GOVERNMENT
Cryptographic Security Built for Public Sector Accountability
Government agencies hold the most sensitive data in existence. We help federal agencies, defense contractors, and state and local governments meet strict compliance mandates.
Trusted By
32,211
Security incidents reported by U.S. federal agencies in a single fiscal year$6.7M
Highest average ransomware demand across all sectors in Q1 202575%
Of government security failures attributed to poor management2030
NIST quantum-resistant encryption deadlineTHE PROBLEM
What’s Holding
Government Sector Back?
Legacy System Gaps
Decades of accumulated infrastructure was never designed for modern PKI or encryption standards, yet continues handling the most sensitive government data.
Identity and Privilege Risk
Shared credentials, over-privileged accounts, and poorly governed certificates are among the leading causes of government breaches year after year.
Overlapping Compliances
FISMA, FedRAMP, and CMMC impose continuously updated obligations requiring documented cryptographic controls and continuous monitoring across federal system.
Supply Chain Risk
Unsigned or unverified software delivered into government environments remains one of the highest-risk attack vectors across the federal contractor ecosystem.
Quantum Exposure
Intelligence collected today against RSA or ECC encryption stays exploitable when quantum computing matures, making early transition a national security obligation.
METHODOLOGY
Our Approach
Government cryptographic programs must satisfy strict compliance frameworks, protect national security data, and operate across complex multi-agency environments. We design every engagement around those realities:
01
Compliance as Outcome
FISMA, FedRAMP, NIST SP 800-53, and CMMC each carry distinct control requirements. We design products that produce audit ready evidence continuously, not periodically.
02
Authorization Boundary Aware
Government systems operate within defined authorization boundaries. We design cryptographic controls that respect those boundaries and integrate cleanly with existing ATOs.
03
Mission Critical Ready
National security data demands cryptographic protections that outlast today's threat model. We build CNSA 2.0 aligned post quantum readiness into every engagement from day one.
PRODUCTS
How We Help?
Applied Cryptography Products
CBOM Secure
Cryptographic Discovery & Inventory
Automated inventory of cryptographic assets across agency systems and contractor environments. Generates audit ready reports aligned to NIST SP 800-53, FISMA, and FIPS SP800 with up to 80% less manual effort.
CertSecure Manager
Certificate Lifecycle Management
Unified certificate visibility and lifecycle management across agency networks and multi-cloud environments. Prevents expirations from creating the access control gaps that drive government breaches.
PKI-as-a-Service
Scalable PKI Without Complexities
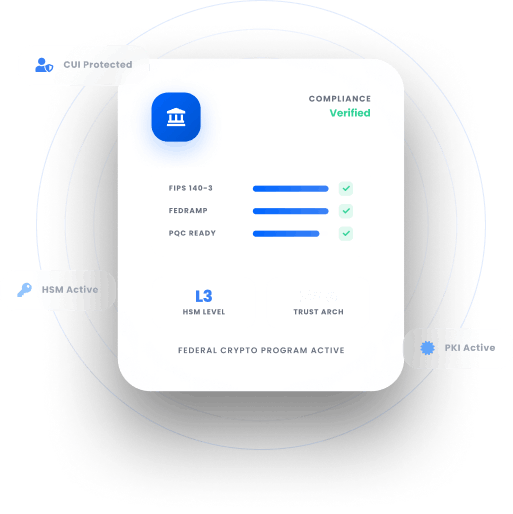
Fully managed, single tenant PKI on FIPS 140-3 Level 3 HSMs issuing trusted identities for agency users, systems, and devices across SCEP, EST, and ACME protocols.
HSM-as-a-Service
High Assurance HSM Solution
FIPS 140-3 certified HSM solutions protecting encryption keys and PKI root trust across on premises, FedRAMP-authorized cloud, or hybrid environments.
CodeSign Secure
Code Signing Solution
Ensures every software package and firmware update is cryptographically verified before deployment. Delivers HSM backed signing, FIPS 140-2 Level 3 compliance, and PQC ready support for MLDSA and LMS.
SERVICES
Expert-Led
Advisory & Implementation
Public Key Infrastructure Services
PKI assessments, CA architecture design, and certificate lifecycle management aligned to NIST SP 800-57, FISMA, and FedRAMP across agency and contractor environments.
Post Quantum Cryptography Services
Cryptographic inventory, quantum exposure analysis, and a migration roadmap aligned to NIST IR 8547 and NSA CNSA 2.0 for agencies where classified data demands earlier action.
Encryption Advisory Services
Assess your encryption posture across agency systems and contractor environments. Identify gaps against FIPS 140-3 and NIST SP 800-111, and receive a remediation roadmap.
Compliance Services
Gap assessments, remediation roadmaps, and compliance support across FISMA, FedRAMP, CMMC, NIST SP 800-53, and FIPS 140-3, backed by over 600 governance frameworks globally.
Why Encryption Consulting?
Federal Compliance Fluency
FISMA, FedRAMP, CMMC, and CNSA 2.0 each carry distinct requirements. We design programs that satisfy every framework and produce the audit evidence federal oversight bodies actually examine.
National Security Discipline
Government cryptographic programs carry implications no commercial engagement matches. We bring the documentation standards and control rigor that working in the federal environment demands.
No Vendor Ties
We are independent of Thales, Entrust, DigiCert, Microsoft ADCS, AWS GovCloud, Azure Government, and more. Our recommendations reflect your agency's mission, not a vendor relationship.
TRUSTED BY THE FORTUNE 500
4 of 5
Top Global Software Companies4 of 5
Top Financial Services3 of 5
Top Global Ranks3 of 4
Top Energy & UtilitiesWho We Serve?
We help government organizations of every type build cryptographic programs that protect sensitive data, satisfy compliance mandates, and support national security.
Federal Agencies
Securing subscriber identity and authentication across core and radio networks.
Defense Contractors
Protecting network infrastructure and customer data at scale.
Intelligence Contractors
Ensuring firmware integrity and cryptographic trust in network hardware.
State and Local
Building compliant PKI and encryption programs within constrained budgets and IT teams.
Law Enforcement
Securing digital evidence chains, identity credentials, and sensitive communications infrastructure.
Critical Infrastructure
Protecting cryptographic controls across government-regulated energy, water, and transport systems.
National Laboratories
Securing research data, controlled unclassified information, and classified computing environments.
Research Institutions
Managing cryptographic compliance across federally funded programs and sensitive data pipelines.
Discover Our
Latest Resources
- Blogs
- White Papers
- Videos
PKI
PKI Maintenance and Quarterly Cleanup for Microsoft CA
Learn how to perform PKI maintenance and quarterly cleanup for Microsoft CA, including CA database backup, certificate cleanup, offline compaction, and post-maintenance validation.
Read more
White Paper
Introduction to Code Signing
Learn the fundamentals of code signing, from digital signatures and certificate validation to time-stamping and application reputation. Discover how to secure your software supply chain, protect against tampering, and build long-term trust across enterprise and consumer environments.
Read more
Video
The 2026 Guide to Upgrading Enterprise PKI and HSMs for Post Quantum Security
Explore expert insights on cybersecurity, PKI, and post-quantum readiness, with practical guidance to strengthen security and future-proof cryptography.
Watch Now