SOFTWARE
Securing the Software That Powers Everyone
Software and IT companies are the most consequential targets. We help software vendors, SaaS providers, and IT organizations protect their products and the customers who trust them.
Trusted By
$60B
Estimated global cost of software supply chain attacks in 2025.30%
Of all data breaches involved a third party or supply chain compromise.267 days
Average time to identify and contain a supply chain breach.$4.91M
Average cost of a supply chain breach.THE PROBLEM
What’s Holding
Software & IT Sector Back?
Unsigned CI/CD Pipelines
Builds, packages, and containers ship without cryptographic signatures, leaving customers unable to verify what they deploy is what you released.
Certificate Sprawl
Thousands of certificates across APIs and cloud environments expire without warning, creating outages and security gaps customers discover before you do.
No Cryptographic Inventory
Customers, regulators, and government procurement require proof of cryptographic provenance. Most organizations have no systematic way to produce it.
Ungoverned Secrets
API keys, signing certificates, and encryption credentials accumulate without lifecycle management, becoming an unmanaged breach surface over time.
Quantum Debt
Cryptographic libraries embedded in software today will run in customer environments for years, shipping known future vulnerabilities into production.
METHODOLOGY
Our Approach
Software cryptographic programs must keep pace with release velocity, protect downstream customers, and address supply chain risk. We design every engagement around those realities:
01
Pipeline Integrated
We embed cryptographic governance directly into your development workflows without slowing release cadence.
02
Customer Accountability First
A cryptographic failure affects every customer running your code. We design programs built around that downstream responsibility.
03
Future Ready by Design
We build post quantum readiness into every engagement so your products do not become your customers' liability.
PRODUCTS
How We Help?
Applied Cryptography Products
CBOM Secure
Cryptographic Discovery & Inventory
Automated inventory of cryptographic assets across source code, binaries, and open source dependencies. Generates audit ready reports for enterprise customers, government procurement, and post quantum transition planning.
CertSecure Manager
Certificate Lifecycle Management
Unified certificate visibility and lifecycle management across cloud infrastructure, microservices, and APIs. Supports ACME, SCEP, and EST protocols to match your release velocity.
PKI-as-a-Service
Scalable PKI Without Complexities
Fully managed, single tenant PKI on FIPS 140-3 Level 3 HSMs issuing trusted identities for services, APIs, and infrastructure at modern software delivery velocity.
HSM-as-a-Service
High Assurance HSM Solution
FIPS 140-3 certified HSM solutions protecting signing keys, API secrets, and PKI root trust across cloud, on premises, or hybrid environments.
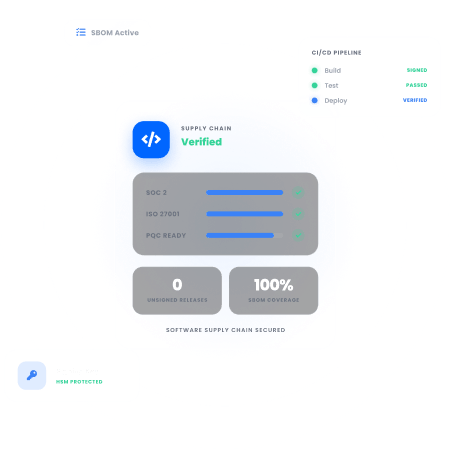
CodeSign Secure
Code Signing Solution
Ensures every release and container image is cryptographically signed before reaching customers. Delivers HSM backed signing, FIPS 140-2 Level 3 compliance, and PQC ready support for MLDSA and LMS.
SERVICES
Expert-Led
Advisory & Implementation
Public Key Infrastructure Services
PKI assessments, CA architecture design, and certificate lifecycle management for cloud-native microservices, developer self-service enrollment, and DevSecOps integration.
Post Quantum Cryptography Services
Cryptographic library inventory, quantum exposure analysis, and a migration roadmap to NIST algorithms for organizations where today's choices become tomorrow's customer liability.
Encryption Advisory Services
Assess your encryption posture across product code and APIs. Identify gaps against NIST, SOC 2, and ISO 27001, and receive a remediation roadmap.
Compliance Services
Gap assessments, remediation roadmaps, and compliance support across SOC 2, ISO 27001, NIST SP 800-218, and FedRAMP, backed by over 600 governance frameworks globally.
Why Encryption Consulting?
Built for Developers
We design cryptographic programs that work within your development environment and release cadence, not programs that require developers to work around security to ship.
Downstream Accountability
A cryptographic failure is a supply chain event affecting every customer running your code. We design programs built around that downstream responsibility from day one.
No Vendor Ties
We are independent of Thales, Entrust, DigiCert, Microsoft ADCS, AWS KMS, Azure Key Vault, and more. Our recommendations reflect your architecture and customer requirements, not a vendor relationship.
TRUSTED BY THE FORTUNE 500
4 of 5
Top Global Software Companies4 of 5
Top Financial Services3 of 5
Top Global Ranks3 of 4
Top Energy & UtilitiesWho We Serve?
We help software and IT organizations of every type build cryptographic programs that protect their products, secure their pipelines, and satisfy customers.
Software Vendors
Signing releases, managing certificates, and proving cryptographic provenance across every product shipped.
SaaS Providers
Securing API credentials, service identities, and encryption keys across multi-tenant cloud environments.
Managed Services
Building cryptographic governance into managed detection, response, and infrastructure platforms.
DevOps Teams
Embedding certificate management and code signing directly into CI/CD pipelines and workflows.
Open Source Maintainers
Protecting signing keys and package integrity across widely distributed software ecosystems.
IT Integrators
Securing cryptographic controls across customer deployments and third party system integrations.
Security Vendors
Ensuring cryptographic libraries, key management, and signing workflows meet the highest standards.
API Platforms
Managing certificates, secrets, and encryption keys across high-volume API infrastructure at scale.
Discover Our
Latest Resources
- Blogs
- White Papers
- Videos
PKI
PKI Maintenance and Quarterly Cleanup for Microsoft CA
Learn how to perform PKI maintenance and quarterly cleanup for Microsoft CA, including CA database backup, certificate cleanup, offline compaction, and post-maintenance validation.
Read more
White Paper
Introduction to Code Signing
Learn the fundamentals of code signing, from digital signatures and certificate validation to time-stamping and application reputation. Discover how to secure your software supply chain, protect against tampering, and build long-term trust across enterprise and consumer environments.
Read more
Video
The 2026 Guide to Upgrading Enterprise PKI and HSMs for Post Quantum Security
Explore expert insights on cybersecurity, PKI, and post-quantum readiness, with practical guidance to strengthen security and future-proof cryptography.
Watch Now