PQC Readiness
Preparing Enterprise Cryptography for
Post-Quantum Security
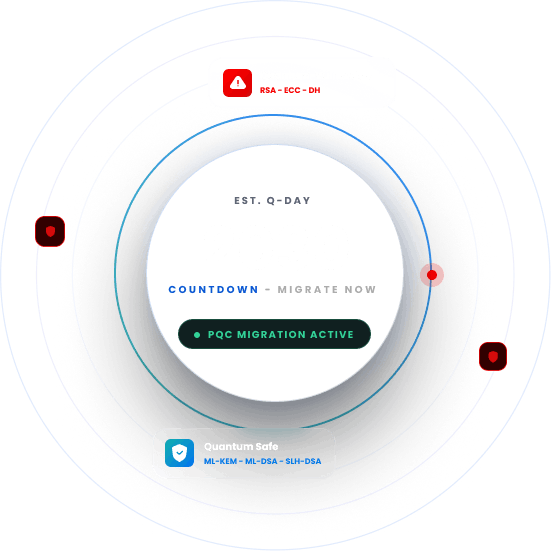
NIST finalized post-quantum standards in 2024. The deadlines are set. The algorithms are chosen. The one thing standing between most organizations and a successful transition isn’t technology, it’s not knowing what they’re working with.
Trusted By
PQC Readiness: Key Statistics
2030
Estimated arrival year for Q-day59%
Lack the expertise to assess, plan, and implement crypto-agility8.6%
Of the top 1 million websites support hybrid PQC92%
Expect to increase investment in PQC.THE PROBLEM
Why Organizations Struggle
with PQC Readiness
Despite public deadlines and finalized standards, most organizations have not made meaningful progress on PQC migration. The reasons are consistent across industries.
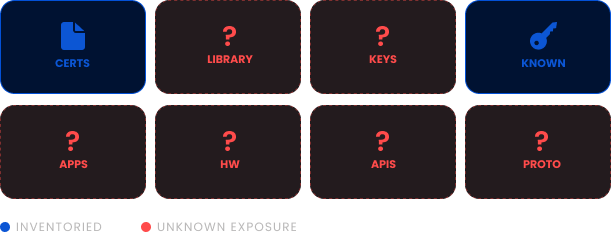
No Cryptographic Inventory
Most organizations lack a complete inventory of cryptographic assets, making it impossible to assess exposure or prioritize migration work.
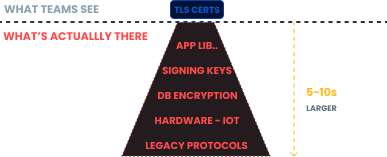
Scope Is Underestimated
Cryptography is embedded across applications, infrastructure, libraries, and hardware. The scope of what needs to change is consistently larger than initial estimates.
Two Transitions at the Same Time
The PQC migration and the 47-day TLS mandate are running concurrently. Treating them separately ends up duplicating work on the same underlying infrastructure.

Skills Gap
Algorithm selection, migration sequencing, and implementation validation require specialized cryptography expertise most internal teams don't have.

Harvest Now, Decrypt Later (HNDL)
Adversaries are already collecting encrypted data today intending to decrypt it once quantum capability matures, meaning vulnerable data is already at risk.

THE STRATEGY
How to Address this
Strategically?
PQC readiness must be approached as a structured program rather than a single project. The starting point is always cryptographic discovery. Everything else follows from having an accurate picture of what exists and what needs to change.
Cryptographic Discovery and CBOM
A full environment scan is required to produce a Cryptographic Bill of Materials before any migration planning can begin.
Risk Assessment and Prioritization
Systems carrying the highest risk from quantum-vulnerable cryptography must be identified and ranked before a migration roadmap is built.
Algorithm Selection
Post-quantum algorithms must be selected based on NIST standards, performance requirements, and infrastructure compatibility to avoid costly reversals mid-migration.
PKI and Infrastructure Readiness
PKI, HSMs, network infrastructure, and application dependencies must each be assessed and prepared before quantum-resistant algorithms can be deployed.
Migration Execution Support
Each migration phase requires implementation, testing, and validation to be completed correctly before the next phase begins.
This is how Encryption Consulting structures every post-quantum readiness engagement , so migration is a planned transition, not a forced one.
I got into cryptography because I believe privacy is a human right. And post-quantum isn't just a technical milestone, it's a moment where we either get ahead of it as an industry, or we let a generation of sensitive data become readable to whoever has the right machine. Patient records. Financial histories. Private communications. That's real people's lives. That's what's at stake, and that's why we take this work seriously.
Products & Services
How We Support
Your Security Journey?
CBOM Secure
Deterministic cryptographic discovery and inventory that gives organizations the complete picture of their cryptographic environment needed to start PQC migration planning.
PQC Advisory Services
Expert advisory covering algorithm selection, migration sequencing, regulatory alignment, and hands-on support through the transition from current cryptographic standards to quantum-resistant alternatives.
PKI Services
PKI assessment, design, and migration services to ensure your PKI infrastructure is ready to issue and manage post-quantum certificates as standards become mandatory.
HSM-as-a-Service
Hardware security module infrastructure that supports post-quantum algorithm storage and operations, without the cost and complexity of managing on-premises HSM hardware.
Encryption Advisory Services
Strategic cryptographic advisory to assess your overall security posture, identify quantum vulnerabilities, and build a roadmap that coordinates PQC migration alongside other cryptographic changes happening at the same time.
TRUSTED BY THE FORTUNE 500
4 of 5
Top Global Software Companies4 of 5
Top Financial Services3 of 5
Top Global Ranks3 of 4
Top Energy & UtilitiesWhy Encryption Consulting?
Deep PQC Expertise
Knowing which algorithms NIST standardized is the starting point. Selecting the right ones for each use case, sequencing migration across interdependent systems, and validating implementations correctly requires hands-on cryptography experience. That is what we bring.
Start With What You Have
Most PQC migrations stall because organizations plan without knowing what they are actually working with. We start with cryptographic discovery so the plan reflects what is in your environment, not what your team assumes is there.
PQC and CLM Together
The 47-day certificate mandate and PQC migration need the same foundations: cryptographic visibility, PKI infrastructure, and automation. We plan both together so nothing gets built twice.
Discover Our
Latest Resources
- Blogs
- White Papers
- Videos
PKI
PKI Maintenance and Quarterly Cleanup for Microsoft CA
Learn how to perform PKI maintenance and quarterly cleanup for Microsoft CA, including CA database backup, certificate cleanup, offline compaction, and post-maintenance validation.
Read more
White Paper
Introduction to Code Signing
Learn the fundamentals of code signing, from digital signatures and certificate validation to time-stamping and application reputation. Discover how to secure your software supply chain, protect against tampering, and build long-term trust across enterprise and consumer environments.
Read more
Video
The 2026 Guide to Upgrading Enterprise PKI and HSMs for Post Quantum Security
Explore expert insights on cybersecurity, PKI, and post-quantum readiness, with practical guidance to strengthen security and future-proof cryptography.
Watch Now