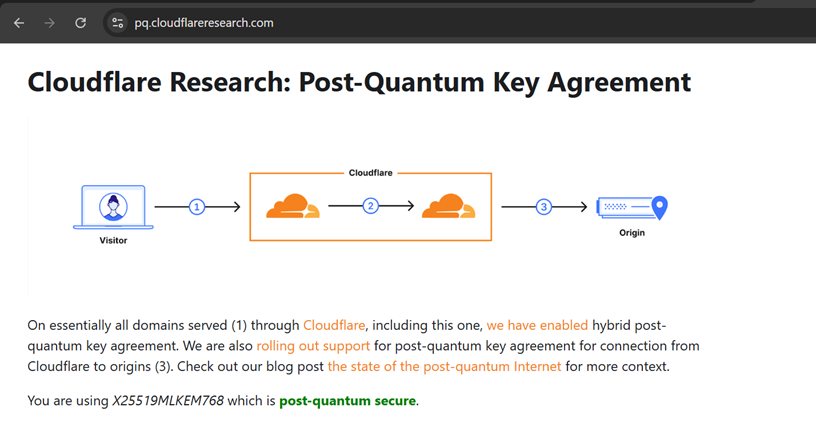
If PQC is successfully enabled and supported by your browser, the test page from Cloudflare may display a message such as “You are using X25519MLKEM768 which is post-quantum secure.” This indicates that the TLS connection between your browser and the server is using a hybrid post-quantum key exchange mechanism.
Via Browser
You can also check which cipher is used for a connection directly from the browser. Steps are mentioned below.
- Launch Google Chrome.
- Open the URL of the website you want to test.
- Click the ellipsis (three dots) in the top-right corner of the browser.
- Navigate to More Tools → Developer Tools.
- Open the Privacy and Security or Security tab in the Developer Tools panel.
- In the Connection section, review the details to see the protocol and cipher suite used for the secure connection.
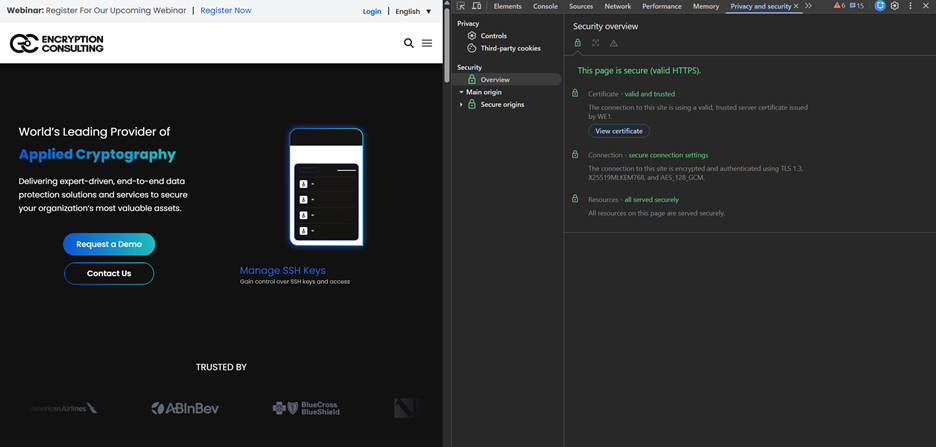
The algorithm X25519MLKEM768 combines two cryptographic techniques: X25519, which is a classical elliptic-curve Diffie-Hellman key exchange algorithm commonly used in modern TLS implementations, and ML-KEM-768, which is a post-quantum key encapsulation mechanism.
Hybrid cryptography is used because it provides security against both present-day and future threats. The classical component (X25519) ensures compatibility and protection against current attackers, while the post-quantum component (ML-KEM-768) is designed to remain secure even in the presence of large-scale quantum computers. During the TLS handshake, the shared secret is derived from both algorithms, which means that the connection remains secure as long as at least one of the algorithms remains unbroken.
If PQC is not enabled or supported by the browser, the page may instead show a classical key exchange algorithm such as X25519. In that case, the connection is still protected by traditional cryptographic methods but does not yet include post-quantum protection.
However, this also highlights the transitional state of modern cryptography. Many environments today operate in hybrid or fallback modes depending on client and server capabilities. Therefore, as organizations begin introducing quantum-resistant mechanisms, ensuring compatibility across browsers, libraries, and infrastructure becomes a critical consideration.
