Modernizing PKI
Preparing PKI for Scale, Speed,
and What Comes Next.
Build a PKI environment that handles today’s scale, meets tomorrow’s compliance requirements, and does not need to be rebuilt when quantum arrives.
Trusted By
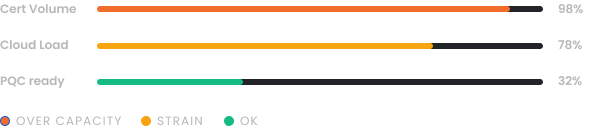
32%
Organizations use a dedicated certificate lifecycle management tool2.6 Hours
Average time to identify a certificate-related outage95%
Organizations face obstacles preparing their PKI for future threats9
Average certificate-related incidents per organization in the past yearTHE PROBLEM
Why PKI Modernization
Keeps Getting Delayed
PKI modernization is one of those projects that every security team knows needs to happen and almost nobody prioritizes until an outage, audit failure, or compliance deadline makes it unavoidable.
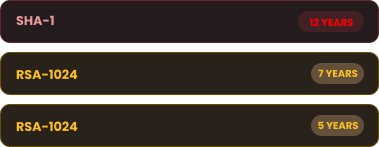
Built for Less
Most enterprise PKI environments were designed for lower volumes, on-prem infrastructure, and a pre-quantum world. That architecture is now carrying a load it was never built for.
No Full Inventory
Before you can modernize a PKI environment, you need to know what is in it. Most organizations do not have a complete view of their CA hierarchy, certificate inventory, or the systems that depend on them.
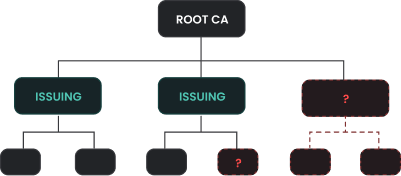
Legacy CAs Are Stuck
Offline root CAs, aging issuing CAs, and unreviewed certificate templates are common in enterprise environments. Replacing them without disrupting dependent systems requires careful planning.
Compliance Requirements
PCI-DSS 4.0, HIPAA, DORA, and other frameworks are placing stricter requirements on how PKI is designed, operated, and documented. PKI environments that were compliant two years ago may not be today.

Quantum Threat
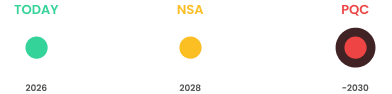
NIST finalized itsinital PQC standards in 2024, and NSA and the European Commission have both set migration timelines. PKI environments not built with post-quantum readiness today will need to be rebuilt within three to five years.
THE STRATEGY
How to Address This
Strategically
PKI modernization is a sequence of changes that need to happen in the right order, with the right planning, so that nothing breaks along the way. The complexity varies significantly across financial services, healthcare, government, and enterprise technology environments, and that variation has to be accounted for from the start.
PKI Assessment
Documenting what exists across the environment is the start. CA hierarchy, certificate templates, key storage, and dependencies must all be mapped before modernization begins.
Fix First, Build Second
Most PKI environments carry misconfigurations, outdated templates, and gaps in certificate governance that must be addressed before modernization can proceed. Attempting to build on top of these issues compounds them.
Design for What Is Coming
The PKI architecture must be designed to handle shorter certificate lifespans, higher issuance volumes, cloud-native workloads, and post-quantum algorithm migration without requiring a full rebuild within a few years.
HSM Integration
Private keys for root and issuing CAs must be protected to the standard regulators and auditors expect. Hardware security module integration into the PKI architecture is a non-negotiable part of any modern deployment.
Managed or Self-Operated
Organizations that want to hand off operational burden need a different delivery model than those that want to operate the infrastructure themselves. Both paths must be available and properly scoped.
This is the approach that Encryption Consulting brings to PKI modernization engagements across financial services, healthcare, government, and enterprise technology.
PKI modernization sounds intimidating, and honestly, for a lot of organizations it is, because their current PKI has years of undocumented decisions baked into it. People have left, things were configured a certain way for reasons nobody remembers - and touching it feels risky. We've been in that room. We know how to untangle it without breaking what's working and build something the organization can actually own and operate going forward.
Products & Services
How We Support
Your Security Journey
HSM-as-a-Service
High Assurance HSM Solution
Secure key storage for your PKI without the cost and complexity of on-premises HSM infrastructure. Purpose-built for root CA and issuing CA key protection.
CertSecure Manager
Certificate Lifecycle Management
Certificate lifecycle management that integrates with your modernized PKI to automate issuance, renewal, and compliance tracking at scale.
PKI Services
Scalable PKI Without Complexities
End-to-end PKI design, assessment, implementation, and migration services for organizations modernizing existing environments or building new ones from scratch.
PKI-as-a-Service
A fully managed, scalable PKI built to modern standards, handling certificate issuance, lifecycle management, and compliance without requiring your team to operate the infrastructure.
PQC Advisory Services
Post-quantum readiness planning built into your PKI modernization roadmap, so the work you do today does not need to be redone when quantum-safe algorithms become mandatory.
TRUSTED BY THE FORTUNE 500
4 of 5
Top Global Software Companies4 of 5
Top Financial Services3 of 5
Top Global Ranks3 of 4
Top Energy & UtilitiesWhy Encryption Consulting
Deep PKI Expertise
PKI modernization is not a side engagement for us. Every consultant we put on a PKI project has hands-on experience designing, building, and fixing PKI environments across regulated industries.
Experience Across Industries
We have modernized PKI environments for mid-size enterprises to Fortune 500 companies across financial services, healthcare, government, and technology. We know the patterns that cause projects to stall and how to avoid them.
Built for a Secure Future
A PKI modernization that does not account for post-quantum cryptography, 47-day certificate lifespans, and increasing automation requirements is not modern. Every environment we design is built to handle what is coming, not just what exists today.
Discover Our
Latest Resources
- Blogs
- White Papers
- Videos
Code Signing
Integrating Post Quantum Cryptography into Code Signing Workflows
Discover how to future-proof your code signing workflows with post-quantum cryptography before quantum threats become real. At Encryption Consulting, we specialize in PKI, encryption, and certificates of all types.
Read more
White Paper
The PQC Signature Selection Playbook
Which NIST post-quantum signature fits your code-signing workflow? Compare ML-DSA, SLH-DSA, and draft FN-DSA variants in one practical reference.
Read more
Video
How to Automate Certificate Renewal with BIG-IP F5 Load Balancer
Explore expert insights on cybersecurity, PKI, and post-quantum readiness, with practical guidance to strengthen security and future-proof cryptography.
Watch Now









