Security is of utmost importance in the dynamic world of virtualization and IT infrastructure. Virtual appliance security is becoming more and more important as virtualization technologies continue to play a major role in datacenters. The signature of OVAs and OVFs is a vital component of this security. We will explore the what, why, and how of this critical security practice as we dig into the world of OVA and OVF signing in this post.
What is OVA and OVF?
Before we dive into the importance of signing OVA and OVF files, let’s understand what OVA and OVF are to wrap our heads around this more easily.
OVF (Open Virtualization Format)
OVF is an open standard for packaging and distributing virtual machines. In addition to specifying the open-source standard, OVF is also the name of a file type used in the standard. A set of OVF files describe a virtual machine’s configuration, virtual disks, and other related information.
OVA (Open Virtualization Appliance)
In addition to the OVF file type, there is also an OVA filetype specified by the standard. Unlike OVF, OVA is a single file that describes the virtual machine’s configuration, virtual disks, and other related information. Simply it’s a TAR format archive of OVF files. This can make signing much more straightforward streamlined and therefore, convenient.
The Need for OVA and OVF Signing
-
Ensuring Authenticity
The first and foremost need for OVA and OVF signing is to guarantee the authenticity of virtual appliances. In a world where virtual appliances can be distributed from various sources, it’s crucial to ensure that what you are deploying is genuinely coming from the claimed source. Without proper signing, there is no way to verify the origin of the virtual appliance. This lack of authenticity can lead to several security risks:
-
Man-in-the-Middle Attacks
Attackers could intercept a virtual appliance during the download process and replace it with a malicious version. OVA and OVF signing helps prevent such attacks by allowing users to verify the authenticity of the appliance.
-
Phishing and Spoofing
Malicious entities may create fake virtual appliances that imitate legitimate ones, tricking users into deploying them. With signing, users can distinguish between authentic and counterfeit packages.
-
-
Preventing Unauthorized Modifications
OVA and OVF signing ensures that a virtual appliance has not been tampered with or altered in any way since it was initially signed by the trusted entity. This is crucial because, without such assurance, attackers could modify the virtual appliance to introduce vulnerabilities, backdoors, or malicious code. Unauthorized modifications can lead to various security problems:
-
Data Breaches
If attackers can modify a virtual appliance to leak sensitive data, your organization could suffer a severe data breach.
-
Disruption of Service
Unauthorized changes can lead to system instability, causing service disruptions and downtime.
-
Infection with Malware
Attackers may insert malware into tampered virtual appliances, compromising the integrity of your entire IT environment.
-
-
Protecting Against Malware
Malware can infiltrate your infrastructure through seemingly harmless virtual appliances. By signing OVA and OVF files, you add an extra layer of defense against malware injection. Here’s how OVA and OVF signing contributes to this protection:
-
Malware Detection
When a virtual appliance is signed, it creates a baseline that represents its original, trusted state. Any alterations to the appliance will invalidate the signature, signalling a potential compromise.
-
Malware-Free Assurance
Users can have confidence that the virtual appliances they deploy have not been compromised with malware, reducing the risk of spreading infections throughout the network.
-
Proactive Security
OVA and OVF signing is a proactive approach to security, allowing organizations to identify and address potential threats before they become critical issues.
-
-
Regulatory Compliance
Many industries and organizations are subject to stringent security and compliance requirements. OVA and OVF signing helps meet these obligations by providing a verifiable trail of trust. Compliance regulations often demand the following:
-
Data Integrity
Regulations frequently require organizations to ensure the integrity of data and software components. OVA and OVF signing helps maintain the integrity of virtual appliances, demonstrating adherence to these regulations.
-
Auditing and Accountability
Compliance standards may necessitate organizations to maintain audit trails, proving the authenticity and source of virtual appliances. OVA and OVF signing simplifies this process.
-
Data Privacy
Protecting sensitive data is a common requirement in compliance standards. OVA and OVF signing aids in ensuring that virtual appliances do not compromise data privacy by preventing unauthorized access or data leaks.
-
Building a Chain of Trust
Building a Chain of Trust is a meticulous process that involves the selection and management of trusted entities, secure key management, compliance, and auditing. The strength of this chain directly impacts the level of trust you can place in digitally signed assets, such as OVA and OVF files.
-
Certificate Authorities (CAs)
Certificate Authorities are trusted third-party entities responsible for issuing digital certificates. These certificates link a public key to an entity, affirming that the entity is who they claim to be. In the context of OVA and OVF signing, CAs play a pivotal role. Considerations include:
-
Selection of Trusted CAs
CAs should adhere to strict verification and compliance standards to maintain trustworthiness. They must ensure that the entities they issue certificates to are legitimate and meet certain security and identity criteria.
-
Verification and Compliance
CAs should adhere to strict verification and compliance standards to maintain trustworthiness. They must ensure that the entities they issue certificates to are legitimate and meet certain security and identity criteria.
-
-
Root of Trust
The root of trust is the highest level of trust in the Chain of Trust hierarchy. It acts as the ultimate authority, and all trust flows from this point. Considerations regarding the root of trust include:
-
Security of the Root CA
The Root CA must be securely maintained. Any compromise of the Root CA would undermine the trust of the entire chain. Security measures, both physical and digital, should be in place to protect the Root CA.
