Securing DevOps
Certificate Management and Code Signing for
DevOps and CI/CD Pipelines.
Most DevOps pipelines lack a consistent process for certificate issuance, key storage, and code signing. Security steps that do not fit the workflow get skipped, resulting in expired certificates, unsigned releases, and misplaced private keys.
Trusted By
78%
of DevOps pipelines rely on manual processes.9
Average certificate-related incidents organizations faced in the past year.72%
Experienced a certificate-related outage in the past year.48%
Push vulnerable code to production due to deadline pressure.THE PROBLEM
Why Certificate Security Is Hard to
Get Right in DevOps
DevOps environments create specific certificate and key management problems that traditional security processes were not built to handle.
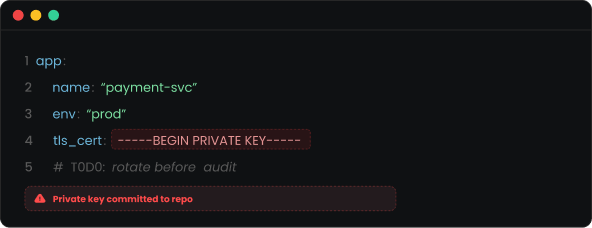
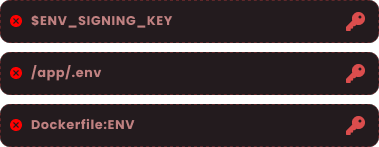
Certificates End Up Hardcoded
When certificate requests require manual steps outside the pipeline, developers store private keys or secrets directly in code or configuration files where they cannot be tracked or rotated.
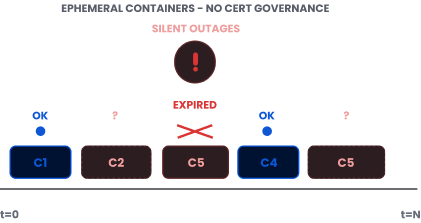
Containers Have No Certificate Lifecycle
Containers spin up quickly but rarely have certificate issuance or renewal in place. Expired certificates in containerized environments cause outages that go undetected until services fail.
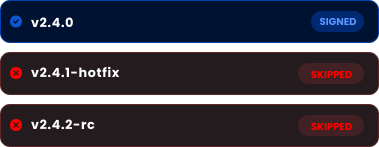
Code Signing Gets Bypassed
When signing adds friction to a release, it gets skipped. Software ships without verification, creating tampering exposure that is hard to detect after deployment.
Private Keys End Up in the Wrong Places
Keys for signing and encryption frequently end up in environment variables or config files. One misconfiguration exposes that key to everyone with repository access.
Security-Development Gap
Security teams set policies that development teams lack the tools to follow. Policies exist on paper but rarely make it into actual releases.
THE STRATEGY
How to Address This
Strategically
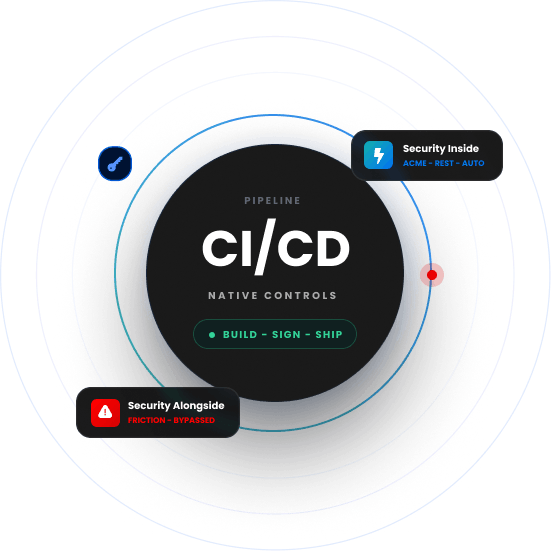
Securing a DevOps environment is not about adding security checkpoints that slow releases down. It is about putting certificate issuance, key protection, and code signing in the right places inside the pipeline so developers can work without creating risk on every build.
