AUTOMOTIVE
Cryptographic Trust from Design to Road
Modern vehicles are software platforms carrying passengers at speed. We help automakers, Tier 1 suppliers, and connected vehicle platforms build cryptographic foundations that safety and regulation demand.
Trusted By
23M
Subscribers affected when SK Telecom's network was breached$97.2M
Record regulatory fine imposed on SK Telecom for cryptographic failures.NIS2
Telecom providers classified as essential entities face fines up to €10M2030
NIST quantum-resistant encryption deadlineTHE PROBLEM
What’s Holding
Automotive Sector Back?
Unsigned OTA Updates
Over-the-air update pipelines lack end-to-end signed and verified delivery, meaning a single tampered update can compromise millions of vehicles simultaneously.
PKI at Vehicle Scale
V2X communication, device authentication, and connected service trust require certificate management at a scale most automotive PKI programs were never designed to handle.
Supply Chain Provenance
Tier 1 and Tier 2 supplier software arrives without a cryptographic bill of materials, leaving manufacturers unable to prove the integrity of safety-critical ECU components.
Mandatory Type Approval
ISO 21434 and UNECE WP.29 require demonstrable cryptographic controls across the vehicle development lifecycle with substantial type approval evidence burdens.
Quantum Risk
Vehicles sold today will be on the road in 2040 and beyond, requiring crypto agility that outlasts the threat model the vehicle was originally designed against.
METHODOLOGY
Our Approach
Automotive cryptographic programs must protect vehicle safety, satisfy type approval regulators, and cover the full supply chain. We design every engagement around those realities:
01
Safety Critical First
Every key and signing credential affects a system where failure causes physical harm. We map your cryptographic footprint before recommending a single change.
02
Release Cycle Aligned
Automotive development runs on fixed model year schedules. We integrate cryptographic workflows into your pipeline without disrupting type approval timelines.
03
Built for Vehicle Lifetimes
Vehicles outlive the algorithms that secured them. We build post quantum readiness into every engagement so protections remain sound for the full lifecycle.
PRODUCTS
How We Help?
Applied Cryptography Products
CBOM Secure
Cryptographic Discovery & Inventory
Automated inventory of cryptographic assets across vehicle software stacks and supplier components. Generates audit ready reports aligned to ISO 21434, UNECE WP.29, and NIST with up to 80% less manual effort.
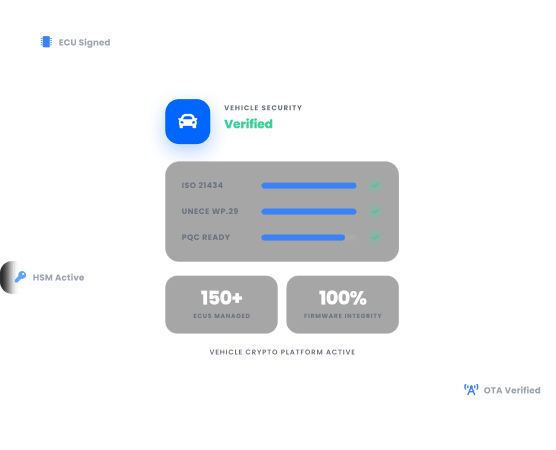
CertSecure Manager
Certificate Lifecycle Management
Unified certificate visibility and lifecycle management across V2X infrastructure and connected vehicle platforms. Prevents expirations from silently breaking vehicle-to-cloud authentication across model lines.
PKI-as-a-Service
Scalable PKI Without Complexities
Fully managed, single tenant PKI on FIPS 140-3 Level 3 HSMs issuing trusted identities for vehicles, connected services, and supply chain partners at automotive scale.
HSM-as-a-Service
High Assurance HSM Solution
FIPS 140-3 certified HSM solutions protecting OTA signing keys, V2X credentials, and PKI root trust across on premises, cloud, or hybrid environments.
CodeSign Secure
Code Signing Solution
Ensures every OTA firmware update and supplier package is cryptographically verified before deployment. Delivers HSM backed signing, FIPS 140-2 Level 3 compliance, and PQC ready support for MLDSA and LMS.
SERVICES
Expert-Led
Advisory & Implementation
Public Key Infrastructure Services
PKI assessments, CA architecture design, and certificate lifecycle management for V2X infrastructure, OTA platforms, and Tier 1 supplier integration.
Post Quantum Cryptography Services
Cryptographic inventory, quantum exposure analysis, and a migration roadmap to NIST algorithms where vehicle lifecycles demand protections that outlast today's threat model.
Encryption Advisory Services
Assess your encryption posture across vehicle software, OTA pipelines, and supplier integrations. Identify gaps against ISO 21434 and NIST, and receive a remediation roadmap.
Compliance Services
Gap assessments, remediation roadmaps, and compliance support across ISO 21434, UNECE WP.29, NIST, and regional type approval requirements.
Why Encryption Consulting?
Safety Critical Expertise
Cryptographic failures in automotive are not just security incidents, they are potential recalls and safety investigations. We design programs with the rigor vehicle certification demands.
Full Supply Chain Coverage
Most cryptographic risk comes from Tier 1 and Tier 2 suppliers. Our CBOM Secure product extends cryptographic governance beyond the OEM to the components inside the vehicle.
Trusted at Scale
Organizations across vehicle manufacturing, Tier 1 supply chain, and connected vehicle platforms rely on us to protect the cryptographic integrity of their products.
TRUSTED BY THE FORTUNE 500
4 of 5
Top Global Software Companies4 of 5
Top Financial Services3 of 5
Top Global Ranks3 of 4
Top Energy & UtilitiesWho We Serve?
We help automotive organizations of every type build cryptographic programs that protect vehicle safety, satisfy regulators, and secure the supply chain.
OEM Manufacturers
Securing vehicle software stacks, OTA pipelines, and connected service credentials at scale.
Tier 1 Suppliers
Managing signing keys, device certificates, and cryptographic provenance for vehicle components.
Tier 2 Suppliers
Ensuring firmware and embedded software meets ISO 21434 and OEM cryptographic requirements.
EV Platforms
Protecting charging infrastructure credentials, V2G communications, and energy transaction integrity.
Autonomous Developers
Securing sensor data pipelines, firmware signing, and connected infrastructure identity.
Telematics Companies
Managing certificates and encryption keys across large connected vehicle fleets.
vSOC Operators
Building cryptographic visibility into vehicle security monitoring and incident response programs.
Certification Bodies
Supporting type approval evidence collection and cryptographic compliance verification.
Discover Our
Latest Resources
- Blogs
- White Papers
- Videos
Post Quantum Cryptography
From Discovery to Action: How a Cryptographic Bill of Materials Turns Inventory into Intelligence
Stop treating your cryptographic inventory as a one-time project. Learn how a living CBOM turns discovery data into compliance evidence, risk prioritization, and a realistic PQC migration plan.
Read more
White Paper
The GDPR Playbook: Protecting Data, Ensuring Compliance, and Building Trust
The General Data Protection Regulation (GDPR) has fundamentally changed the way organizations collect, manage, and protect personal data. But navigating its requirements can be complex.
Read more
Video
From 50 to 9: NIST's Post-Quantum Signature Survivors
Explore expert insights on cybersecurity, PKI, and post-quantum readiness, with practical guidance to strengthen security and future-proof cryptography.
Watch Now