Crypto-Agility
Build the Capability to Change Your Cryptographic Foundation
Without Breaking Anything.
Deprecated algorithms, compliance deadlines, and quantum migration all become manageable when the cryptographic foundation underneath them was built to handle change.
Trusted By
35%
Maintain a centralized cryptographic asset inventory54%
Operating on infrastructure that lacks compatibility with modern standards60%
Not prepared to respond to a critical cryptographic vulnerability59%
Lack the expertise to assess, plan, and implement crypto-agilityTHE PROBLEM
Why Crypto-Agility Is Harder
Than It Looks
Most organizations have cryptography spread across dozens of systems, applications, and environments. Updating it sounds straightforward. In practice it rarely is.
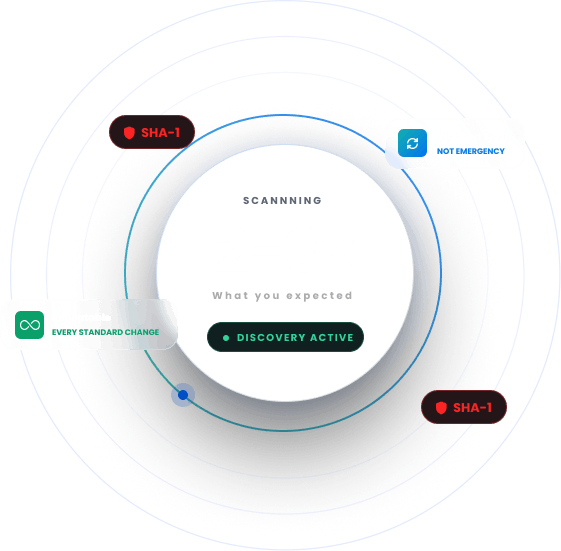
Lacking an Inventory
You cannot update what you have never found. Most organizations do not have a complete, accurate record of the algorithms, certificates, and keys running across their environment.

Hardcoded Cryptography
Algorithms get embedded in application code, configuration files, and legacy systems. When a standard gets deprecated, finding every instance takes longer than most teams expect.
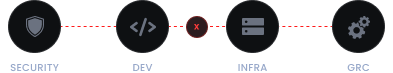
No Clear Process in Place
Replacing a cryptographic algorithm touches security, development, infrastructure, and compliance. Without a clear process, it becomes a coordination problem that stalls before it starts.
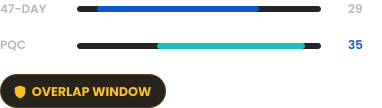
Two Transitions, One Timeline
The 47-day certificate mandate and the post-quantum migration are running on overlapping timelines. Organizations that treat them as separate projects will end up doing the same work twice.
Compliance Deadlines
NIST, NSA, and the European Commission have all set timelines for cryptographic transitions. Organizations without crypto-agility built into their infrastructure will scramble when those deadlines arrive.
THE STRATEGY
How to Address This
Strategically
Crypto-agility is not a product you buy. It is a capability you build. Getting there requires putting the right discovery, governance, and automation in place so that when cryptographic standards change, updating them becomes a planned, repeatable process rather than an emergency response.
Full Cryptographic Inventory
Before anything else can change, you need to know what you have. This means surfacing every algorithm, certificate, key, and library across your environment, so nothing gets left behind during a transition.
Risk Prioritization
Not everything needs to change at the same rate. Cryptographic assets must be mapped against current and upcoming standards, so teams can prioritize the highest-risk areas and work through the rest in order.
Building Repeatable Processes
Governance and automation must be in place so that updating cryptographic standards becomes a repeatable operational process rather than a one-off project every time something changes.
Plan PQC and the 47-Day Shift Together
Both transitions require visibility, automation, and governance. Planning them together cuts duplication and overall project cost.
Get Ahead of Regulatory Timelines
Working through NIST and NSA migration timelines before they become urgent ensures your team is not scrambling when deadlines take effect.
This is how Encryption Consulting approaches every crypto-agility engagement.
We've seen organizations spend months scrambling to replace a single deprecated algorithm. That's not a technology problem - that's a preparedness problem. Crypto-agility is really about asking yourself: if we had to change our cryptographic foundation tomorrow, could we? Most can't. That's what we help fix.
Products & Services
How We Support
Your Security Journey
CBOM Secure
Cryptographic Discovery & Inventory
Builds the cryptographic inventory that crypto-agility depends on. Every algorithm, certificate, key, and library across your environment, in one place.
SSH Secure
SSH Key Lifecycle Management
Automates SSH key discovery, lifecycle management, and policy enforcement across your infrastructure, eliminating orphaned keys and unauthorized access risks.
CertSecure Manager
Certificate Lifecycle Management
Automates certificate lifecycle management so that when certificate standards change, renewals and replacements happen without manual effort across every environment.
Encryption Advisory Services
Strategic advisory to assess your current cryptographic posture, identify gaps in your agility, and build a roadmap to fully crypto-agile operations.
PQC Advisory Services
Expert guidance on planning and executing your post-quantum migration, including algorithm selection, timeline planning, and transition sequencing across your infrastructure.
PKI Services
Hands-on PKI design and implementation to make sure your underlying infrastructure can support rapid cryptographic changes without rebuilding from scratch every time standards shift.
TRUSTED BY THE FORTUNE 500
4 of 5
Top Global Software Companies4 of 5
Top Financial Services3 of 5
Top Global Ranks3 of 4
Top Energy & UtilitiesWhy Encryption Consulting
Cryptographic Foundation
Crypto-agility is not a topic we cover alongside broader IT strategy. Applied cryptography is the entire focus of our practice, and the advice you get is grounded in direct, hands-on experience.
Covering the Full Scope
Crypto-agility touches discovery, certificate management, PKI architecture, PQC planning, and compliance. We cover all of it. You work with one team across the full transition instead of coordinating separate vendors for each piece.
Working With What You Have
Our tools and advisory services are built to integrate with your existing infrastructure and tooling. Getting to crypto-agility does not require you to replace your current stack. It requires you to add visibility, governance, and automation on top of it.
Discover Our
Latest Resources
- Blogs
- White Papers
- Videos
Code Signing
Integrating Post Quantum Cryptography into Code Signing Workflows
Discover how to future-proof your code signing workflows with post-quantum cryptography before quantum threats become real. At Encryption Consulting, we specialize in PKI, encryption, and certificates of all types.
Read more
White Paper
The PQC Signature Selection Playbook
Which NIST post-quantum signature fits your code-signing workflow? Compare ML-DSA, SLH-DSA, and draft FN-DSA variants in one practical reference.
Read more
Video
How to Automate Certificate Renewal with BIG-IP F5 Load Balancer
Explore expert insights on cybersecurity, PKI, and post-quantum readiness, with practical guidance to strengthen security and future-proof cryptography.
Watch Now









