Managing Cryptographic Posture
Cryptographic Clarity,
Across Every Environment.
Turn scattered certificates, keys, and algorithms into a unified, governed cryptographic posture – built for compliance, resilience, and the quantum transition ahead.
Trusted By
73%
of organizations cannot fully inventory their cryptographic assets.47 Days
Maximum TLS certificate lifespan, effective March 2029.59%
Lack the expertise to assess, plan, and implement crypto-agility.2030
Estimated Q-Day deadline.THE PROBLEM
Why Cryptographic Posture
Breaks Down
Across industries, the same gaps surface. Visibility, control, and coordination are consistently absent when cryptography is treated as a background function.
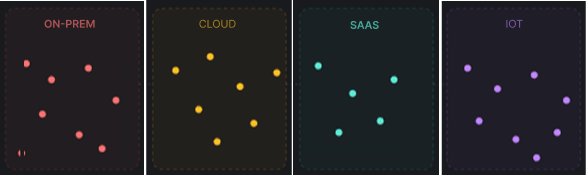
No Unified Visibility
Cryptographic assets scattered across hybrid environments make it hard to assess exposure or enforce consistent policy without a central inventory.
Manual Lifecycle Gaps
Teams relying on manual tracking cannot sustain the velocity that future 47-day certificate cycles and continuous compliance demands require.
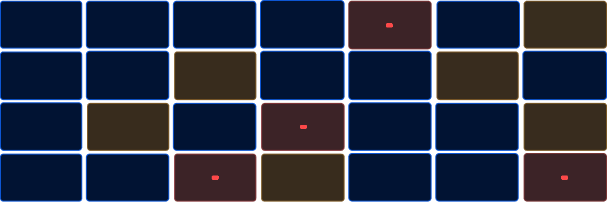
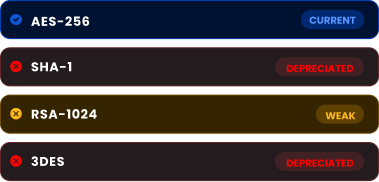
Algorithm Sprawl
Deprecated and inconsistent cryptographic algorithms coexist across applications, creating silent vulnerabilities that evade standard security assessments entirely.
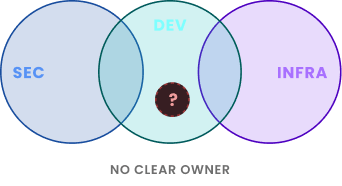
Fragmented Ownership
Cryptography responsibilities split between DevOps, security, and infrastructure teams produce blind spots, duplication of effort, and no clear accountability for posture.
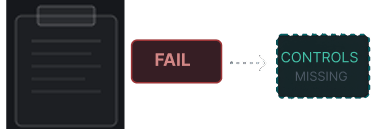
Compliance Without Proof
Auditors and regulators increasingly require demonstrable cryptographic controls. Organizations without automated evidence collection consistently fail assessments.
THE STRATEGY
How to Address This
Strategically
Managing cryptographic posture requires continuous discovery, risk-informed prioritization, and the operational maturity to enforce policy at scale, across every environment, every certificate, and every key.
Cryptographic Discovery & CBOM
A full environment scan must produce a Cryptographic Bill of Materials covering every certificate, key, algorithm, and dependency. No posture program can be built on partial visibility.
Risk-Based Asset Prioritization
Every cryptographic asset must be scored for algorithm weakness, expiration proximity, and compliance exposure so security teams can direct remediation effort where business impact is greatest.
Enforceable Cryptographic Policy
Cryptographic standards must be formally defined and enforced through automation because policy that lives in documentation but not in controls will always produce configuration drift.
Automated CLM
Certificate issuance, renewal, and revocation must be fully automated to eliminate manual tracking, reduce human error, and ensure no certificate expires unnoticed across any environment.
Audit Readiness
Cryptographic posture must be monitored continuously, not assessed annually, with compliance metrics tracked in real time and audit-ready reporting generated without manual evidence collection.
This is the approach Encryption Consulting takes to secure cryptographic postures across industries.
Cryptographic posture isn't a project you complete. It's a discipline you build. The organizations that understand that are the ones who stop chasing individual certificate fires and start thinking about the underlying system: the inventory, the policy, the automation, the ownership. That shift in thinking is what separates teams that are always reacting from teams that are actually in control. Getting organizations to that second place, and keeping them there as the threat landscape changes around them, is what we built Encryption Consulting to do.
Products & Services
How We Support
Your Security Journey
CBOM Secure
Cryptographic Discovery & Inventory
Deterministic cryptographic discovery and inventory that maps every certificate, key, and algorithm across hybrid environments to produce an audit-ready Cryptographic Bill of Materials.
CertSecure Manager
Certificate Lifecycle Management
Automated CLM that handles issuance, renewal, and revocation at the velocity the industry requires, eliminating manual tracking and certificate-related outages entirely.
SSH Secure
SSH Key Lifecycle Management
Automates SSH key discovery, lifecycle management, and policy enforcement across your infrastructure, eliminating orphaned keys and unauthorized access risks.
HSM-as-a-Service
High Assurance HSM Solution
Managed hardware security module infrastructure for secure key generation, storage, and cryptographic operations, without the overhead of deploying and maintaining on-premises HSMs.
Encryption Advisory Services
Strategic cryptographic advisory that assesses your current posture, identifies risk concentrations, and builds a prioritized roadmap aligned to your compliance and operational requirements.
PQC Advisory Services
Expert guidance on algorithm selection, migration sequencing, and quantum-readiness planning, ensuring your posture improvement roadmap accounts for the cryptographic transition already underway.
Public Key Infrastructure Services
End-to-end PKI assessment, design, and managed services to build the issuing infrastructure that reliable, scalable cryptographic posture management depends on at its foundation.
TRUSTED BY THE FORTUNE 500
4 of 5
Top Global Software Companies4 of 5
Top Financial Services3 of 5
Top Global Ranks3 of 4
Top Energy & UtilitiesWhy Encryption Consulting
Cryptography-First Expertise
Posture management requires more than tooling; it demands cryptographic judgment. Our team brings deep algorithm-level expertise that informs every discovery, prioritization, and migration decision we make.
Visibility Before Everything
Every engagement starts with cryptographic discovery because planning without an accurate inventory produces roadmaps that don't reflect reality, and remediation that leaves the highest-risk assets untouched.
CLM + PQC Approach
The 47-day certificate mandate and post-quantum migration share the same foundations. We plan both together so your posture investments serve both requirements without building the same infrastructure twice.
Discover Our
Latest Resources
- Blogs
- White Papers
- Videos
Code Signing
Integrating Post Quantum Cryptography into Code Signing Workflows
Discover how to future-proof your code signing workflows with post-quantum cryptography before quantum threats become real. At Encryption Consulting, we specialize in PKI, encryption, and certificates of all types.
Read more
White Paper
The PQC Signature Selection Playbook
Which NIST post-quantum signature fits your code-signing workflow? Compare ML-DSA, SLH-DSA, and draft FN-DSA variants in one practical reference.
Read more
Video
How to Automate Certificate Renewal with BIG-IP F5 Load Balancer
Explore expert insights on cybersecurity, PKI, and post-quantum readiness, with practical guidance to strengthen security and future-proof cryptography.
Watch Now









