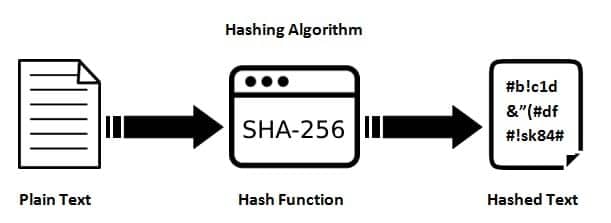
SHA, which stands for Secure Hash Algorithm, is a family of cryptographic hash functions designed by the National Security Agency (NSA) and published by the National Institute of Standards and Technology (NIST) in the United States. It is part of the larger family of hash functions used for various cryptographic applications.
Introduction of SHA-256
SHA-256, part of the SHA-2 algorithm family, is a Secure Hash Algorithm introduced collaboratively by the NSA and NIST in 2001. It emerged as a robust successor to the SHA-1 family, which faced increasing vulnerabilities to brute force attacks.
The “256” in SHA-256 signifies its fixed hash digest size, always producing a 256-bit value, regardless of the input plaintext or cleartext size. This characteristic ensures consistent and strong cryptographic hashing.
Within the broader SHA family, SHA-256 shares similarities with its counterparts. Its development marked a crucial milestone in cryptography, addressing security concerns prevalent in earlier algorithms like SHA-1.
How does it work?
We want to hash the message “Hello, SHA-256!” using SHA-256. Here are the steps:
-
Message Padding
The ASCII representation of “Hello, SHA-256!” is converted to binary: 01001000 01100101 01101100 01101100 01101111 00101100 00100000 01010011 01001000 01000001 00101101 00110010 00110011 00110110 00100001. Append a ‘1’ bit to the end of the message: 01001000 01100101 01101100 01101100 01101111 00101100 00100000 01010011 01001000 01000001 00101101 00110010 00110011 00110110 00100001 1.
(Note: The actual padding involves more than adding a ‘1’ bit, including appending the original message length, but this is simplified for illustration.)
-
Initialization
The initial hash values (eight 32-bit words) are set. These values are defined in the SHA-256 specification.
-
Processing in Blocks
Divide the padded message into 512-bit blocks. For each block, perform a series of bitwise operations, modular additions, and logical functions using the current hash value and the block.
-
Compression Function
A compression function is applied to each block, creating a new hash value. This function involves mixing the bits of the current hash value and the message block.
-
Iteration
Repeat the compression function for each block, using the output of each iteration as input for the next.
-
Output
The final hash value after processing all blocks becomes the SHA-256 hash of the original message.
In reality, this process involves many complex bitwise operations and transformations. The resulting SHA-256 hash for our simplified example would be a 256-bit hexadecimal string.
Where can it be implemented?
SHA-256, a cryptographic hash function, finds applications in various areas where data integrity and security are crucial. Here are some common implementations:
-
Digital Signatures
SHA-256 is often used with public-key cryptography to create digital signatures. It allows for the verification of the integrity and authenticity of digital messages or documents.
-
Blockchain Technology
SHA-256 plays a fundamental role in blockchain technology. It generates the hash values of blocks in a blockchain, ensuring the immutability and integrity of the entire chain.
-
Password Hashing
In secure password storage, systems store the SHA-256 hash of the password instead of storing the actual password. This enhances security by preventing exposure to plain-text passwords in case of a data breach.
-
Secure Communication
Hash functions like SHA-256 are used in secure communication protocols to ensure the integrity of transmitted data. For example, in TLS/SSL protocols, hash functions are used with digital signatures to provide secure communication over the Internet.
-
Certificate Authorities (CAs)
SHA-256 is commonly used to create and verify digital certificates issued by Certificate Authorities. It helps ensure the authenticity and integrity of these certificates.
-
File Integrity Checking
SHA-256 generates checksums or hash values for files. Users can then verify the integrity of files by comparing the computed and original hash.
Advantages and Disadvantages
| Advantages | Disadvantages |
|---|---|
| SHA-256 ensures data remains unchanged during transmission. | Once data is hashed, it cannot be reversed or decrypted to retrieve the original data. |
| SHA-256 provides a high level of security, making it practically impossible to derive the original data from its hash value. | Although rare, there is a theoretical possibility of hash collisions, where two different inputs produce the same hash value. |
| SHA-256 is a cornerstone of blockchain technology, ensuring the integrity and immutability of blocks. | Being deterministic, the same input will always produce the same hash, which may lead to potential vulnerabilities in some scenarios. |
| SHA-256 computations are relatively fast on modern hardware. | While SHA-256 has a high resistance to collision attacks, its resistance to pre-image attacks is theoretically less than collision resistance. |

