Cryptographic Inventory
Your Cryptographic Environment Has More in It
Than Your Team Realizes.
Certificates, keys, and algorithms accumulate across your environment faster than most teams realize. Organizations that gain full visibility move from reactive to resilient and stay ahead of risks others never see coming.
Trusted By
37%
Organizations have no centralized inventory.48%
Have partial/fragmented inventory.59%
Lack the expertise to assess, plan, and implement crypto-agility.60%
Are not prepared to respond to critical cryptographic vulnerability.THE PROBLEM
Why Cryptographic Discovery Is a Problem
Most Teams Have Not Solved
Organizations grow fast. Systems get added, cloud environments expand, and development teams spin up new services. This results in cryptographic assets accumulating faster than anyone can track them.
Incomplete Visibility
Certificates, keys, and algorithms are spread across servers, cloud platforms, containers, and applications with no central inventory. Nobody has the full picture.

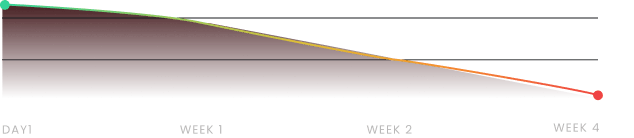
Unscalable Approach
Manually built inventories degrade within weeks as new assets are issued or systems change. The gaps they leave behind are often what drive the next incident.
Shadow and Rogue Assets
Certificates and keys issued outside approved channels go undetected for months or years. They create vulnerabilities that internal teams do not know to look for.
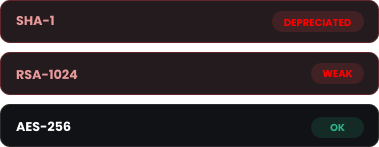
Outdated Algorithms
Many organizations are still running cryptographic algorithms that no longer meet current security standards. Without discovery, there is no way to know where they are or how many exist.
Compliance Requirements
Frameworks like PCI-DSS and GDPR, alongside NIST standards (SP 800-57, SP 800-131A), require organizations to demonstrate control over their cryptographic assets. You cannot prove compliance for assets you have not found.

THE STRATEGY
How to Address This
Strategically
Addressing cryptographic risk strategically requires more than running a scan. Organizations need a deterministic discovery process, one that finds what is in the environment, and produces a foundation for ongoing governance.
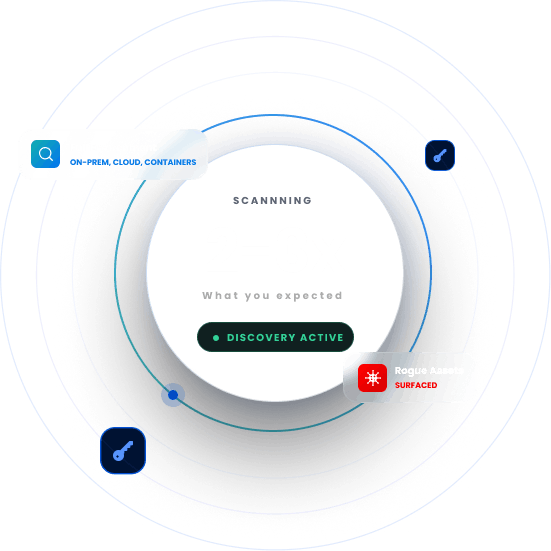
Full Environment Scanning
Scan across on-prem infrastructure, hybrid environments, multi-cloud deployments, and containerized workloads to surface every cryptographic asset in scope.
Full Cryptographic Check
Discovery is not just about finding certificates. It's also about identifying every algorithm, protocol, and library in use and flagging anything that falls outside current standards or your internal policy.
Rogue Asset Detection
Surface certificates and keys that were issued outside approved processes, giving your security team visibility into assets they did not know to look for.
Compliance Gap Mapping
Map findings against the standards and regulations relevant to your business, so you know exactly where you stand and what needs to change.
CBOM Generation
Produce a Cryptographic Bill of Materials, giving your organization a structured, auditable record of every cryptographic asset across your environment.
This is the approach Encryption Consulting brings to every cryptographic discovery engagement.
Every organization I've spoken to believes they know what's running in their environment. Then we do a discovery and the number is always two to three times what they expected. Rogue certificates, forgotten keys, shadow PKI nobody documented. You cannot protect what you don't know exists. Cryptographic inventory isn't the glamorous part of security, but it's the foundation everything else is built on. We make sure that foundation is solid.
Products & Services
How We Support
Your Security Journey
CBOM Secure
Cryptographic Discovery & Inventory
Encryption Consulting was built on applied cryptography. Knowing what cryptographic assets an organization runs, where they live, and whether they are secure has been central to our work from day one.
CertSecure Manager
Certificate Lifecycle Management
Once certificates are discovered, CertSecure Manager brings them under centralized lifecycle management so every certificate remains tracked and managed.
SSH Secure
SSH Key Lifecycle Management
Automates SSH key discovery, lifecycle management, and policy enforcement across your infrastructure, eliminating orphaned keys and unauthorized access risks.
Encryption Advisory Services
Expert advisory to help your organization understand what your cryptographic inventory reveals and build a remediation plan around the findings.
Compliance Services
Map your cryptographic posture against PCI-DSS, NIST, GDPR, and other relevant frameworks and close the gaps before your next audit.
PQC Advisory Services
Your cryptographic inventory is the starting point for post-quantum migration planning. We use what we find to help you prioritize and sequence your transition.
TRUSTED BY THE FORTUNE 500
4 of 5
Top Global Software Companies4 of 5
Top Financial Services3 of 5
Top Global Ranks3 of 4
Top Energy & UtilitiesWhy Encryption Consulting
Cryptographic Expertise
Encryption Consulting was built on applied cryptography. Knowing what cryptographic assets an organization runs, where they live, and whether they are secure has been central to our work from day one.
Fits Your Stack
CBOM Secure plugs into the security and compliance tools your teams already use. Discovery findings are delivered directly into your SIEM or compliance platforms, with no new systems to learn or manage.
From Discovery to Full Remediation
We do not stop at handing you a list of findings. Our team works with you through assessment, gap analysis, and remediation so the inventory actually leads to a stronger security posture.
Discover Our
Latest Resources
- Blogs
- White Papers
- Videos
Code Signing
Integrating Post Quantum Cryptography into Code Signing Workflows
Discover how to future-proof your code signing workflows with post-quantum cryptography before quantum threats become real. At Encryption Consulting, we specialize in PKI, encryption, and certificates of all types.
Read more
White Paper
The PQC Signature Selection Playbook
Which NIST post-quantum signature fits your code-signing workflow? Compare ML-DSA, SLH-DSA, and draft FN-DSA variants in one practical reference.
Read more
Video
How to Automate Certificate Renewal with BIG-IP F5 Load Balancer
Explore expert insights on cybersecurity, PKI, and post-quantum readiness, with practical guidance to strengthen security and future-proof cryptography.
Watch Now