PQC Migration and Challenges
Migrating to PQC is an important step toward protecting digital infrastructure from the future risks posed by quantum computing. However, transitioning from traditional public-key cryptographic systems to quantum-resistant alternatives presents several technical, operational, and organizational challenges. These challenges must be carefully addressed to ensure a secure and efficient migration process. Some of them are mentioned below:
Cryptographic Discovery and Inventory
One of the first challenges in PQC migration is identifying where cryptography is used across an organization’s infrastructure. Cryptographic components are often deeply embedded in applications, APIs, network protocols, databases, and hardware devices. Without a comprehensive inventory of cryptographic assets, such as keys, certificates, algorithms, and dependencies, it becomes difficult to determine which systems are vulnerable and require migration.
Compatibility with Existing Systems
Many existing systems and protocols were designed around classical cryptographic algorithms such as RSA and Elliptic Curve Cryptography. Integrating PQC algorithms into these environments may require changes to protocols, libraries, and infrastructure components. Ensuring backward compatibility with legacy systems while introducing quantum-resistant mechanisms can be complex.
Performance and Resource Overhead
Many PQC algorithms introduce larger key sizes, ciphertexts, or signatures compared to classical algorithms. This can increase computational overhead, memory usage, and network bandwidth requirements. Systems with limited resources, such as embedded devices or IoT systems, may face additional constraints when adopting PQC.
Protocol and Infrastructure Updates
Security protocols such as TLS and digital certificate infrastructures must be updated to support PQC algorithms. This often involves upgrading cryptographic libraries, certificate authorities, and authentication systems. Coordinating these updates across distributed systems and services can be a complex operational task.
Migration Planning and Risk Management
Beyond technical integration, organizations must carefully plan how and when to transition to PQC. Migration decisions must consider factors such as system criticality, data sensitivity, and the expected lifetime of protected information. For example, data that must remain confidential for many years may require earlier migration due to potential HNDL risks. Organizations should adopt phased or hybrid approaches during the transition period to balance security improvements with operational stability and minimize disruptions to existing services.
How can Encryption Consulting Help?
Encryption Consulting is your trusted partner in achieving quantum-safe security. We guide you through every phase, from discovery to migration, with clarity, confidence, and proven expertise.
- Cryptographic Discovery & Inventory: The first step in quantum-readiness is conducting a comprehensive discovery and inventory of an organization’s cryptographic assets. Then we begin by mapping your entire cryptographic landscape. This includes identifying all systems (on-prem, cloud, hybrid) using cryptographic keys, certificates, algorithms, and dependencies across applications, APIs, networks, and databases.
- PQC Impact Assessment: Next, we evaluate vulnerabilities to quantum threats by analyzing cryptographic assets relying on RSA, ECC, and similar algorithms. We assess your PKI, HSMs, and applications for PQC readiness and deliver a prioritized report highlighting high-risk areas and migration needs.
- PQC Strategy & Roadmap: With risks defined, we create a tailored, phased migration strategy aligned with your business, compliance, and technical goals. This includes policy updates, algorithm agility design, and a clear roadmap outlining pilot, hybrid, and full deployment stages.
- Vendor Evaluation & Proof of Concept: We help you select and test PQC-ready solutions. We will help you define technical and business requirements for RFI/RFP, run PoCs to evaluate vendor offerings, and deliver vendor comparison matrix and recommendation report to ensure optimal technology selection for your environment.
- Pilot Testing & Scaling: Before full deployment, we validate PQC models in pilot environments to ensure interoperability and minimize disruption. Feedback from technical and business teams fine-tunes the rollout for scalability and efficiency.
- PQC Implementation: Finally, we execute full-scale migration, integrating PQC into your live environment while maintaining compliance, continuity, and hybrid algorithm support. Rolling out PQC support across your PKI, applications, infrastructure, cloud services, and APIs. Providing hands-on training for your teams along with detailed technical documentation for ongoing maintenance. Setting up monitoring systems and lifecycle management processes to track cryptographic health, detect anomalies, and support future upgrades.
Transitioning to PQC is complex, but you don’t have to do it alone. Encryption Consulting ensures a smooth, secure journey. Reach out to us at info@encryptionconsulting.com and let us build a customized roadmap that aligns with your organization’s specific needs.
Conclusion
The transition to post-quantum security is gradually becoming a priority for the modern internet ecosystem. PQC refers to cryptographic algorithms designed to remain secure against both classical and quantum computers. These algorithms aim to replace or augment current public-key systems that could become vulnerable once large-scale quantum computers become practical.
As researchers and organizations continue to prepare for the potential impact of quantum computing, technologies such as PQC are being integrated into everyday platforms and tools. Major browsers like Google Chrome, Microsoft Edge, and Mozilla Firefox have already started supporting hybrid cryptographic mechanisms that combine classical algorithms with quantum-resistant techniques.
Enabling PQC support in browsers and verifying it through testing platforms allows developers, security teams, and researchers to better understand how these new cryptographic mechanisms work in real-world environments. Taking these small steps today helps organizations become more prepared for the long-term transition toward a quantum-safe internet.