ENERGY
Protecting the Infrastructure That Powers Everything
Energy infrastructure powers economies and underpins national security. We help utilities, grid operators, and energy providers secure the cryptographic foundations the world depends on.
Trusted By
80%
Surge in ransomware attacks targeting the energy and utilities sector60
New vulnerable points added to the U.S. power grid every day21%
Of all ICS vulnerabilities discovered in 2024 and 2025 affected energy systems2030
NIST quantum-resistant encryption deadlineTHE PROBLEM
What’s Holding
Energy Industry Back?
IT and OT Convergence
The traditional air gap between enterprise IT and Operational Technology (OT) is largely gone, yet cryptographic controls for each environment were never designed to work together.
Unverified Control System
Control system firmware frequently arrives from vendors without cryptographic signatures, allowing tampered software to reach operational technology undetected.
Supply Chain Provenance
Substations, smart meters, and remote equipment carry certificates that are rarely inventoried or governed centrally, creating compliance gaps at massive scale.
Mandatory Type Approval
State-sponsored actors establish persistent access and wait, exploiting unmanaged credentials and weak cryptographic controls for years before detection.
Quantum Risk
NERC CIP mandates documented cryptographic controls across bulk electric assets. Manual processes cannot meet continuous monitoring requirements at grid scale.
METHODOLOGY
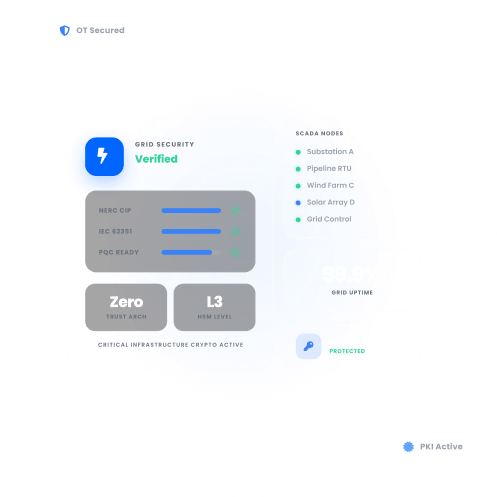
Our Approach
Energy cryptographic programs must span IT and OT environments, respect operational constraints, and defend against persistent threats. We design every engagement around those realities:
01
Grid Aware First
Every certificate and key spans IT networks, SCADA systems, and remote field assets. We map your full cryptographic footprint before recommending any changes.
02
Operationally Constrained
Energy systems run under strict availability requirements. We design cryptographic automation that works within maintenance windows, not around them.
03
Protected for Decades
Grid infrastructure installed today operates for decades. We build post quantum readiness into every engagement so protections remain sound for the asset's full lifetime.
PRODUCTS
How We Help?
Applied Cryptography Products
CBOM Secure
Cryptographic Discovery & Inventory
Automated inventory of cryptographic assets across control system software, vendor firmware, and enterprise IT. Generates audit ready reports aligned to NERC CIP, NIST SP 800-82, and FIPS SP800 with up to 80% less effort.
CertSecure Manager
Certificate Lifecycle Management
Unified certificate visibility and lifecycle management across substations, remote monitoring systems, and grid infrastructure. Prevents expirations in remote assets from silently compromising grid communications.
PKI-as-a-Service
Scalable PKI Without Complexities
Fully managed, single tenant PKI on FIPS 140-3 Level 3 HSMs issuing trusted identities for grid assets, remote systems, and operational staff.
HSM-as-a-Service
High Assurance HSM Solution
FIPS 140-3 certified HSM solutions protecting grid control credentials, SCADA signing keys, and PKI root trust across on premises, cloud, or hybrid environments.
CodeSign Secure
Code Signing Solution
Ensures every firmware release and control system update is cryptographically verified before reaching operational technology. Delivers HSM backed signing, FIPS 140-2 Level 3 compliance, and PQC ready support.
SERVICES
Expert-Led
Advisory & Implementation
Public Key Infrastructure Services
PKI assessments, CA architecture design, and certificate lifecycle management covering SCADA networks, substation automation, and distributed field infrastructure.
Post Quantum Cryptography Services
Cryptographic inventory, quantum exposure analysis, and a migration roadmap to NIST algorithms for energy operators where grid assets operate well past 2030.
Encryption Advisory Services
Assess your encryption posture across enterprise systems and control networks. Identify gaps against NERC CIP and NIST SP 800-82, and receive a remediation roadmap.
Compliance Services
Gap assessments, remediation roadmaps, and compliance support across NERC CIP, NIST SP 800-82, and NIS2, backed by over 600 governance frameworks globally.
Why Encryption Consulting?
Grid Security Expertise
We understand the difference between patching a web server and patching a substation controller. Every engagement accounts for the availability requirements unique to energy infrastructure.
Nation-State Threat Aware
Energy infrastructure attracts state-sponsored long-dwell attackers. Our cryptographic inventory and PQC advisory capabilities directly address persistent access patterns that have compromised operators globally.
Trusted at Scale
Organizations across electricity generation, transmission, oil and gas, and renewable energy rely on us to protect the cryptographic foundations of the systems they operate.
TRUSTED BY THE FORTUNE 500
4 of 5
Top Global Software Companies4 of 5
Top Financial Services3 of 5
Top Global Ranks3 of 4
Top Energy & UtilitiesWho We Serve?
We help energy organizations of every type build cryptographic programs that protect critical infrastructure, satisfy regulators, and defend against persistent threats.
Electric Utilities
Securing cryptographic controls across generation, transmission, and distribution infrastructure.
Grid Operators
Managing certificates and credentials across SCADA systems and substation automation networks.
Oil and Gas
Protecting pipeline control systems, operational credentials, and field device firmware integrity.
Renewable Energy
Securing wind, solar, and storage control systems and remote monitoring infrastructure.
Energy Traders
Encrypting transaction data and securing credentials across market-facing trading platforms.
Smart Grid Vendors
Signing firmware, managing device certificates, and meeting NERC CIP cryptographic requirements.
Nuclear Operators
Protecting air-gapped control systems, personnel credentials, and classified operational data.
Certification Bodies
Supporting cryptographic compliance verification across regulated operator environments.
Discover Our
Latest Resources
- Blogs
- White Papers
- Videos
PKI
PKI Maintenance and Quarterly Cleanup for Microsoft CA
Learn how to perform PKI maintenance and quarterly cleanup for Microsoft CA, including CA database backup, certificate cleanup, offline compaction, and post-maintenance validation.
Read more
White Paper
Introduction to Code Signing
Learn the fundamentals of code signing, from digital signatures and certificate validation to time-stamping and application reputation. Discover how to secure your software supply chain, protect against tampering, and build long-term trust across enterprise and consumer environments.
Read more
Video
The 2026 Guide to Upgrading Enterprise PKI and HSMs for Post Quantum Security
Explore expert insights on cybersecurity, PKI, and post-quantum readiness, with practical guidance to strengthen security and future-proof cryptography.
Watch Now