Let’s define NIST Cyber Security Framework in brief.
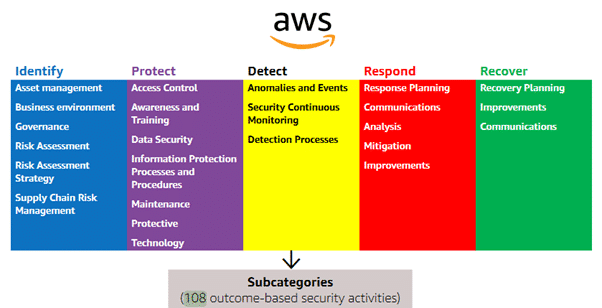
The NIST Cyber Security Framework known as NIST CSF is a cybersecurity assessment-type framework developed by the NIST (National Institute of Standards and Technology). The core purpose of the NIST CSF is to protect the nation’s critical infrastructure using a set of cybersecurity best practices and recommendations. It’s a voluntary, risk-based, and outcome-oriented cybersecurity framework to help your organization to categorize its security activities around five key functions 1) Identify 2) Protect, 3) Detect, 4) Respond, and 5) Recover.
Let’s look at each function briefly:
Identify – The Identify function assist you to evolve an overall cybersecurity risk management approach to systems, people, assets, data, and capabilities in the organization. It helps you to identify the critical assets, overall business environment, governance model, and supply chain.
Protect – The protect function helps you to set up defensive controls based on the inputs from identify function such as critical assets, risk tolerance/acceptance levels. It also emphasizes the importance of access control & identity management, protecting data, and training & awareness to users.
Detect – The detection functions help you to detect anomalies, malicious activities, and other events effectively by continuous security monitoring and with the help of other detection processes & procedures.
Respond – To complete the detection function, respond helps you to take the right action immediately through incident response planning, mitigation actions for events, accurate analysis, communication to the designated stakeholders, and continuous improvement with each event.
Recover – Recover function assists you to get back to the pre-attack condition with the help of recovery planning, continuous improvement, and communication to the designated stakeholders.
NIST Cyber Security Framework Overview: Core, Tiers, and Profile
The NIST CSF consists of three sections:
The core section represents cybersecurity practices, technical, operational, process security controls, and outcomes that support the five risk management functions such as Identify, Protect, Detect, Respond, and Recover.
The tiers section emphasizes the organization’s processes of managing risks while remaining aligned with NIST CSF.
The profiles characterize how effectively an organization’s cybersecurity program is managing its risk. It also expresses the state of an organization’s “as is” and ‘’to be’’ cybersecurity postures.
NIST Cyber Security Framework and AWS Cloud
Earlier AWS team published a guide on how to implement the NIST CSF in an AWS cloud environment. AWS recommends using NIST CSF as a mechanism to have baseline security in place that can improve the cloud security objectives of an organization. NIST CSF contains a comprehensive controls catalogue derived from the ISO/IEC 27001 (1), NIST SP 800-53 (2), COBIT (3), ANSI/ISA-62443 (4), and the Top 20 Critical Security Controls (CSC) (5).
There is a listing on the AWS portal that specifies the alignment of NIST CSF to various AWS services that are known as “AWS Services and Customer Responsibility matrix for Alignment to the CSF” (6). This is a comprehensive list that customers can use to align their needs with the CSF in the AWS cloud for their security requirements. Also, this enables the customer to design their baseline security requirements to meet their security goals.
AWS Cloud Adoption Framework
Before setting up a baseline, it is important for a customer to have a clear understanding of their business use cases and the customer-owned responsibilities for “security in the AWS cloud”. The customer should review the “AWS Cloud Adoption Framework” (7) to evaluate the governance model that will be required while implementing the NIST CSF into the AWS cloud services. The AWS CAF (Cloud Adoption Framework) lists pointers known as “CAF Perspectives” to identify gaps in security skills, capabilities, and cybersecurity processes.