-
Geographical Distribution
To further enhance security, organizations may use multiple, geographically distributed Root CAs. This can provide redundancy and protect against single points of failure.
-
-
Intermediate CAs
Intermediate CAs are entities that bridge the gap between the root of trust and end-entity certificates. They issue certificates on behalf of the Root CA. Considerations include:
-
Secure Communication
Communication between the Root CA and intermediate CAs must be secure to prevent any potential compromise in the transmission of certificates.
-
Limited Scope
Intermediate CAs typically issue certificates for specific use cases or domains. Ensuring that intermediate CAs have a limited scope helps control the overall security of the chain.
-
Regular Auditing
Periodic audits of intermediate CAs can help maintain trust. Organizations should regularly verify that these CAs are adhering to security and compliance standards.
-
-
End-Entity Certificates
End-entity certificates are the certificates issued to the actual entities that sign digital assets such as OVA and OVF files. These certificates form the basis for verifying the authenticity and integrity of virtual appliances. Considerations for end-entity certificates include:
-
Key Pair Security
End entities must securely generate and store their public-private key pairs. The private key, used for signing, must be well-protected.
-
Certificate Renewal
Certificates have a limited lifespan, and they need to be renewed periodically. Renewal must be a well-organized process to avoid gaps in trust.
-
Auditing and Compliance
End-entity certificate holders should ensure that they comply with security and compliance standards. Auditing may be required to maintain their legitimacy in the chain.
-
-
Verification and Trust Path
The recipients of digitally signed assets, such as virtual appliances, use the Chain of Trust to verify the authenticity and integrity of the asset. The verification process follows these steps:
-
Obtaining the Public Key
The recipient obtains the public key of the entity that signed the asset. This public key is part of the end-entity certificate.
-
Checking the Signature
The recipient verifies the digital signature on the asset using the obtained public key.
-
Traversing the Chain
If the signature is valid, the recipient’s system traces the trust path back to the root of trust to ensure that each certificate in the chain is valid.
-
Root Trust
Once the trust path is successfully traversed, the recipient has confidence in the authenticity and integrity of the digital asset.
-
Challenges and Considerations
While OVA and OVF signing offers robust security, it’s important to be aware of certain challenges and considerations:
-
Key Management
Managing cryptographic keys is a fundamental challenge in the world of OVA and OVF signing. The secure generation, storage, and distribution of keys are critical. Here’s why:
-
Key Security
The private keys used for signing virtual appliances must be kept highly secure. Any compromise of the private key can lead to unauthorized signing and modifications.
-
Key Rotation
Regularly rotating keys is a good security practice. However, key rotation can be complex, especially in large-scale environments. Administrators must ensure that old keys are securely retired, and new keys are distributed effectively.
-
Key Recovery
In the event of key loss or compromise, a plan for key recovery must be in place. Without a recovery plan, data or virtual appliances signed with the lost key may become inaccessible.
-
-
Revocation
The ability to revoke keys or certificates is essential in the event of key compromise or other security incidents. Revocation mechanisms are necessary to ensure the continued trustworthiness of virtual appliances. Considerations include:
-
Timely Revocation
Certificates must be revoked in a timely manner once they are compromised. Delays in revocation could expose systems to vulnerabilities.
-
CRL and OCSP
Revocation information is often managed through Certificate Revocation Lists (CRL) and Online Certificate Status Protocol (OCSP). These mechanisms must be effectively maintained to ensure that revoked certificates are recognized by relying parties.
-
Efficient Communication
The process of revocation must be effectively communicated to all relevant parties to prevent the use of compromised certificates or keys.
-
-
Root of Trust
The root of trust, often managed by a certificate authority (CA), is the highest level in the certificate hierarchy. It’s the foundation of the trust chain. The considerations related to the root of trust include:
-
Root Trustworthiness
The trustworthiness of the Root CA is paramount. If the Root CA is compromised, the entire trust chain built upon it is at risk. Organizations must carefully select and monitor Root CAs.
-
Distributed Roots
In some cases, relying on a single Root CA may be risky. Organizations may consider using multiple, geographically distributed Root CAs to enhance security.
-
-
Usability
Balancing security with usability is a challenge. Excessive security measures can make the user experience complex and frustrating. Considerations in this regard include:
-
User-Friendly Interfaces
Implementing user-friendly tools and interfaces for managing certificates and verifying signatures can help mitigate the challenges of usability. If the process is too complicated, users may be tempted to bypass security measures.
-
Automated Processes
Wherever possible, automate certificate management and signature verification processes to reduce the burden on users and administrators.
-
-
Standardization
The OVA and OVF signing process should follow standardized protocols and formats to ensure interoperability and compatibility. This includes:
-
Interoperability
Ensure that OVA and OVF files signed with one tool or platform can be verified by others, promoting cross-platform compatibility.
-
Standard Formats
Adhering to standard formats and protocols helps in the consistent implementation of OVA and OVF signing practices.
