Organizations need to secure keys and secrets, and their data is increasing exponentially. The demand for high-level security for that is at its peak now. For most organizations, automation of key lifecycle management is ideal because the lifecycle of cryptographic keys also calls for a high level of management. HSMs, or hardware security modules, are the mainstay in this scenario. Hardware security module (HSM) adds additional security for sensitive data. Before diving into HSM as a Service, let’s briefly discuss what HSM is and how it works.
What is HSM, and how does it work?
Hardware security modules (HSMs) are fortified, tamper-resistant hardware components that produce, safeguard, and manage keys for encrypting and decrypting data and establishing digital signatures and certificates. This secures cryptographic procedures. To the highest security requirements, including FIPS 140-2 and Common Criteria, HSMs have been evaluated, verified, and certified. HSMs are extremely difficult to breach and have highly regulated access, which is one of the reasons they are so secure.
For constructing tamper-resistant, hardened environments for storing cryptographic keys, HSMs act as trust anchors. An HSM can serve as the ideal Root of Trust in any organization’s security infrastructure thanks to the stringent security procedures implemented inside it. They have the specialized gear to generate high-quality random keys. Multiple organizations use more than one HSM to secure their environment instead of just one. A simplified, central key management system founded on stringent internal security standards and external laws enhances security and compliance regardless of how many HSMs are deployed.
To further protect against breaches, HSMs are often kept off the organization’s computer network. An attacker would need physical access to the HSM to view the protected data.
HSM as a Service
A top priority is creating an encryption key management and maintenance plan, especially if you want to keep your HSMs operating at peak efficiency throughout each encryption certificate. To fully actualize secure techniques for data security, this includes managing your encryption keys over private and public networks and hybrid mixes of physical and cloud-based HSM functions. It would help if you established uniformity around the board to successfully navigate the difficulties of switching to HSM as a Service.
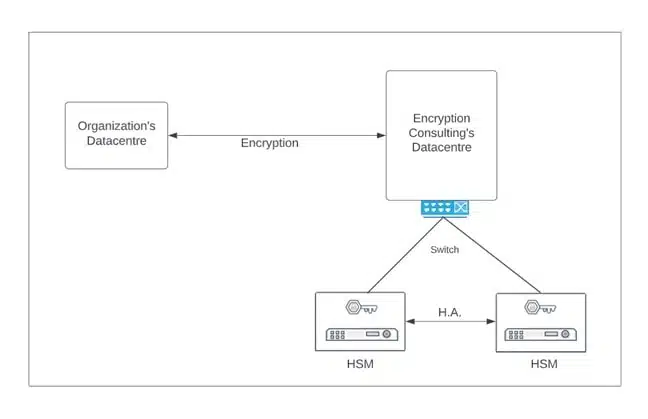
EC’s HSM as a Service
The HSM as a Service from Encryption Consulting offers the highest level of security for certificate management, data encryption, fraud protection, and financial and general-purpose encryption. It is globally compatible, FIPS 140-2 Level 3, and PCI HSM approved. It offers customizable, high-assurance HSM Solutions (On-prem and Cloud) designed and built to the highest standards. We are Vendor- agnostic and provide various options, whichever is best for you to deploy. We ensure Highest Availability around the world and supply our services across the globe.
Encryption Consulting’s HSM-as-a-Services are suitable for the following:
- Customers who already have HSM deployed in place.
- Customers who are planning for new HSM infrastructure (Designing and Deploying)
Being a Vendor-agnostic Organization, we give it upon the customer to implement whichever HSM they want by providing various options:
-
Entrust N-shield HSM
nShield HSMs provide a secure solution for encryption and signing keys, creating digital signatures, encrypting data, and more. N-shield as a Service gives the advantages of a cloud service deployment with the same features and capability as on-premises HSMs.
-
Thales Luna 7 HSM
Thales Luna Network HSMs secure your sensitive data and critical applications by storing, protecting, and managing your cryptographic keys with high-assurance, tamper-resistant, network-attached appliances offering market-leading performance.
-
FutureX HSM
FutureX hardware security module solutions provide robust encryption, tamper resistance, and logical security to safeguard your most sensitive data. Key lifecycle management, payment encryption, and general encryption are all handled by Futurex HSMs.
For HSM, we provide both varieties of solutions:
Dedicated HSM
Azure Dedicated HSM offers storage for cryptographic keys. Dedicated HSM meets the most demanding security requirements.
- Organizations who require FIPS 140-2 Level 3-validated devices and total and exclusive control over the HSM appliance should choose this option.
- Microsoft uses Thales Luna 7 HSM model A790 appliances to supply the Dedicated HSM service.
- They are directly deployed to a client’s private IP address space.
- Single-tenant devices.
- Full administrative control and High Performance.
- Azure Dedicated HSM is most suitably used in migration scenarios.
Managed HSM
Azure Managed HSM is a fully managed, highly available, standards-compliant cloud service that enables you to safeguard cryptographic keys for your cloud applications.
- Uses FIPS 140-2 Level 3 validated devices.
- Your keys are safeguarded using Marvell LiquidSecurity HSM adapters while using Managed HSMs.
- Single-tenant devices.
- Supports Import keys from your on-premises HSMs.
Advantages of HSM as a Service
- Systems that are exceptionally safe against tampering include tamper-evident, tamper-proof, and tamper-resistant systems.
- Can implement on both On-premises and Cloud with scalability and versatility.
- Maintain complete control over key materials regardless of where application workloads occur.
- Leveraging numerous clouds to expand cloud-based cryptography and key management.
- With a single click, services may be automatically scaled, reducing the administration burden.
- When necessary, enables the creation and application of rules to ensure compliance
EC Managed HSMaaS
Encryption Consulting LLC (EC) will completely offload the HSM environment, which means EC will take care of deploying the HSM environment to lead and manage the HSM environment (cloud/ hybrid or On-Prem) of your organization. For more information, visit our website or contact us via email.
Conclusion
Hardware Security Module (HSM) is a specialized, highly trusted physical device used for all the main cryptographic activities, such as encryption, decryption, authentication, key management, key exchange, and more. EC’s HSMaaS provides a variety of options for HSM deployment as well as management. Dedicated HSM is used widely in migration scenarios, whereas Managed HSM supports importing keys from your on-prem HSMs. Advantages include security, scalability, versatility, full control, and more. Do visit our website or contact us for more information.