47-Day Certificate Readiness
The Industry Is Moving to 47-Day Certificates.
Is Your Team Ready for It?
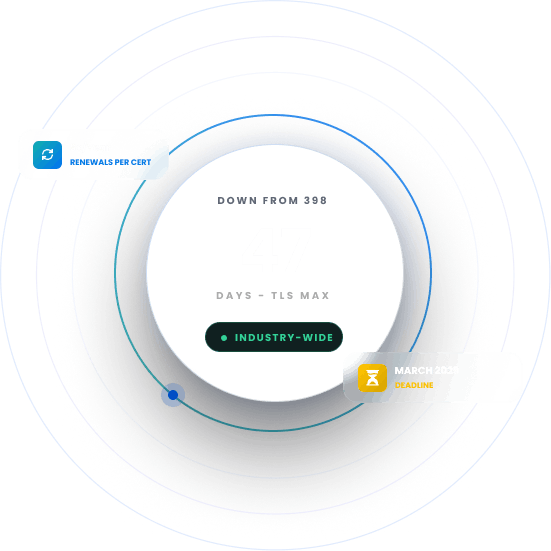
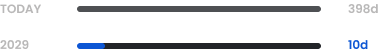
TLS certificate lifespans are shrinking fast. The maximum lifespan dropped to 200 days on March 15, 2026, will fall further to 100 days by March 2027, and will reach just 47 days by March 2029.
Trusted By
47
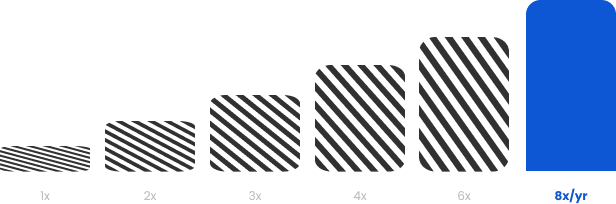
Days Maximum TLS certificate lifespan effective March 20298x
More renewals required per year than today’s typical annual cycle56.6%
Already struggle to track certificate expiration dates$2.8M
Average cost of a certificate-related breachTHE PROBLEM
Why Most Organizations Aren’t Ready for the
47-Day Certificate Deadline
Most teams are already stretched managing certificates at current volumes. The move to 47-day lifespans does not just increase renewal frequency; it also exposes every gap in your existing process.
Manual Processes Break Down
Renewing certificates 8 times a year per certificate is not a task spreadsheets or calendar reminders can handle reliably at any scale.
Inventory Gaps Get Worse
Teams that lack a complete view of their certificate estate today will face compounding blind spots as renewal windows shrink to weeks.
DevOps Pipelines Get Blocked
Without automation in place, certificate renewals become a bottleneck that delays deployments and disrupts release cycles.
Domain Validation Pressure
By March 2029, domain control validation reuse periods drop to 10 days, compounding the pressure of shorter certificate lifespans.
Compliance Risk Grows
Frameworks like PCI-DSS, HIPAA, and GDPR require valid certificates. More renewals mean more opportunities for gaps.

THE STRATEGY
How to Address This
Strategically
The shift to 47-day certificates is not just a compliance deadline. It is the moment automation stops being optional. Organizations need to build an infrastructure to handle short-lived certificates without adding headcount or operational burden.
Certificate Discovery First
A full inventory of every certificate across the environment is required before any automation can be reliably deployed.
Automation by Protocol
ACME, SCEP, and EST-based automation must be implemented so certificates renew on schedule without human intervention.
PKI Architecture Review
The underlying PKI must be assessed for its ability to handle significantly higher issuance volumes generated by short-lived certificates.
Policy and Governance
Renewal policies, ownership rules, and escalation workflows must be defined and enforced before automation goes live.
PQC Readiness Alongside
The 47-day transition and PQC migration are happening at the same time and must be planned together to avoid duplicating infrastructure decisions.
This is the approach Encryption Consulting brings to every 47-day certificate lifecycle engagement.
When I heard 47 days, the first thing I thought was, most organizations can't even tell you how many certificates they have, let alone renew them every six weeks. This isn't just a deadline; it's a forcing function. The teams that treat it that way and automate now will be fine. Everyone else is going to have a very hard 2029. We're here to make sure our clients are in the first group.
Products & Services
How We Support
Your Security Journey
CertSecure Manager
Certificate Lifecycle Management
Automates certificate issuance, renewal, and deployment at scale using ACME, SCEP, and EST protocols — built for high-frequency renewal cycles.
PKI-as-a-Service
Scalable PKI Without Complexities
A fully managed PKI built to handle the increased issuance load that comes with 47-day certificate lifespans, without requiring internal infrastructure changes.
CBOM Secure
Cryptographic Discovery & Inventory
Discovers every certificate across your environment so you know exactly what needs to be brought under automated management before the deadline hits.
Public Key Infrastructure Services
Hands-on advisory to assess your current PKI, identify gaps in your renewal process, and build a migration plan ahead of the first reduction deadline in March 2029.
PQC Advisory Services
Plan your post-quantum migration alongside the 47-day transition so both are handled together rather than as separate projects.
TRUSTED BY THE FORTUNE 500
4 of 5
Top Global Software Companies4 of 5
Top Financial Services3 of 5
Top Global Ranks3 of 4
Top Energy & UtilitiesWhy Encryption Consulting
Cryptography is Our Foundation
Certificate management and PKI are not services we expanded into. They are what Encryption Consulting was built to do, grounded in applied cryptography from the very start.
No Infrastructure Overhaul Required
CertSecure Manager integrates with your existing CA, ITSM, and DevOps tooling. You get automation without having to rebuild your infrastructure from the ground up.
One Team for the Full Transition
From certificate discovery to PQC readiness, we cover the full scope of what is changing. You work with one team instead of coordinating multiple vendors across overlapping projects.
Discover Our
Latest Resources
- Blogs
- White Papers
- Videos
Code Signing
Integrating Post Quantum Cryptography into Code Signing Workflows
Discover how to future-proof your code signing workflows with post-quantum cryptography before quantum threats become real. At Encryption Consulting, we specialize in PKI, encryption, and certificates of all types.
Read more
White Paper
The PQC Signature Selection Playbook
Which NIST post-quantum signature fits your code-signing workflow? Compare ML-DSA, SLH-DSA, and draft FN-DSA variants in one practical reference.
Read more
Video
How to Automate Certificate Renewal with BIG-IP F5 Load Balancer
Explore expert insights on cybersecurity, PKI, and post-quantum readiness, with practical guidance to strengthen security and future-proof cryptography.
Watch Now