-
Cross-Platform Support
Ensure that OVA and OVF signing tools are compatible with various virtualization platforms, operating systems, and certificate authorities.
-
-
Resource Overhead
Implementing OVA and OVF signing adds a certain degree of resource overhead. Considerations in this context include:
-
Computational Resources
The process of signing and verifying can be resource-intensive, especially in large-scale environments. Ensuring that systems have adequate computational resources to handle the load is essential.
-
Time and Latency
The signing and verification process can introduce latency. In time-sensitive environments, this delay needs to be minimized to avoid performance issues.
-
Storage and Bandwidth
Signed virtual appliances may have larger file sizes due to added signature data. Ensure that sufficient storage and bandwidth are available for distribution and deployment.
EC’s Code signing solution for OVA/OVF files
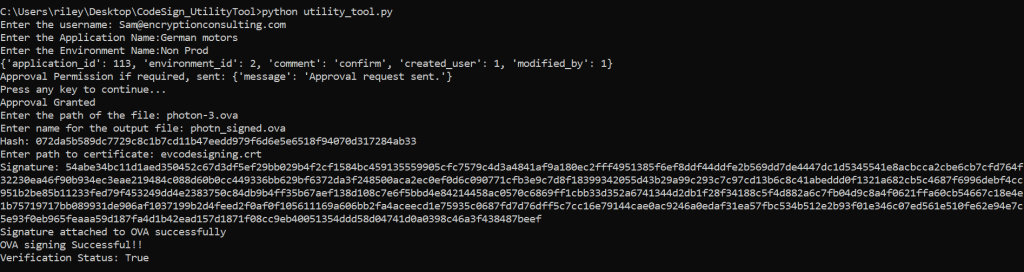
Encryption Consulting(EC) understands the need for security in the modern world and strives to solve these problems through CodeSign Secure. To that end, we have developed an easily operated command-line Utility that provides users with seamless and hassle-free OVA/OVF signing.
CodeSign Secure’s Utility tool is designed for high performance, accuracy and user-friendliness in mind, making signing of OVA/OVF files simplified for the users.
How to sign OVA/OVF files?
Now that we understand why OVA and OVF signing is crucial, let’s explore the actual process.
-
Necessary input
The user needs to give all the input data, mentioned below, to the utility tool for the signing process.
-
Username
The primary email of the user to proceed with the signing process.
-
Certificate path
The path to the certificate being used for signing the desired file.
-
Input file path
The path to the OVA/OVF file that needs to be signed.
-
Output file path
The path to the signed OVA/OVF output file.
-
Application name
Application name is the application associated with the certificate used for signing in our web portal.
-
Environment
The environment name, whether it’s production, non-production, Lab, or any specific environment created by the user in our web portal.
-
-
Acquiring an End-Entity Certificate
To sign the OVA or OVF file, the user needs an end-entity certificate. This certificate can be generated from our web application, or can be imported into the utility tool. We prefer importing EV certificate(Extended Validation) certificate as it is the highest form of SSL Certificate on the market.
-
Generating a Hash
Client-side Hashing is used to calculate the hash of the file that is to be signed. This hash is sent to the server along with the private key alias to generate signature .
-
Generating and attaching the Signature
Signature is generated in the HSM by using the hash and the private key and this digital signature is sent back to the client. Once client receives the signature it is attached to the OVA or OVF package.
- We strictly adhere to the CA/B Forum guidelines, ensuring that we maintain the highest standards in the industry.
- We go the extra mile by utilizing FIPS 140/2 level 3 compliant Hardware Security Modules (HSMs). With us, your private key is generated and securely stored within the HSM, ensuring that it never leaves the module. This guarantees the impossibility of a private key compromise.
Client-Side hashing is an extra step that is implemented from our end to ensure more secure transfer of data between client and server. Client-side hashing ensure even if the packet is intercepted the attacker get just the hash which is useless of the attacker.
Client-Side hashing provides a significant advantage in terms of remote digital signature generation, reducing the overall bandwidth requirement due to only hash value upload, and avoiding the attacks of malicious code signed due to no code file movement within the environment.
Why to go with us?
Encryption Consulting’s Utility tool keeps strict compliance with latest security guidelines. Utility tool showcases some security features that ensure we are a step ahead in securing the files.
The following features make CodeSign Secure’s Utility tool a trustworthy vector for your code signing endeavours.
Conclusion
In today’s digital landscape, securing virtual appliances is of utmost importance. The techniques required to create confidence and guarantee the integrity of virtual appliances are provided by OVA and OVF signing. Organizations may confidently deploy virtual appliances, protecting their IT infrastructure from potential threats and compliance challenges, by utilizing cryptographic signatures, PKI, and a chain of trust. Adopting OVA and OVF signing is essential for data center security and virtualization, not just as a best practice.
Our ambition at Encryption Consulting is to provide tools that enable a more secure environment. We are aware of the crucial function that file signing plays in providing protection from unanticipated events. We have an unrelenting dedication to your security, and we’re here to give you the knowledge and resources you need to safeguard what matters most.
To learn more about CodeSign Secure, the ultimate code signing tool you need, request a demo now!