NIST CSF Functions and Responsibilities (Customer-owned & AWS-owned)
AWS team has come up with the concept of NIST CSF Functions categories & sub-categories into 108-outcome based security activities. Every function depicts the Customer-owned and AWS-owned responsibilities that mean security of the cloud owned by AWS and security in the cloud owned by the Customer. Business owners/stakeholders can use the AWS link of “AWS Services and Customer Responsibility matrix for Alignment to the CSF” to tailor their needs as per the organization’s tiers and profile level in the CSF.
The below figure represents the CSF core functions (Identify, Protect, Detect, Respond, and Recover) with categories defined and those that have been converted to 108-outcome based security activities (8) by AWS.
Till now we have discussed the NIST CSF alignment with the AWS Cloud Services and how the customer can use CAF (Cloud Adoption Framework) to evaluate the skill gap, capability, and cybersecurity processes using the CAF Perspectives.
Let’s discuss how appropriate AWS services can be leveraged to set up effective Security Architecture using NIST Cyber Security Framework.
The table below provides a summarized view of AWS Cloud Services categorized into the NIST CSF Core Functions based on the nature of the service:
| # | Identify | Protect | Detect | Respond | Recover |
|---|---|---|---|---|---|
| 1 | Organizations | Shield | GuardDuty | CloudWatch | OpsWorks |
| 2 | Security Hub | Certificate Manager | Macie | Lambda | CloudFormation |
| 3 | Config | KMS | Inspector | Detective | S3 Glacier |
| 4 | Trusted Advisor | Network Firewall | Security Hub | CloudTrail | Snapshot |
| 5 | Systems Manager | WAF | Systems Manager | Archive | |
| 6 | Control Tower | Firewall Manager | Step Functions | CloudEndure Disaster Recovery | |
| 7 | CloudHSM | ||||
| 8 | IAM | ||||
| 9 | Direct Connect | ||||
| 10 | VPC | ||||
| 11 | Single-Sign-On |
Conclusion
Having the AWS Cloud Services aligned with the NIST CSF enables the customer to improve their cloud security posture with appropriate risk management and industry-compliant cloud services. Encryption Consulting, a leading cyber-security firm, offers various AWS and NIST related cybersecurity consulting Services catering to its customers a risk and security control maturity assessment based on the outlined standards. Encryption Consulting helps customers to get them familiarized with NIST CSF and AWS security tools & documentation and assist them in conducting a meaningful and quantifiable cybersecurity assessment while keeping the organization’s business goals intact.
Resources
- ISO/IEC 27001:2013, Information Technology – Security techniques – Information Security management systems – Requirements. ISO. Retrieved February 18, 2021, from: https://www.iso.org/standard/54534.html
- NIST Special Publication (SP) 800-53, Rev. 5, Security and Privacy Controls for Information Systems and Organizations. National Institute for Standards and Technology. Retrieved February 18, 2021, from: https://csrc.nist.gov/publications/detail/sp/800-53/rev-5/final
- Control Objectives for Information and Related Technology (COBIT), an ISACA Framework. Information Systems Audit and Control Association (ISACA). Retrieved February 18, 2021 from: https://www.isaca.org/resources/cobit
- ANSI/ISA-62443-2-4-2018 / IEC 62443-2-4:2015+AMD1:2017 CSV, Security for industrial automation and control systems. International Society of Automation (ISACA).
- The 20 CIS Controls & Resources. Center for Internet Security (CIS). Retrieved February 18, 2021, from: https://www.cisecurity.org/controls/cis-controls-list/
- AWS Services and Customer Responsibility Matrix for Alignment to the CSF can be downloaded from here: https://aws.amazon.com/compliance/nist/
- An overview of the AWS Cloud Adoption Framework (CAF), Ver. 2. Amazon Web Services, Inc.
- An overview of AWS capabilities that can be leveraged with NIST CSF: https://d1.awsstatic.com/whitepapers/compliance/NIST_Cybersecurity_Framework_CSF.pdf




