Certificate Outage Prevention
Prevent Certificate Outages
for Business Continuity.
Expired certificates take down applications silently and suddenly. Gain full visibility, automate renewals, and eliminate unplanned downtime across your entire certificate landscape.
Trusted By
72%
Experienced a certificate-related outage in the past year$50K–$250K
Lost per incident by 31% of organizations56.6%
Can't track certificate expiration dates5–24
Hours of Downtime from a single certificate-related incidentTHE PROBLEM
Why Do Outages
Keep Happening
Certificate sprawl, manual processes, and blind spots turn routine expirations into costly incidents.
No Centralized Visibility
Certificates scattered across on-prem, cloud, and hybrid environments go untracked, creating blind spots that trigger unexpected outages.
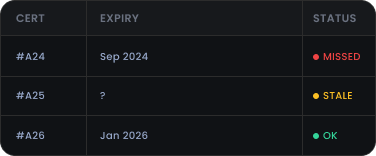
Spreadsheet-Driven Tracking
Manual inventories cannot scale with thousands of certificates, resulting in missed renewals, stale data, and increased operational risk.
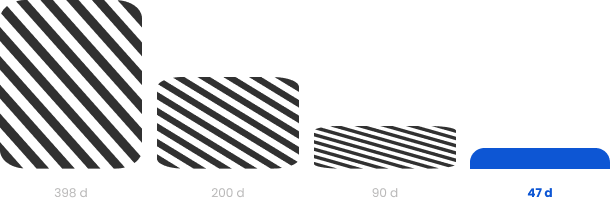
Shrinking Lifespans
With TLS validity dropping to 47 days by March 2029, manual renewal processes will collapse under the volume, making automation non-negotiable.
Rogue & Shadow Certificates
Unmanaged certificates issued outside approved processes go undetected, widening the attack surface and creating compliance gaps that auditors flag.
Weak Integration Support
Certificate silos disconnected from ITSM, DevOps, and cloud platforms slow response times and create coordination failures during critical renewal windows.

THE STRATEGY
How to Address This
Strategically
Preventing certificate-related outages requires more than reactive monitoring. Continuous discovery, automated renewals, and proactive alerting must work together to ensure certificate expiration is never the cause of an outage.
Continuous Discovery
Every environment including on-prem, cloud, and containers must be continuously scanned to maintain a real-time, accurate certificate inventory without manual effort.
Zero-Touch Renewals
The full renewal lifecycle must be automated using ACME, SCEP, and EST protocols to eliminate manual intervention and close the window for expiration-driven outages.
Proactive Alerting
Automated alerts, ticketing integrations, and escalation workflows must be triggered well ahead of expiration so the right teams act before services are impacted.
Policy Enforcement
Organization-wide certificate policies covering algorithm restrictions, approval workflows, and compliance requirements must be defined and enforced from a single central management platform.
Expert-Led Remediation
Root cause analysis, PKI architecture fixes, and remediation guidance must be backed by certified practitioners, so the underlying issue is fixed, not just the immediate alert.
This is how Encryption Consulting keeps certificate infrastructure running, before expiration ever becomes an incident.
A certificate expiration doesn't sneak up on you — it's always there on the calendar. The problem is nobody owns it. It sits between security, IT, and DevOps, and everyone assumes someone else is watching. That gap is where outages happen. We close that gap by giving teams the visibility and automation they need, so expiration is never a surprise, let alone a crisis.
Products & Services
How We Support
Your Security Journey
CertSecure Manager
Certificate Lifecycle Management
Unified CLM platform for automated discovery, renewal, and policy enforcement across all CA types and environments.
PKI-as-a-Service
Scalable PKI Without Complexities
Fully managed, scalable PKI infrastructure that eliminates internal CA complexity and guarantees certificate issuance with no planned downtime.
CBOM Secure
Cryptographic Discovery & Inventory
Deterministic cryptographic discovery to surface unmanaged and rogue certificates before they become outage or compliance risks.
Public Key Infrastructure Services
Expert advisory and implementation services to design, audit, and optimize PKI environments for reliability and operational resilience.
Compliance Services
Identify certificate-related compliance gaps across PCI-DSS, HIPAA, and GDPR frameworks and remediate them with structured guidance.
TRUSTED BY THE FORTUNE 500
4 of 5
Top Global Software Companies4 of 5
Top Financial Services3 of 5
Top Global Ranks3 of 4
Top Energy & UtilitiesWhy Encryption Consulting
PKI-Native Expertise
Every solution is built and backed by practitioners with 20+ years of applied cryptography experience, not generalist IT vendors retrofitting PKI features.
Vendor-Neutral Platform
CertSecure Manager manages certificates across public and private CAs in one dashboard, no vendor lock-in, full coverage from day one.
Designed for Longevity
Crypto-agile architecture and built-in PQC readiness mean your outage prevention investment protects you today and scales into the post-quantum era seamlessly.
Discover Our
Latest Resources
- Blogs
- White Papers
- Videos
Code Signing
Integrating Post Quantum Cryptography into Code Signing Workflows
Discover how to future-proof your code signing workflows with post-quantum cryptography before quantum threats become real. At Encryption Consulting, we specialize in PKI, encryption, and certificates of all types.
Read more
White Paper
The PQC Signature Selection Playbook
Which NIST post-quantum signature fits your code-signing workflow? Compare ML-DSA, SLH-DSA, and draft FN-DSA variants in one practical reference.
Read more
Video
How to Automate Certificate Renewal with BIG-IP F5 Load Balancer
Explore expert insights on cybersecurity, PKI, and post-quantum readiness, with practical guidance to strengthen security and future-proof cryptography.
Watch Now