Pipeline-Native Issuance
Certificate issuance and renewal must integrate directly into CI/CD pipelines so developers never leave their existing tools.
Container Certificate
Every container that starts must have a valid, properly issued certificate, with expiries tracked and renewed automatically.
Code Signing in the Build
Code signing must be integrated into the build pipeline with HSM-stored keys and every signing event logged and auditable.
Structured Key and Secrets Management
Keys and secrets must be moved out of environment variables and configuration files into policy-driven storage with proper access controls.
Policies that Work Inside the Pipeline
Certificate and key management policies must fit inside existing DevOps workflows rather than running alongside them as a separate process.
This is the approach that Encryption Consulting takes to secure every DevOps environment, without slowing the pipeline down.
Developers are not the problem. When a private key ends up in a config file or a container ships without a valid certificate, it is almost never because someone was careless — it is because the secure path was harder than the fast path. We design security controls that live inside the pipeline, not alongside it. When signing a release or requesting a certificate is just part of how the build works, developers do the right thing automatically. That is the only security that actually holds in a DevOps environment.
Products & Services
How We Support
Your Security Journey
CertSecure Manager
Certificate Lifecycle Management
Automates certificate issuance and renewal for DevOps environments using ACME and REST APIs, integrating directly into CI/CD pipelines without adding manual steps or delays.
CodeSign Secure
Code Signing Solution
Integrates code signing into build pipelines with HSM-protected signing keys, ensuring every software release is signed, verifiable, and auditable without adding friction to the release process.
SSH Secure
SSH Key Lifecycle Management
Manages SSH key lifecycle across CI/CD pipelines with hardware-backed storage and controlled, auditable server connections, ensuring keys are securely generated, rotated, and governed without disrupting pipeline operations.
HSM-as-a-Service
High Assurance HSM Solution
Hardware-backed key protection for the private keys used in DevOps pipelines, without the operational overhead of managing on-premises HSM infrastructure.
PKI-as-a-Service
Scalable PKI Without Complexities
A fully managed PKI that issues private certificates for DevOps workloads, containers, and internal services at scale, with no rate limits or volume caps.
Public Key Infrastructure Services
Advisory and implementation services to design a PKI architecture that supports DevOps environments, from container certificate management to pipeline key governance.
TRUSTED BY THE FORTUNE 500
4 of 5
Top Global Software Companies4 of 5
Top Financial Services3 of 5
Top Global Ranks3 of 4
Top Energy & UtilitiesWhy Encryption Consulting
Inside the Pipeline
We integrate certificate, key, and code signing controls into existing CI/CD workflows. Security becomes part of how the team ships rather than a separate process that runs alongside it and gets worked around.
Built for Developers
Security that creates friction gets bypassed. Every control we put in place is designed to work inside existing developer tools without requiring PKI expertise or manual security team involvement for routine certificate requests.
Keys Stay in Hardware
Every signing key, certificate private key, and secrets credential we manage is protected by hardware security. Private keys do not sit in configuration files, environment variables, or poorly configured secrets managers.
Discover Our
Latest Resources
- Blogs
- White Papers
- Videos
Code Signing
Integrating Post Quantum Cryptography into Code Signing Workflows
Discover how to future-proof your code signing workflows with post-quantum cryptography before quantum threats become real. At Encryption Consulting, we specialize in PKI, encryption, and certificates of all types.
Read more
White Paper
The PQC Signature Selection Playbook
Which NIST post-quantum signature fits your code-signing workflow? Compare ML-DSA, SLH-DSA, and draft FN-DSA variants in one practical reference.
Read more
Video
How to Automate Certificate Renewal with BIG-IP F5 Load Balancer
Explore expert insights on cybersecurity, PKI, and post-quantum readiness, with practical guidance to strengthen security and future-proof cryptography.
Watch Now









