HEALTHCARE
Protecting Patient Trust with Cryptographic Security
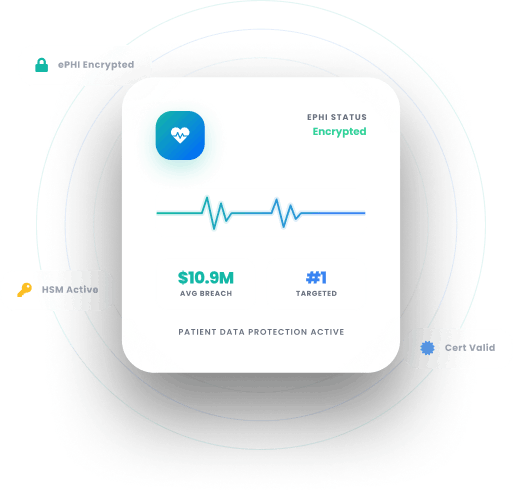
Patient data is among the most sensitive and most targeted information in the world. We help healthcare organizations protect it, secure connected medical devices, and stay compliant.
Trusted By
$7.42M
Average cost of a data breach#1
Most targeted industry globally279 days
Average time to identify and contain a breach.2030
NIST Quantum DeadlineTHE PROBLEM
What’s Holding the
Healthcare Sector Back?
Cryptographic Blind-Spots
EHR platforms, clinical portals, and third party integrations carry cryptographic assets that are rarely inventoried together, leaving compliance gaps invisible until an audit surfaces them.
Connected Device-Vulnerabilities
Infusion pumps, imaging systems, and remote monitoring devices rely on certificates and keys that are rarely rotated, creating persistent entry points for ransomware and unauthorized access.
Long Lived Patient Data
Genomic sequences, chronic condition histories, and mental health records must stay confidential for a patient's lifetime, making them prime targets for HNDL attack.
Fragmented Networks
Mergers, acquisitions, and third party integrations create fragmented PKI environments where no single team has visibility or consistent policy enforcement.
Software Integrity
Unsigned clinical application updates and device firmware can be tampered with in transit, introducing risk where HIPAA and FDA demand provable software integrity.
METHODOLOGY
Our Approach
Healthcare cryptographic programs must protect patient safety, satisfy regulators, and operate without disrupting clinical workflows. We design every engagement around those three realities:
01
Clinical Context First
Every cryptographic asset touches a system that affects patient care. We map your footprint across clinical networks and connected devices before recommending a single change.
02
Zero Disruption to Care
Clinical environments cannot tolerate downtime. We automate cryptographic workflows around care delivery schedules, not IT maintenance windows.
03
Protected for a Lifetime
Patient records outlive the systems that created them. We build post quantum readiness into every engagement so protections remain sound for decades.
PRODUCTS
How We Help?
Applied Cryptography Products
CBOM Secure
Cryptographic Discovery & Inventory
Continuous, automated inventory of every cryptographic asset across clinical applications, medical device firmware, and third party integrations. Generates audit ready reports aligned to HIPAA, FIPS SP800, and SOC 2 with up to 80% less manual effort.
CertSecure Manager
Certificate Lifecycle Management
Unified certificate visibility and automated lifecycle management across hospital networks, connected devices, and clinical portals. Prevents certificate expirations from becoming care disruptions or HIPAA breach notification events.
PKI-as-a-Service
Scalable PKI Without Complexities
Fully managed, single tenant PKI on FIPS 140-3 Level 3 HSMs issuing and managing trusted identities for clinical users, connected devices, and health IT systems without infrastructure overhead.
HSM-as-a-Service
High Assurance HSM Solution
FIPS 140-3 certified HSM solutions protecting ePHI encryption keys, medical device credentials, and PKI root trust across on premises, cloud, or hybrid environments.
CodeSign Secure
Code Signing Solution
Ensures every clinical application and device firmware release is verifiably authentic before deployment. Delivers HSM backed signing, FIPS 140-2 Level 3 compliance, and PQC ready support for MLDSA and LMS.
SERVICES
Expert-Led
Advisory & Implementation
Public Key Infrastructure Services
PKI assessments, CA architecture design, and certificate lifecycle management for IoMT devices, EHR integrations, and multi site hospital networks.
Post Quantum Cryptography Services
Cryptographic inventory, quantum exposure analysis, and a migration roadmap to NIST algorithms for organizations where patient records must stay private for a lifetime.
Encryption Advisory Services
Assess your ePHI encryption posture across clinical systems and third party integrations. Identify gaps against HIPAA, HITECH, and NIST SP 800-111, and receive a remediation roadmap.
Compliance Services
Gap assessments, remediation roadmaps, and compliance support across HIPAA, HITECH, FIPS 140-3, and SOC 2, backed by over 600 governance frameworks globally.
Why Encryption Consulting?
Device Coverage
We extend cryptographic governance across the clinical environment, including connected devices like infusion pumps and imaging systems that most programs leave unaddressed.
HIPAA Compliance Built-In
Every architecture decision and certificate workflow is designed from the outset to satisfy HIPAA Security Rule technical safeguards and withstand OCR audit scrutiny.
Vendor-Neutral
We are independent of Thales, Entrust, DigiCert, Microsoft ADCS, AWS KMS, Azure Key Vault, and more. Our recommendations reflect your clinical obligations, not a vendor margin.
TRUSTED BY THE FORTUNE 500
4 of 5
Top Global Software Companies4 of 5
Top Financial Services3 of 5
Top Global Ranks3 of 4
Top Energy & UtilitiesWho We Serve?
From large hospital networks to clinical research organizations, we help healthcare entities of every type build cryptographic programs that protect patients and satisfy regulators.
Hospital Networks
Securing certificates, keys, and clinical infrastructure across multi-site environments.
Ambulatory Providers
Protecting ePHI and connected device credentials in distributed care settings.
Health Insurers
Encrypting member data and securing claims processing infrastructure end to end.
Life Sciences
Safeguarding clinical trial data, research records, and regulated manufacturing systems.
Device Manufacturers
Signing firmware, managing device certificates, and meeting FDA integrity requirements.
Telehealth Providers
Protecting patient communications, identity credentials, and connected care infrastructure.
Research Organizations
Securing cryptographic controls across multi-site trials and research data pipelines.
Discover Our
Latest Resources
- Blogs
- White Papers
- Videos
PKI
PKI Maintenance and Quarterly Cleanup for Microsoft CA
Learn how to perform PKI maintenance and quarterly cleanup for Microsoft CA, including CA database backup, certificate cleanup, offline compaction, and post-maintenance validation.
Read more
White Paper
Introduction to Code Signing
Learn the fundamentals of code signing, from digital signatures and certificate validation to time-stamping and application reputation. Discover how to secure your software supply chain, protect against tampering, and build long-term trust across enterprise and consumer environments.
Read more
Video
The 2026 Guide to Upgrading Enterprise PKI and HSMs for Post Quantum Security
Explore expert insights on cybersecurity, PKI, and post-quantum readiness, with practical guidance to strengthen security and future-proof cryptography.
Watch Now